From Green Bubbles to Secure Channels
With iOS 26.5, Apple is closing one of the biggest gaps in mobile security: unencrypted texts between iPhone and Android. Until now, iMessage conversations enjoyed end-to-end encrypted texting, but chats that fell back to SMS or non‑encrypted RCS were exposed to interception while in transit. The new encrypted RCS messaging support in iOS 26.5 changes that for users with supported carriers and Android contacts using the latest Google Messages app. Apple describes this as part of a cross‑industry effort to replace traditional SMS with a modern, internet‑based protocol that can finally be protected by default. Instead of relying on third‑party chat apps, everyday text conversations can now gain stronger iPhone Android encryption at the system level, significantly improving privacy in mixed‑platform group chats and one‑to‑one messages.
How Default End-to-End Encrypted RCS Works
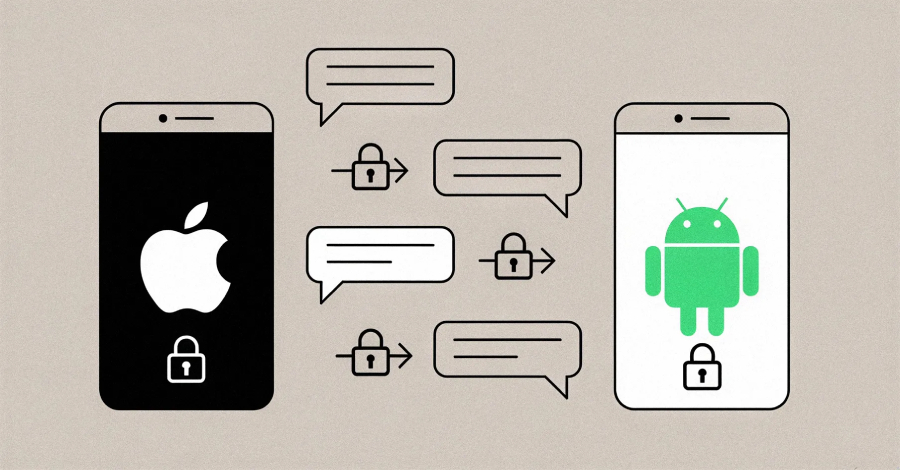
RCS, built on the RCS Universal Profile, is essentially a richer texting standard that runs over the internet rather than the old signaling network used by SMS. It enables high‑resolution media sharing, typing indicators, and read receipts that people are used to from chat apps. In iOS 26.5, Apple has added end‑to‑end encryption to RCS messaging, meaning messages are encrypted on the sender’s device and can only be decrypted on the recipient’s device. According to Apple, when RCS messages are end‑to‑end encrypted, they cannot be read while they are being sent between devices. On iPhone, users will see a new lock icon within RCS conversations to confirm encryption, while Android users in Google Messages will see a padlock symbol. The feature is enabled by default for both new and existing RCS chats, as long as both sides meet the technical requirements.
Why Cross-Platform E2EE Matters for Everyday Users
The upgrade to encrypted RCS messaging is more than a technical milestone; it addresses a real privacy concern for mixed‑platform households, friend groups, and workplaces. Previously, any iPhone‑to‑Android text thread could silently drop to unsecured SMS or unencrypted RCS, exposing message contents to interception at the carrier or network level. With iOS 26.5 security improvements, those same threads are now protected by end‑to‑end encrypted texting when RCS is available, without users needing to consciously switch apps or adjust settings. This reduces the risk that sensitive information—such as login links, private photos, or business details—will travel in the clear. It also helps align the security expectations users have from iMessage and popular chat apps with what they actually get when texting Android contacts, making strong iPhone Android encryption the new default rather than an exception.
Rollout, Testing, and What Users Should Expect
Apple’s encrypted RCS implementation in iOS 26.5 follows months of phased testing. Initial trials began in the first iOS 26.4 developer beta, where Apple quietly enabled E2EE RCS but limited it to a small pool of iPhone users with iMessage disabled. Shortly afterward, a second developer beta allowed iPhones and Android devices to exchange fully encrypted RCS messages for the first time. Now, with 26.5, Apple has moved to large‑scale public testing, still labeling the feature as beta and rolling it out in phases. Users will automatically see encrypted RCS turned on over time for eligible new and existing conversations, signaled by the lock icon in chat. Apple also points to a list of participating carriers, and notes that the release accompanies fixes for more than 50 vulnerabilities across components like AppleJPEG, ImageIO, Kernel, mDNSResponder, and WebKit, further strengthening overall platform security.
