Three Privacy Defaults You Get Automatically in Android 17
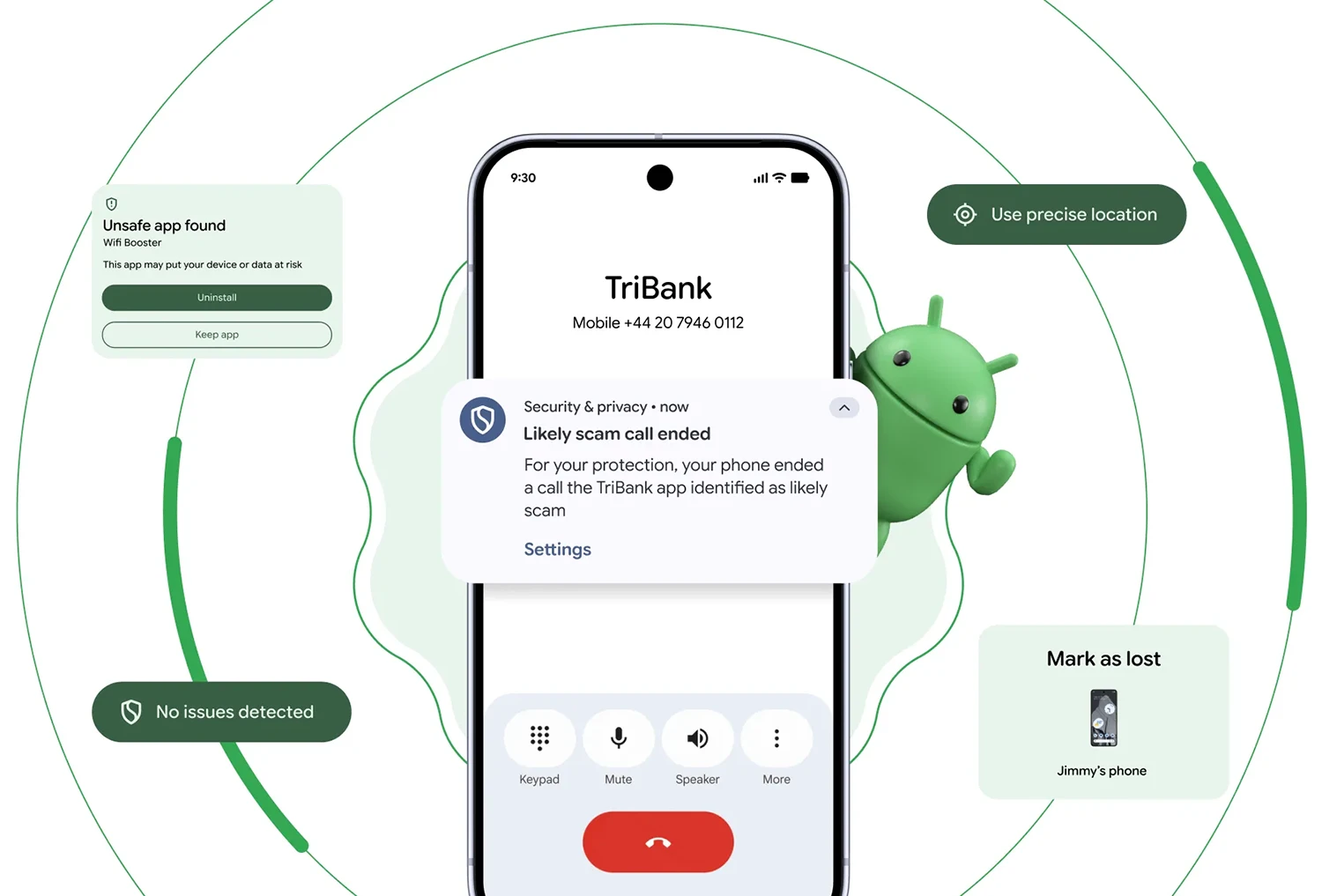
Android 17 introduces a powerful trio of privacy protections that switch on as soon as the update hits your device. You do not need to open Settings, tap a toggle, or respond to new prompts. These are app permissions defaults, not optional add‑ons, and they apply to apps targeting Android’s new API level 37. First, a system-level Contacts Picker replaces blanket access to your address book. Second, a new ACCESS_LOCAL_NETWORK permission stops apps from silently scanning devices on your Wi‑Fi. Third, Android delays most automated access to SMS one-time passwords (OTP), shutting down the “read your code before you do” trick many apps relied on. At the same time, Google is layering these changes into a broader security roadmap that also includes Live Threat Detection, verified financial calls, and tightened accessibility and USB protections. Together, they aim to reduce hidden tracking, fraud, and device abuse without overwhelming users with extra decisions.
Contacts Picker: No More Full Address Book Access by Default
Previously, granting contact permission meant handing an app your entire address book—every name, phone number, email, and note—often just to perform a single action. Android 17’s Contacts Picker changes that model completely. Instead of requesting broad READ_CONTACTS access, apps call a system picker, similar to the photo picker, letting you choose one or a few specific entries. Access is session-based and temporary: once you finish the task, the app’s contact access ends. That makes Android 17 privacy meaningfully stronger for everyday messaging, shopping, and productivity apps that never needed your full contact list in the first place. The Contacts Picker also works smoothly with work profiles and private spaces. You can pick contacts from personal or work lists without exposing the entire directory to the app. For users, the main takeaway is simple: if you see a contact selection screen instead of a permission pop-up, you are benefiting from a far safer default without losing functionality.
Local Network Blocking: Stopping Silent Device Scans on Your Wi‑Fi
Before Android 17, any installed app could quietly explore your local network. Games, shopping apps, or utilities you barely used could scan for devices on your router, spot nearby access points, and build a unique network fingerprint that helps track you across services. None of this required a visible permission or explicit approval. Android 17 fixes this by introducing the ACCESS_LOCAL_NETWORK runtime permission. Apps targeting the new platform can no longer discover or connect to devices on your LAN without asking. Legitimate tools—like smart home controllers or media server apps—have two paths: use a system device picker that handles the connection for them, or request this new permission when they truly need persistent access. Most users will notice nothing overt; many apps can simply rely on the picker. What changes is that background scanners lose their silent access. If an app suddenly asks to access your local network, you can decide whether its feature set actually justifies that level of connectivity.
SMS OTP Security: Delays That Disarm Silent Code Theft
Many people still rely on SMS for two-factor authentication. Traditionally, any app with SMS read permission could intercept one-time passwords the instant they arrived, filling them in before you even opened Messages. That convenience came with serious risk: malicious apps and SIM swap attackers could silently capture codes and hijack accounts. Android 17 introduces a three-hour delay before most third-party apps can programmatically read SMS messages containing OTP codes, strengthening SMS OTP security by default. This delay applies to apps targeting API level 37 and aims to block automated code harvesting, especially in fast-moving fraud scenarios. There are important exceptions so essential features keep working. Your default SMS app, approved assistant apps, and verified companion apps are exempt. Apps using Google’s SMS Retriever or SMS User Consent APIs—where you explicitly approve each use—also remain unaffected. In practice, you keep your normal login flow, while opportunistic apps lose the ability to quietly read your verification texts in real time.
How to Manage These Defaults and Keep Apps Working Smoothly
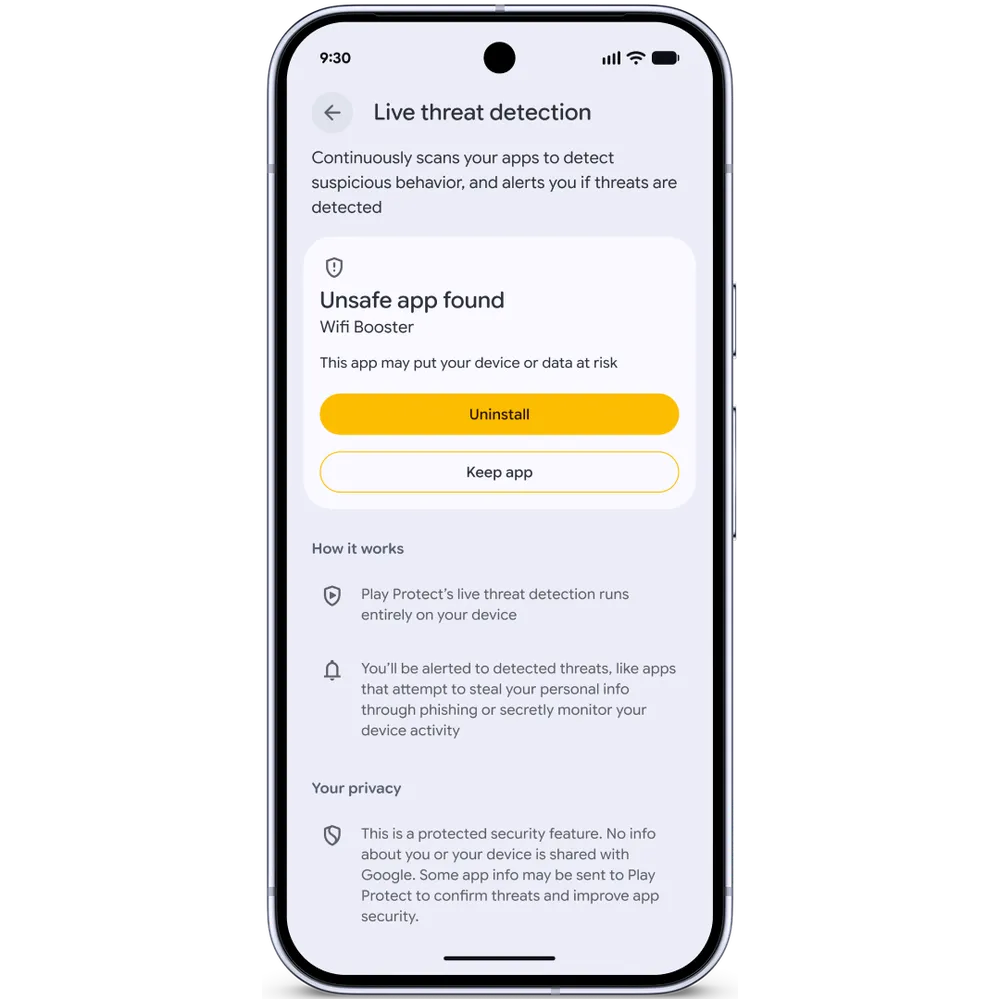
Despite being automatic, Android 17’s privacy features are not all-or-nothing. You stay in control. If a legitimate app breaks or loses functionality, you can review its permissions in Settings to decide whether it deserves broader access. For contacts, look for permissions related to address book or contact access. Many modern apps will lean on the Contacts Picker instead, so you may simply see a built-in selector instead of a toggle. For local network access, check whether a smart home, printer, or casting app has requested the ACCESS_LOCAL_NETWORK permission; if its core function depends on talking to devices on your LAN, granting it may be reasonable. For SMS OTP-related behavior, avoid granting general SMS read access unless absolutely necessary, and prefer apps that use the official SMS Retriever or User Consent flows. Combined with Android’s other protections—like Live Threat Detection and verified financial calls—these defaults give you a safer baseline while still allowing case-by-case flexibility.