Why This Apple Security Update Matters Now
Apple has issued a major round of critical security updates focused on iPhones, iPads, and Macs running older operating systems. These releases address a broad set of vulnerabilities spanning the kernel, WebKit, Wi-Fi, sandbox protections, and privacy frameworks. For users, the key takeaway is simple: if you are on an older system version, you are at elevated risk until you apply the latest Apple security update. Apple’s advisories describe issues that could allow attackers to escalate privileges, execute arbitrary code at the kernel level, escape app sandboxes, or access sensitive user data. Even though Apple has not reported any of these flaws as being actively exploited, the nature of the problems—especially WebKit vulnerability chains and Mac kernel flaw scenarios—means they could be weaponized quickly. Installing the patches promptly is the most effective way to preserve your device’s baseline security.
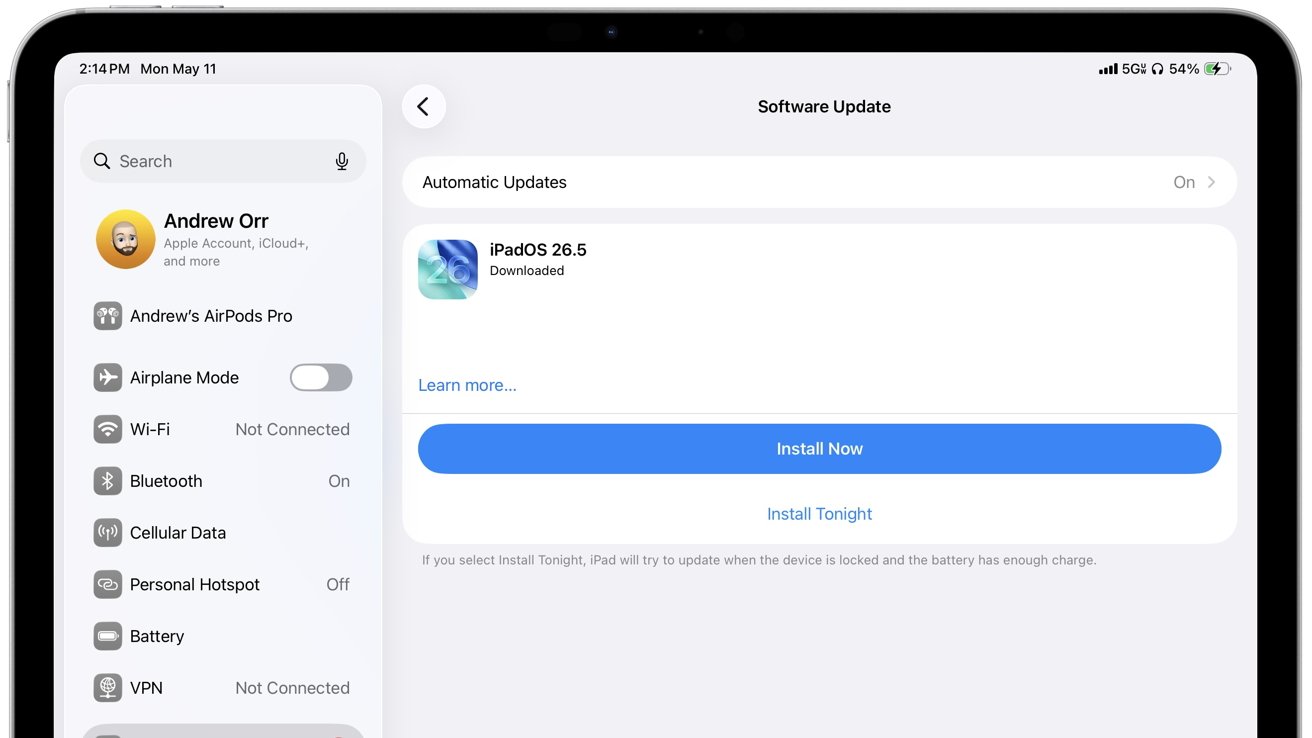
Which iPhones, iPads, and Macs Need Immediate Updates
The latest release cycle covers both current-generation systems and a wide range of older Apple hardware. On the Mac side, Apple has shipped security patches for macOS Tahoe 26.5, macOS Sequoia 15.7.7, and macOS Sonoma 14.8.7, with Tahoe receiving some of the most extensive fixes. For mobile devices, iOS 18.7.9 and iPadOS 18.7.9 target devices such as the iPhone XS, iPhone XR, and the seventh‑generation iPad. Apple is also maintaining legacy branches: iPadOS 17.7.11 supports models including the sixth‑generation iPad and earlier iPad Pro variants, while iOS 16.7.16 and iPadOS 16.7.16 serve devices like the iPhone X and first‑generation 12.9‑inch iPad Pro. Even older hardware, such as the iPhone 6s, iPhone 7, first‑generation iPhone SE, iPad Air 2, and iPad mini 4, is covered via iOS 15.8.8 and iPadOS 15.8.8. If your device falls into any of these families, you should install the corresponding iPhone security patch or iPad update without delay.

The Most Serious WebKit, Kernel, and Wi‑Fi Flaws Explained
Many of the most critical fixes focus on WebKit, the browser engine behind Safari, App Store previews, embedded in‑app browsers, and countless web views across Apple platforms. Apple has patched multiple WebKit vulnerabilities that could bypass Content Security Policy protections, leak sensitive information, corrupt memory using malicious web content, or crash browser processes. At the system level, the updates deliver extensive kernel hardening, closing holes that could enable root privilege escalation, kernel memory disclosure, integer overflows, out‑of‑bounds writes, and race conditions. Some of these issues are classic Mac kernel flaw cases that attackers could chain with other bugs for full device compromise. Networking components also received urgent fixes, including a Wi‑Fi vulnerability that could allow arbitrary code execution with kernel privileges via an out‑of‑bounds write, along with denial‑of‑service issues triggered by crafted Wi‑Fi packets and mDNSResponder traffic. Together, these patches significantly reinforce both browser-based and system-level defenses.
Sandbox Escapes, Privacy Risks, and What Users Should Do
Beyond WebKit and the kernel, Apple’s latest patches tackle multiple threats to app isolation and user privacy. Some vulnerabilities could let malicious apps gain elevated privileges, escape the sandbox, or enumerate installed apps. Others involve App Privacy Report bypasses, IP address tracking, unauthorized access to Contacts, and even screen capture risks through camera metadata exposure. A Notification Services flaw affecting several legacy branches meant deleted notifications could remain stored on‑device unexpectedly. While Apple has not flagged any of these issues as currently exploited in the wild, they collectively weaken the security model if left unpatched. To reduce risk, users should immediately install the relevant Apple security update, then restart their devices so low‑level fixes fully apply. In daily use, avoid untrusted apps, suspicious links, unsecured Wi‑Fi networks, and unsolicited file downloads. If your device no longer receives updates, avoid using it for sensitive tasks such as banking, password storage, or handling highly personal data.