Why This Apple Security Update Matters for Older Devices
Apple has rolled out a major security update cycle targeting not only its latest systems, but also older iPhones, iPads, and Macs that many people still use every day. The new Apple security update, released on Monday, delivers critical fixes for WebKit, kernel, Wi‑Fi, and sandbox components across a wide range of operating system versions, including macOS Tahoe 26.5, macOS Sequoia 15.7.7, macOS Sonoma 14.8.7, iOS 18.7.9, iPadOS 18.7.9, iPadOS 17.7.11, iOS 16.7.16, and iOS 15.8.8. These iPhone iPad Mac patches are designed to close serious security gaps that could enable everything from remote code execution via malicious web pages to elevated system access by rogue apps. Although Apple has not reported any of these flaws as actively exploited, the scope and depth of the kernel security flaw and WebKit vulnerability fix work make these updates urgent, especially for anyone relying on legacy hardware.
WebKit Vulnerability Fixes: How Malicious Websites Could Harm You
A key focus of this release is WebKit, the browser engine behind Safari, App Store previews, and in‑app web views across iOS, iPadOS, and macOS. Apple’s advisories describe multiple WebKit issues that could let attackers bypass Content Security Policy controls, leak sensitive data, crash browser processes, or corrupt memory using crafted web content. In the worst case, these bugs might let a malicious website execute arbitrary code on your device, turning a simple visit to a compromised page into a full system compromise. Because WebKit is used far beyond Safari—powering embedded browsers inside many apps—the risk extends to any feature that loads web content. Installing the latest Apple security update ensures that your device receives the necessary WebKit vulnerability fix, significantly reducing your exposure to drive‑by attacks and poisoned links delivered via email, messages, or embedded web views.
Kernel, Wi‑Fi, and Sandbox Escapes: Closing Deep System Gaps
Beyond WebKit, Apple has patched a wide range of kernel security flaws, Wi‑Fi vulnerabilities, and sandbox escape issues that strike at the core of system security. The kernel fixes include protection against root privilege escalation, kernel memory disclosure, integer overflows, out‑of‑bounds writes, race conditions, and Gatekeeper bypasses using malicious disk images or ZIP archives. Networking and wireless components also received serious attention, with patches for a Wi‑Fi bug that could allow arbitrary code execution with kernel privileges, plus denial‑of‑service issues triggered by crafted Wi‑Fi packets or mDNSResponder traffic. Apple further addressed vulnerabilities that could let apps escape sandbox restrictions, gain elevated privileges, or access protected user data such as contacts, notifications, or screen content. Together, these iPhone iPad Mac patches significantly harden devices against attackers attempting to move from a single app exploit to full‑system control.
Legacy Hardware Still Protected—But Only If You Update
One standout theme in this release is Apple’s continued support for older hardware. Instead of dropping security coverage when devices can no longer run the newest OS, Apple issued dedicated maintenance updates for iPadOS 17, iOS 16, and iOS 15. iPadOS 17.7.11 targets devices like the sixth‑generation iPad and earlier iPad Pro models, fixing a Notification Services bug where deleted notifications could remain stored unexpectedly. iOS 16.7.16 and iPadOS 16.7.16 extend protection to devices such as the iPhone X and first‑generation 12.9‑inch iPad Pro. Even further back, iOS 15.8.8 and iPadOS 15.8.8 support aging models like the iPhone 6s, iPhone 7, first‑generation iPhone SE, iPad Air 2, and iPad mini 4. This ongoing support only helps if you install the updates; otherwise, these devices remain exposed to the patched vulnerabilities.

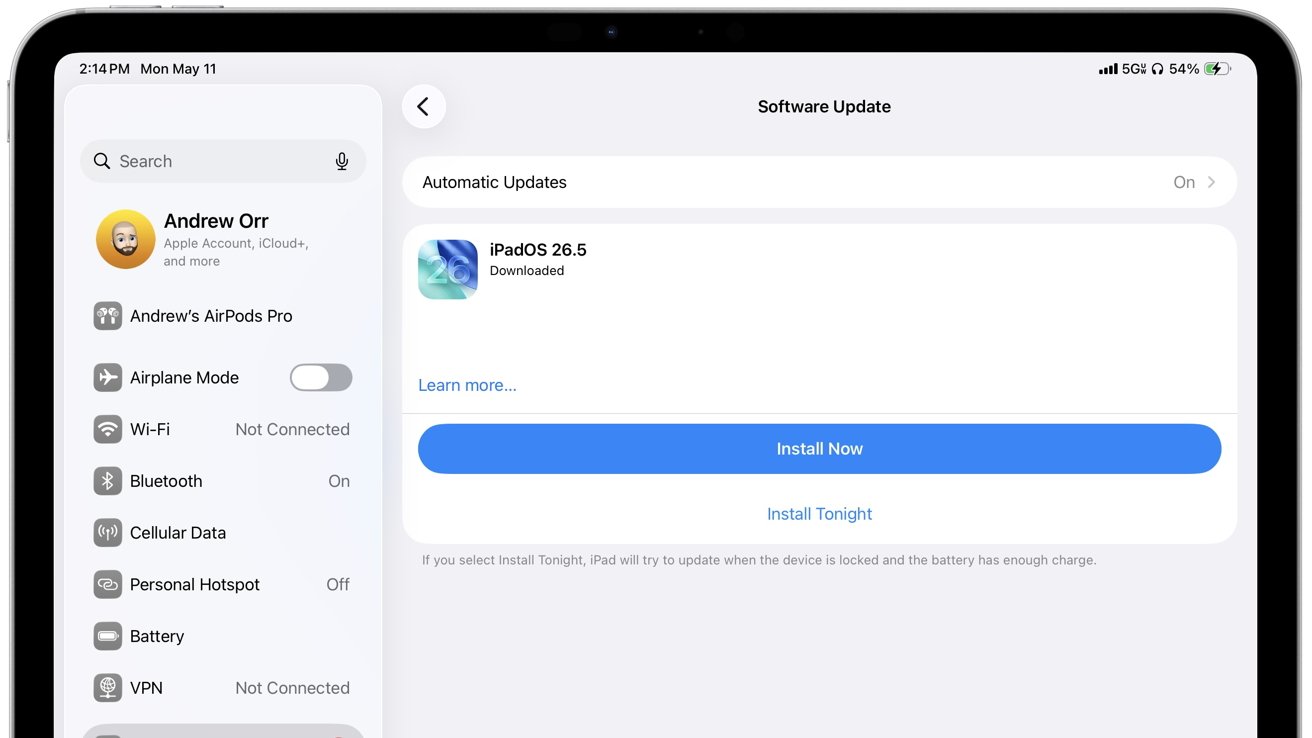
What You Should Do Now to Stay Secure
To benefit from these fixes, you should install the latest Apple security update on every eligible device as soon as possible. On iPhone and iPad, go to Settings → General → Software Update and apply any pending versions such as iOS 18.7.9, 16.7.16, or 15.8.8, and their iPadOS equivalents. On Mac, open System Settings (or System Preferences on older versions), then Software Update, and install the latest macOS release offered. Restart your device after updating so kernel, Wi‑Fi, and sandbox patches are fully applied. In addition, avoid untrusted apps, unknown configuration profiles, suspicious links, unsecured Wi‑Fi networks, and unsolicited file downloads—many patched issues involve crafted files or malicious web content. If you own hardware that no longer receives updates at all, avoid using it for sensitive activities such as banking, password management, or storing personal information, as it will remain permanently vulnerable.