From APIs to Live Sessions: What the Codex Chrome Extension Changes
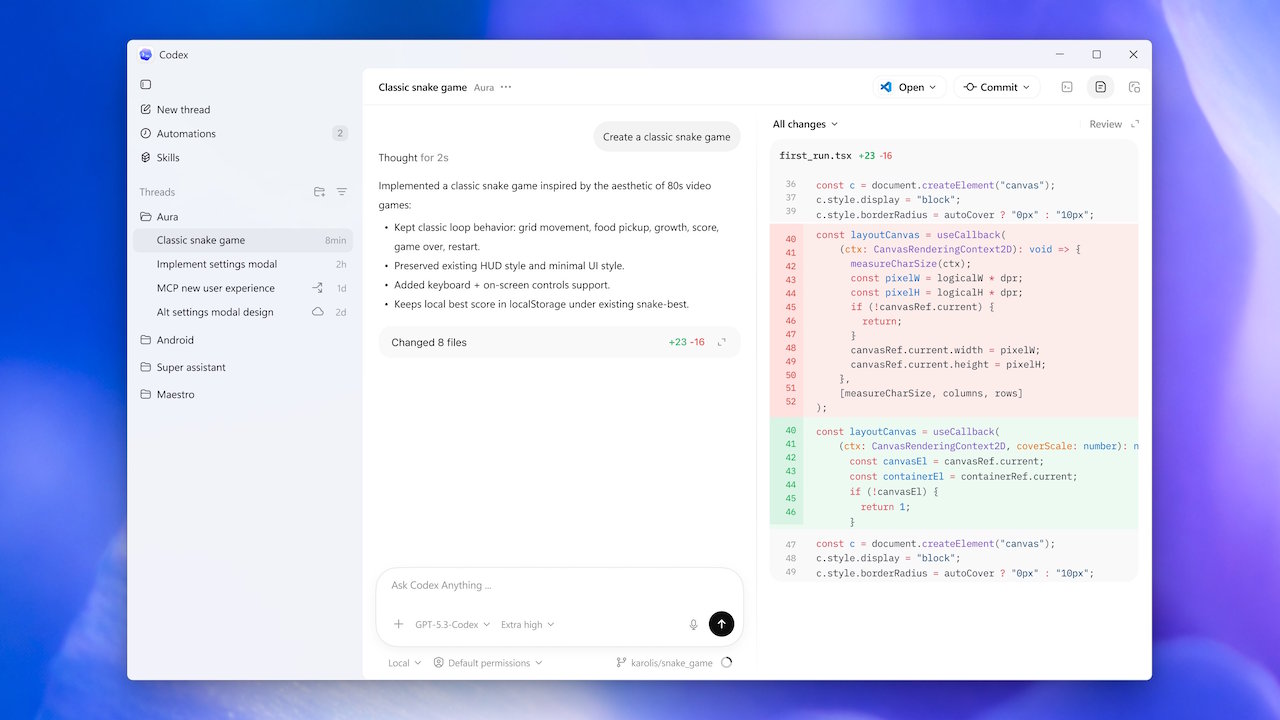
The Codex Chrome extension pushes AI browser automation into a space that APIs alone rarely reach: your live, signed-in sessions. Instead of relying only on integrations, Codex can now operate inside the same Chrome profile you use for Gmail, Salesforce, LinkedIn, and internal dashboards. Users can explicitly call it with prompts like “@Chrome open Salesforce,” letting Codex spin up its own tab groups and browser instance as needed. This approach lets the AI agent read page state, follow multi-step workflows, and interact with forms exactly as a human would in an authenticated web task. Crucially, Codex doesn’t replace the in-app browser or plugins; it complements them. Public pages and localhost work can stay in the built-in browser, while richly contextual, logged-in workflows move to Chrome. The result is broader coverage of everyday web tasks, without asking teams to rebuild everything around clean, well-structured APIs.
Task-Specific Tab Groups and Non-Disruptive Background Automation
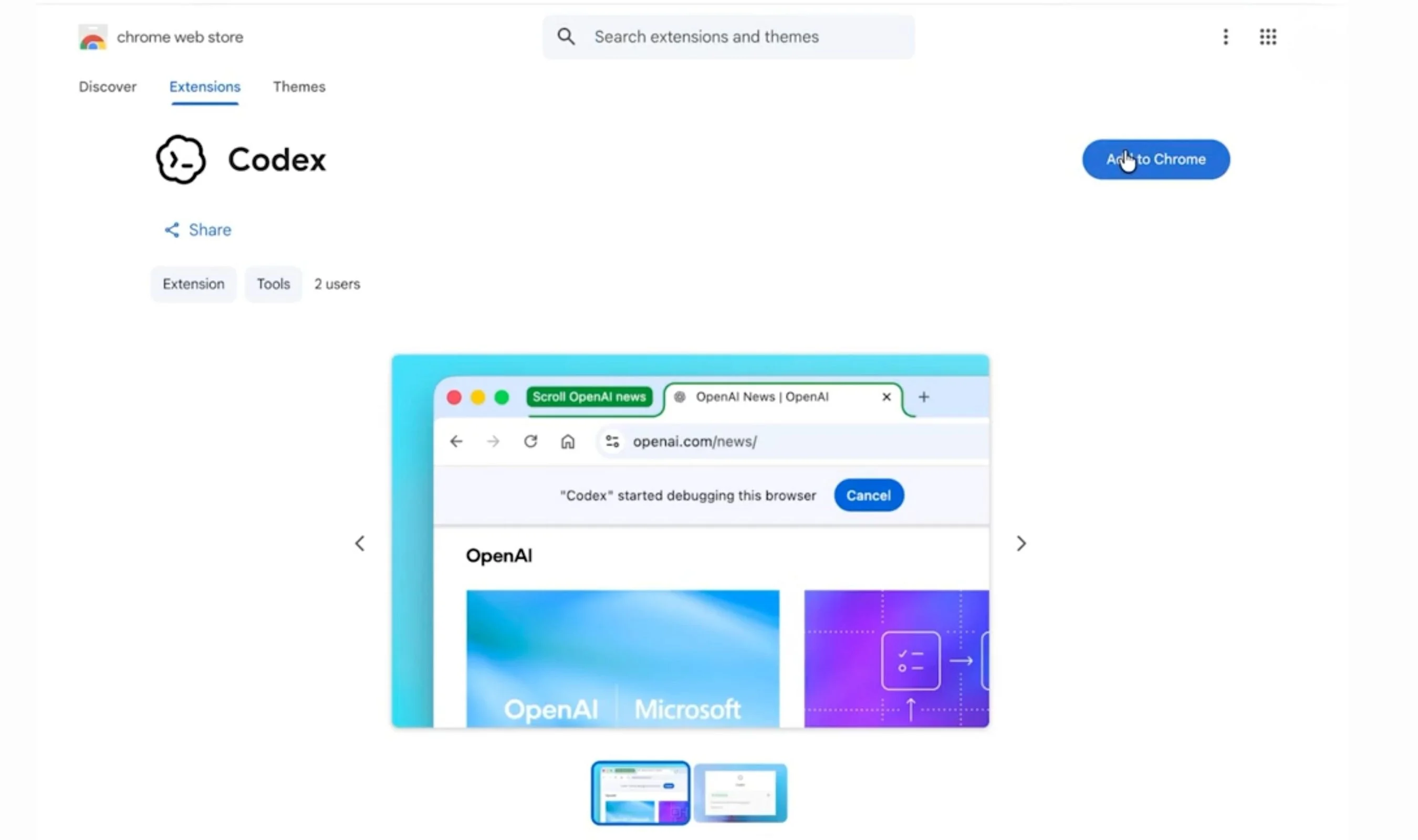
Instead of hijacking your screen, the Codex Chrome extension runs in the background through its own tab groups. OpenAI deliberately separates the agent’s workspace from your active browsing session, so you can keep working while Codex tests web apps, inspects logs, or reviews dashboards. Each task is isolated in dedicated tab groups, which keeps automation visibly bounded and easier to audit. The extension can gather context across multiple tabs, use Chrome DevTools in parallel, and keep test runs organised, all without reflowing your current window or shuffling your tabs. This makes it especially useful for developers, support teams, and operations staff who need continuous access to their own foreground tabs while offloading repetitive browser steps. Codex’s connection state is explicit too: you must install the plugin from within Codex, confirm Chrome’s prompts, and verify the extension is connected before any new background session begins.
Managing Authenticated Web Tasks with Approval Gates and Allowlists
Because the Codex Chrome extension can work inside signed-in services, its control model focuses heavily on approval and scoping. Codex is confined to its own tab groups and relies on host-specific prompts and approvals, rather than gaining blanket control over your browser. When the AI agent first encounters a new domain, it asks for permission, and site-level allowlists or blocklists in Codex’s Computer Use settings govern whether it can proceed. There is no permanent “always allow everything” switch: access to browser history and specific sites remains scoped per request. This design ensures that AI browser automation does not silently expand into sensitive areas of your account. For workflows involving Gmail, Salesforce, LinkedIn, or internal dashboards, users can choose precisely where Codex is allowed to operate, adding a practical layer of AI agent security on top of Chrome’s own permission system.
Windows Sandbox, DPAPI, and Network Controls Behind the Scenes
Behind the browser, Codex’s Windows sandbox reinforces security when tasks touch local resources or development environments. OpenAI’s design relies on separate offline and online sandbox users, keeping default tasks away from outbound network access unless you explicitly grant more connectivity. Before any child process runs, multiple enforcement layers kick in: DPAPI-protected credentials, firewall checks, and controlled command-runner handoffs reduce the chance of ungoverned behaviour. Codex can still read widely across a system and write inside the active workspace, but within a more tightly constrained environment than earlier Windows builds that lacked a sandbox. This matters for developers who blend local automation—such as scripts or build tools—with browser-based workflows. The sandbox model aligns Codex’s AI agent security posture with enterprise expectations, emphasising governance and observability rather than raw freedom, while still allowing productive everyday use on developer machines.
Remote Control, Voice Mode, and the Future of AI Browser Automation
On top of background automation, the Codex Chrome extension supports interactive control patterns designed to feel natural during real work. Users can steer Codex through prompts that invoke specific browser actions, or rely on its remote-control style capabilities to handle routine navigation, form filling, and dashboard checks across authenticated tabs. Voice mode, powered by OpenAI’s GPT-Realtime-2 speech model, is being developed to bring hands-free control into the same environment. That means developers debugging a deployment, or support agents triaging issues, could speak commands while Codex manipulates Chrome in parallel. Combined with task isolation and sandbox protections, these features point toward a future where AI browser automation becomes a normal part of everyday workflows instead of a disruptive novelty. Codex’s rapid growth in weekly active users suggests that many teams already see value in this controlled, collaborative approach to AI-driven browsing.