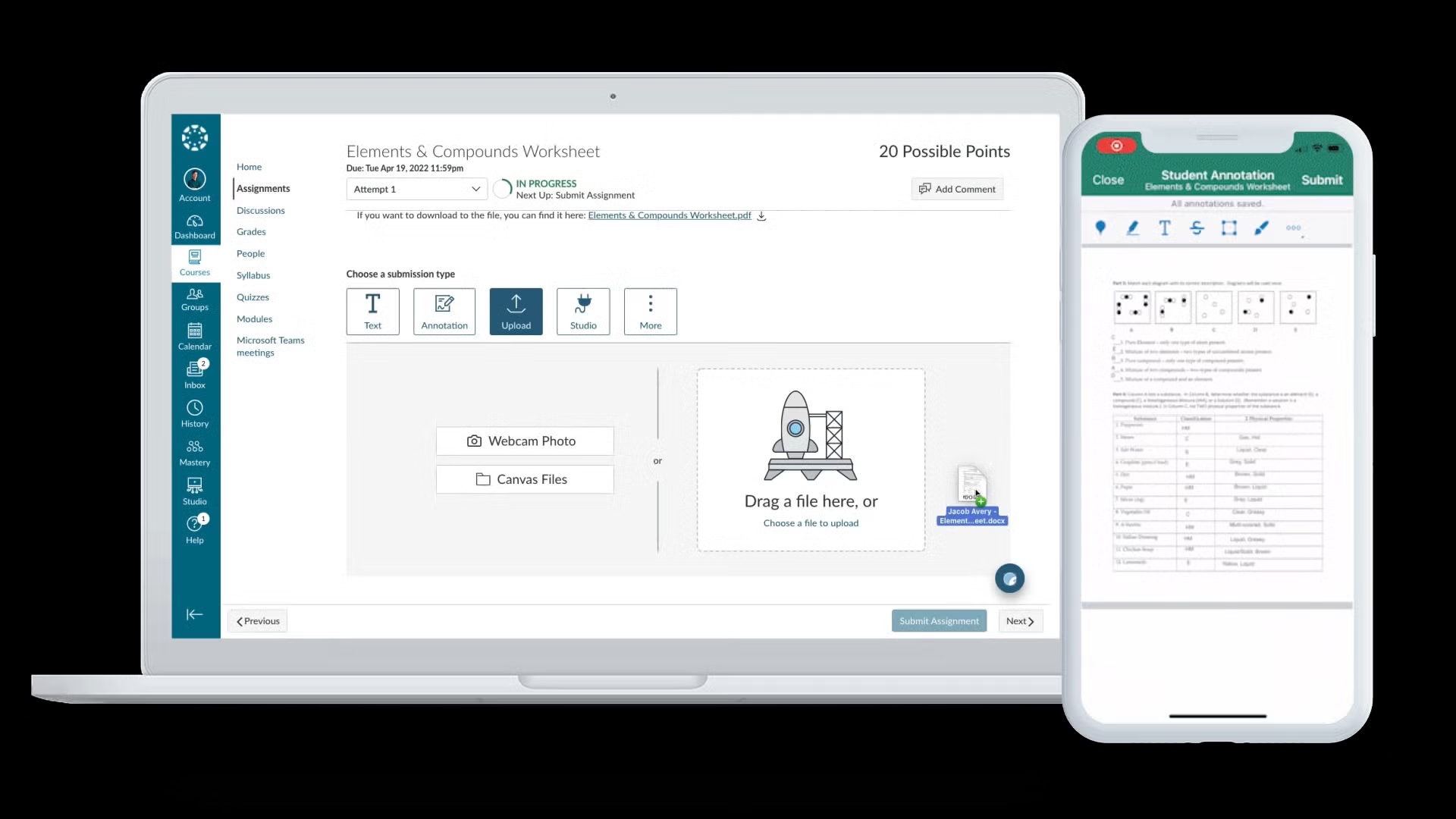
What Happened in the Canvas Data Breach?
Instructure, the company behind the Canvas learning platform, recently confirmed a major edtech security incident involving the cyber extortion group ShinyHunters. The attackers exploited a vulnerability linked to Canvas’s “free-for-teacher” accounts, gaining access to the cloud-based system used by thousands of institutions. Instructure detected suspicious activity in late April and again in early May, as universities reported widespread service disruptions right in the middle of exam season. Some students even encountered ransom notes on their screens during online assessments, forcing emergency postponements. ShinyHunters claimed to have stolen 280 million records and 3.5 terabytes of data, threatening to leak billions of private messages between students and teachers. The hack temporarily paralyzed Canvas services at roughly 9,000 institutions, highlighting how deeply embedded the platform is in academic life and how dependent teaching and assessment processes have become on a single edtech provider.
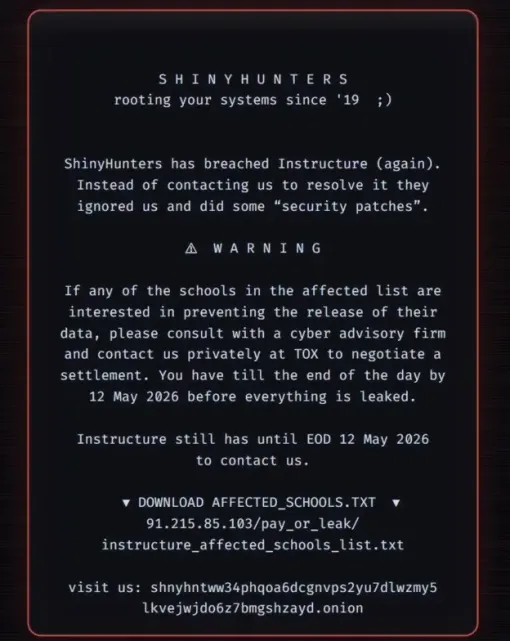
The Ransom Settlement and Why It Is Controversial
Under pressure from institutions needing Canvas back online, Instructure reached a ransom settlement with ShinyHunters. The company says the cybercriminals returned stolen data, deleted copies and agreed not to extort affected universities or individuals further. Instructure also stated it obtained “digital confirmation of data destruction” and framed the decision as a way to give customers additional peace of mind. However, law enforcement agencies worldwide caution against paying ransoms, arguing that such payments fuel the cybercrime ecosystem and provide no technical guarantee that data is truly destroyed. Investigations into other groups, like LockBit, show that attackers sometimes retain copies of data even after receiving payment. Security experts note that ShinyHunters timed the attack to coincide with exam season, maximizing leverage over institutions. The incident raises difficult questions about whether edtech platforms should ever pay ransom and how they balance business continuity with long-term student data protection.

What Data Was Compromised and Who Was Affected?
Instructure has acknowledged that the stolen information includes user-identifying data such as names, email addresses, messages and student ID numbers from affected institutions. ShinyHunters claimed responsibility for accessing data linked to more than 8,800 organizations, with universities reporting outages and disruptions as systems were locked or taken offline. The group also threatened to leak several billions of private messages between students and teachers, underscoring the sensitive nature of the content stored on Canvas. While Instructure says it has restored services and reported the breach to relevant cybersecurity and law enforcement authorities, the precise scope of what was accessed at each institution can vary. Students, lecturers and administrative staff whose learning, communication or assessment activities run through Canvas should assume that core profile details, course communications and possibly assessment-related messages may have been exposed, even if the attackers now claim to have deleted their copies following the ransom settlement.
Practical Security Steps for Students and Educators
Anyone using Canvas should take concrete steps to protect themselves after this edtech security incident. First, change your Canvas password and avoid reusing it on other services; if you used the same password elsewhere, update those accounts too. Enable multi-factor authentication wherever your institution supports it, so attackers cannot log in with just a password. Be cautious of phishing emails referencing the Canvas data breach, password resets or exam-related issues, especially if they ask you to click links or share personal information. Students and staff should also review their Canvas inboxes and remove sensitive information that does not need to be stored there long term. Where possible, avoid sending highly confidential details via Canvas messages. Finally, monitor institutional announcements, as some universities may offer credit monitoring, require password resets or share additional guidance tailored to their specific exposure and internal security policies.
How Institutions and Edtech Providers Should Respond
For universities and schools, the Canvas data breach underscores the need for stronger governance around third-party platforms that handle student data. Institutions should review their contracts and security requirements with edtech vendors, ensuring clear obligations for incident reporting, vulnerability management and independent security audits. Regularly testing backup and continuity plans is essential so teaching and assessment can continue if a learning management system goes offline. Security teams should also limit the use of high-risk features, such as open or “free-for-teacher” accounts, or enforce stricter controls around them. More broadly, this ransom settlement highlights the strategic risk of overreliance on a single platform. Institutions may want to diversify critical systems or maintain offline contingencies for high-stakes exams. Finally, boards and senior leaders should treat cyber resilience as part of core academic planning, aligning investments in digital infrastructure with robust protections for student data protection and privacy.