What Apple Just Released for Older iPhone, iPad, and Mac Models
Apple has rolled out a major batch of Apple security updates that specifically target both current and legacy iPhone, iPad, and Mac operating systems. Alongside the newest platforms, the company has issued patches for older software branches including iOS 18.7.9, iPadOS 18.7.9, iPadOS 17.7.11, iOS 16.7.16, iOS 15.8.8, and several macOS releases such as macOS Tahoe 26.5, macOS Sequoia 15.7.7, and macOS Sonoma 14.8.7. These iPhone iPad Mac patches are not feature updates; they are focused on critical security flaws. Apple’s advisories highlight vulnerabilities in WebKit, kernel components, Wi‑Fi, sandbox protections, privacy systems, and file handling frameworks. Notably, Apple is still maintaining devices dating back to hardware from around 2014–2015 through these legacy OS branches. Even though Apple has not indicated that any of the fixed issues are actively exploited, the company’s decision to push such broad coverage underscores how serious these weaknesses are.

The Critical Security Flaws: WebKit, Kernel, Wi‑Fi, and Sandbox Escapes
The latest Apple security updates address a cluster of critical security flaws that cut across the operating system stack. At the browser level, Apple has delivered a significant WebKit vulnerability fix, closing issues that could allow attackers to bypass Content Security Policy checks, leak sensitive information, corrupt memory, crash Safari, or run malicious code via crafted web content. In the kernel, Apple patched bugs linked to privilege escalation, kernel memory disclosure, integer overflows, race conditions, and out‑of‑bounds writes—issues that could let an attacker execute arbitrary code with system‑level rights. Wireless networking also received urgent attention: one Wi‑Fi vulnerability allowed arbitrary code execution with kernel privileges through a crafted out‑of‑bounds write, while other flaws enabled denial‑of‑service via malicious Wi‑Fi or mDNSResponder traffic. Additional fixes close sandbox escape paths, address Gatekeeper bypasses using disk images or ZIP archives, and tighten privacy around contacts, screen capture, and app data.
Why Legacy Devices Are Especially at Risk If You Delay
Older iPhones, iPads, and Macs tend to stay on the same system version for years, and that makes timely security patching crucial. Many of the latest vulnerabilities impact core components like WebKit, Wi‑Fi, and the kernel—areas that underpin almost everything your device does. If you skip these iPhone iPad Mac patches, malicious websites, crafted files, or hostile apps could exploit critical security flaws to read private information, gain elevated privileges, or escape the sandbox that is meant to contain them. Apple’s continued releases for iOS 16.7.16, iOS 15.8.8, and iPadOS 17.7.11 show that the company knows older hardware still holds sensitive data. These updates even fix subtle privacy issues, such as a Notification Services bug where deleted notifications might remain stored unexpectedly. If your device is so old that it no longer receives any WebKit vulnerability fix or kernel update, you should avoid using it for banking, password management, or other sensitive tasks.
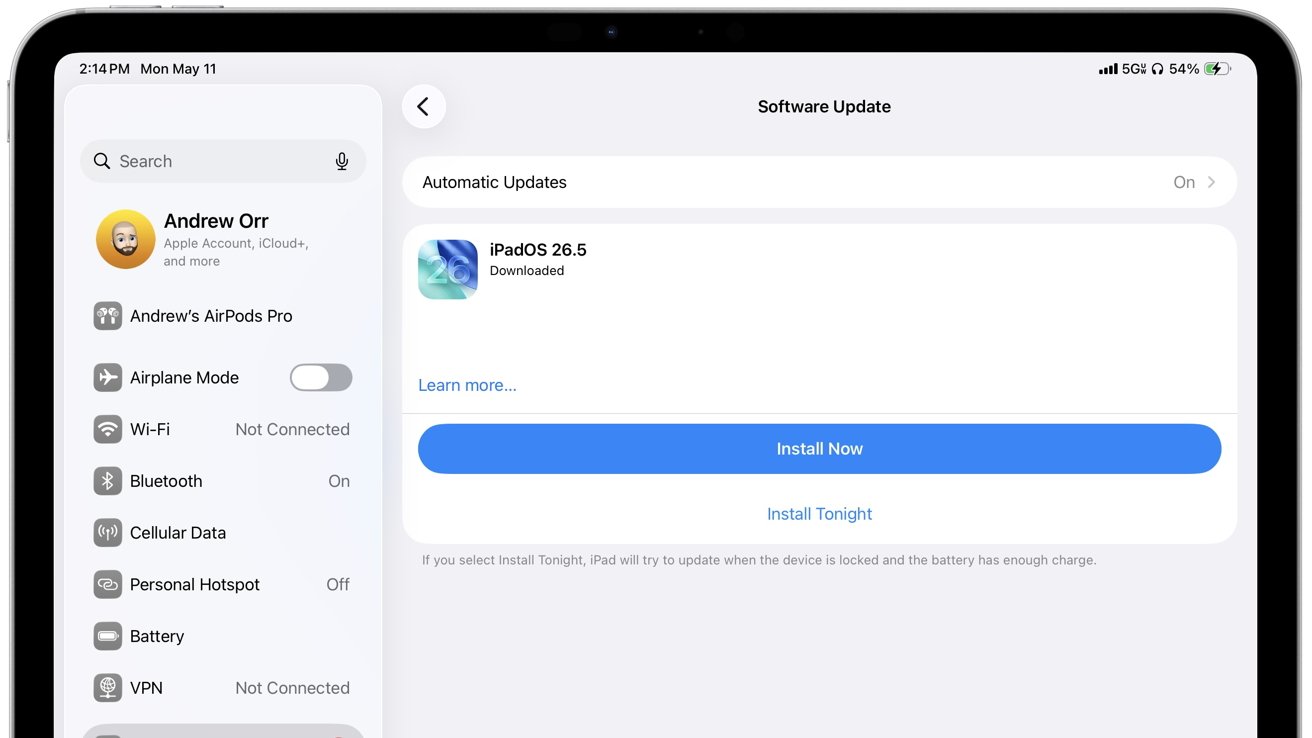
How to Check for and Install Security Updates on iPhone and iPad
To protect your iPhone or iPad, install the latest Apple security updates as soon as possible. First, connect to a trusted Wi‑Fi network and make sure your battery is sufficiently charged or the device is plugged in. Then open Settings, tap General, and choose Software Update. Your device will check Apple’s servers and show the latest version available, such as iOS 18.7.9, iOS 16.7.16, iOS 15.8.8, or the corresponding iPadOS release. Tap Download and Install, enter your passcode if prompted, accept the terms, and allow the download to complete. The device will prepare the update, then restart to apply kernel, WebKit, Wi‑Fi, and sandbox fixes. Do not interrupt this process. After the reboot, return to Software Update to confirm that your device reports it is up to date. If automatic updates are disabled, consider turning them on so future iPhone iPad Mac patches arrive promptly.
How to Update macOS and Reduce Your Exposure to Attacks
On a Mac, installing these patches is just as important, especially because many of the same WebKit and kernel flaws affect macOS. To update, click the Apple menu in the top‑left corner, open System Settings (or System Preferences on older macOS versions), and navigate to Software Update. Your Mac will display the latest compatible release, such as macOS Tahoe 26.5, macOS Sequoia 15.7.7, or macOS Sonoma 14.8.7. Click Update Now or Upgrade Now, review the details, and proceed with the installation. Keep your Mac connected to power and do not close the lid during the process. Once the update finishes and the system restarts, critical security flaws tied to WebKit, Wi‑Fi, sandbox escapes, and privilege escalation will be patched. For added safety, avoid untrusted apps, unknown configuration profiles, suspicious links, insecure Wi‑Fi networks, and unsolicited downloads—common paths attackers use to exploit the kinds of vulnerabilities just fixed.