What Happened: Supply Chain Attack and Exposed Certificates
OpenAI’s ChatGPT desktop app for Mac has been caught up in a broader supply chain security incident involving a compromised open-source library. Malware tied to the “Mini Shai-Hulud” attack infected two employee devices via the TanStack npm ecosystem, giving attackers limited access to internal source code repositories. Among the data exposed were Apple code-signing certificates used to prove that Mac apps come from a legitimate developer. These certificates are central to macOS security, enabling systems like Gatekeeper and notarization to decide whether an app should be trusted, launched, or blocked. To contain the risk, OpenAI rotated these certificates and re-signed affected apps, including ChatGPT Desktop, Codex App, Codex CLI, and Atlas. Investigations so far show no evidence that the exposed credentials were used to sign malicious software or distribute malware to users, and no production systems or customer data were compromised.

Why Some Macs Flagged ChatGPT as Malware
Many Mac users recently saw alarming messages that the ChatGPT app was malware and found it moved to the Trash. This wasn’t Apple declaring ChatGPT harmful; it was macOS Xprotect doing its job. Xprotect relies on notarization and code-signing certificates to determine whether an app is genuine. Because of security concerns around a third-party developer tool, OpenAI proactively switched to new certificates and adjusted the process that certifies its macOS apps as legitimate. Older versions of ChatGPT and ChatGPT Atlas, signed with the previous certificates, effectively lost their notarized status. As a result, macOS treated those installs as suspicious and blocked them from running. Importantly, there is no indication that these apps actually contained malware or installed anything malicious. The simplest fix if your Mac flagged ChatGPT is to redownload the app directly from OpenAI so it’s signed and notarized with the new, trusted certificate.

Update Deadlines, Affected Versions, and Platform Impact
Because the exposed signing certificates could theoretically be misused, Apple’s macOS protections will stop trusting apps signed with those old certificates after June 12. That means older releases of ChatGPT Desktop, Codex App, Codex CLI, and Atlas may stop working or receiving updates unless you upgrade. Specifically, ChatGPT Desktop 1.2026.125, Codex App 26.506.31421, Codex CLI 0.130.0, and Atlas 1.2026.119.1 are listed among affected versions. Mac users are being urged to install the latest releases as soon as possible; OpenAI has already been pushing in-app notices with an update deadline. Once updated, your apps will be signed with the new certificates and remain trusted by macOS Gatekeeper and Xprotect. OpenAI says users on other platforms, such as Windows and iOS, do not need to take action at this time, as the incident did not compromise production environments or distribution channels for those platforms.

What OpenAI Found and What It’s Doing Next
OpenAI’s investigation, supported by a third-party digital forensics and incident response firm, concluded that only a limited amount of credential material was exfiltrated from internal code repositories. The company reports no evidence that user data, production systems, or intellectual property were accessed, and no signs that the exposed signing certificates were abused to ship malicious builds. Nonetheless, OpenAI treated the event as a serious OpenAI security breach and accelerated rollout of additional supply chain protections. These include stronger checks on package provenance, tighter CI/CD credential controls, and safeguards in package managers such as minimum release age policies. The two compromised employee devices happened to be outside these newer controls, which allowed the malware in, but that gap is now being closed. OpenAI has also blocked future notarization attempts using the old credentials to prevent attackers from leveraging them for counterfeit ChatGPT Mac security bypass attempts.
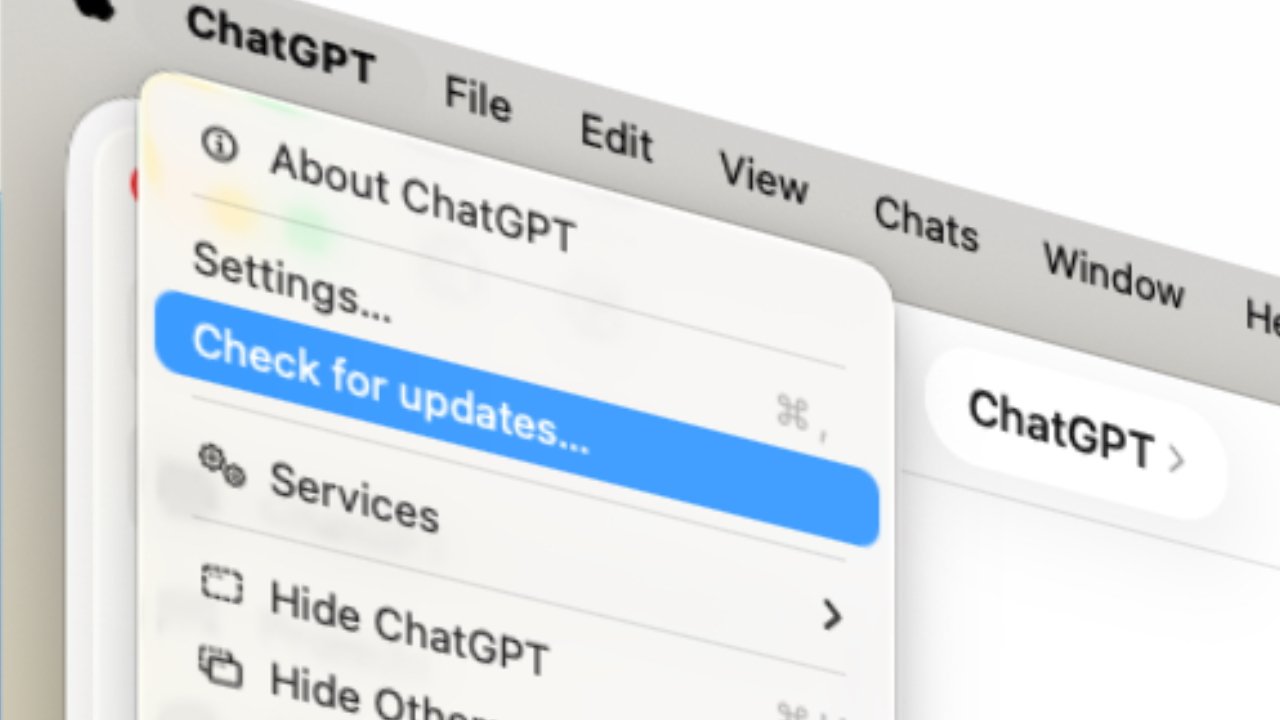
How to Stay Safe: Verify Authenticity and Prevent False Positives
To protect yourself, treat this as a mandatory Mac app security update. First, confirm you’re running the latest version of ChatGPT or other OpenAI desktop apps by using the built-in updater or downloading fresh installers from OpenAI’s official website. Avoid installers from ads, third-party download sites, email attachments, or unsolicited messages, as these are common vectors for real ChatGPT malware false positive lookalikes. If your Mac previously flagged ChatGPT as malware, drag any old copies to the Trash, empty it, and then reinstall from the official source so you get a properly signed and notarized build. Going forward, keep automatic updates enabled where possible and pay attention to security prompts from macOS. By updating before June 12 and sticking to trusted distribution channels, you can continue using ChatGPT on Mac with confidence that your app is legitimate and remains protected by Apple’s security systems.