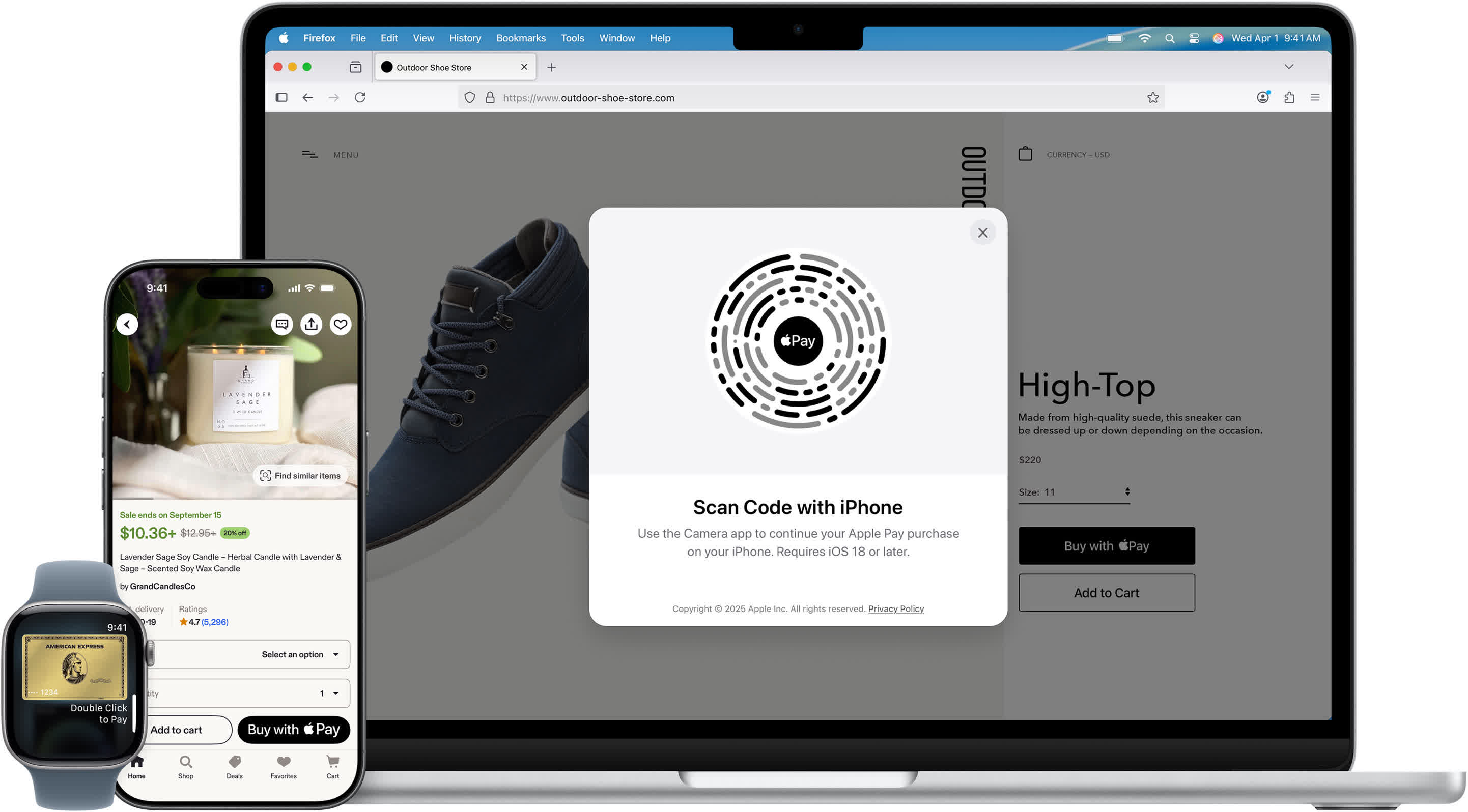
From Tap to Approval: What Really Happens in Two Seconds
To you, an Apple Pay purchase feels like a quick tap: double‑click, glance at your phone, and you’re done. Behind that simple motion is a tightly choreographed process built on modern contactless payment technology. Your iPhone or Apple Watch uses near‑field communication (NFC) to talk to the payment terminal over a distance of just a few centimeters. At the same time, EMV standards—originally designed for chip cards—define how your payment data is formatted, verified, and authorized. Once you authenticate with Face ID, Touch ID, or your passcode, Apple Pay pulls encrypted credentials from a dedicated Secure Element chip inside your device. It then constructs a one‑time payment package and sends it via NFC to the terminal. From there, the merchant’s systems and payment networks race to verify, decrypt, and authorize the transaction, usually in the time it takes you to put your phone back in your pocket.
Tokenization Explained: Your Card Number Never Leaves Your Device
The core of Apple Pay security is tokenization, a technique that swaps your real card number for a stand‑in called a Device Account Number (DAN). When you add a card to Apple Wallet, your bank works with a Token Service Provider to generate this token plus cryptographic keys. Apple stores the DAN and keys only inside the Secure Element on your device—not on Apple’s servers. When you pay, Apple Pay never shares your actual card number with the store. Instead, it sends the DAN plus fresh, transaction‑specific data. Even if a merchant’s systems are later breached, attackers see only useless tokens, not real card details. Because each device gets its own unique DAN, compromising one phone doesn’t unlock others. This architecture dramatically improves mobile wallet security by ensuring your actual card data stays confined to your device and your bank’s systems.
Layers of Payment Encryption and Biometric Checks
Before Apple Pay sends anything, it enforces a biometric checkpoint: Face ID, Touch ID, or a PIN must unlock the Secure Element. That chip is isolated from the rest of the phone’s software and holds the DAN and corresponding keys. Once unlocked, Apple Pay builds a cryptogram—a compact, encrypted bundle that includes the token, special token keys, the amount, and a dynamic CVV generated from a bank‑provided key. This cryptogram acts like a sealed envelope that only the right payment processors and networks can open. Because every transaction gets a unique cryptogram and CVV, replaying old data is useless to attackers. Combined, biometric authentication and robust payment encryption ensure that only an authorized user can initiate a payment and that the transmitted information remains protected from the moment it leaves your device to the moment it reaches your bank.
Real-Time Authorization: How Fraud Gets Stopped Mid-Transaction
Once the payment terminal receives your cryptogram, the merchant’s payment service provider (PSP) goes to work. It decrypts the package and formats a 3D Secure authorization request, then sends it through the card network—such as Visa or Mastercard—which in turn contacts the Token Service Provider to map the Device Account Number back to your real card. The token service validates the request, returns the actual card data to the network, and your bank checks the dynamic CVV and account status. Only if everything matches and your account can cover the transaction does the bank approve it. That approval then flows back through the network, PSP, and terminal, which signals success to your device. This entire loop runs in real time. Any mismatch, suspicious pattern, or invalid cryptogram can cause the transaction to fail before the payment completes, stopping many fraudulent attempts at the authorization stage.
Why Apple Pay Security Matters for Everyday Contactless Payments
Apple Pay’s design combines tokenization, strong payment encryption, biometric authentication, and real‑time authorization to make contactless payments both convenient and resilient against theft. Tokenization means merchants never see or store your actual card number, reducing the fallout if their systems are hacked. Biometric checks ensure that even if someone grabs your phone, they can’t easily use your mobile wallet. Unique, per‑transaction cryptograms and dynamic CVVs prevent attackers from reusing intercepted data. Finally, banks and networks continuously verify each payment as it happens, catching anomalies before money moves. For everyday users, this translates into a mobile wallet security model where your true card details stay between your device’s Secure Element and your issuing bank. The result is that those routine two‑second taps at the checkout counter rest on a deep stack of cryptography and controls you never have to see—but benefit from every time you pay.