Android 17 Privacy: Automatic Protection Without Extra Prompts
Android 17 is reshaping how app permissions work on Android by shifting privacy from something you manage manually to something the system enforces by default. Instead of relying on endless pop‑ups and checkboxes, Google is introducing three automatic safeguards that tighten access to your contacts, local network, and SMS one‑time passwords (OTPs). These changes apply to apps targeting API level 37, meaning new and updated apps must play by the new rules. Crucially, most users will never see a new permission dialog for any of this. The protections sit at the platform level and run silently in the background. For everyday users, that means fewer confusing decisions about which toggles to flip. For developers, it means building around stricter defaults that assume data should not be shared unless there is a clear, narrow reason. Android 17 privacy is less about new switches and more about making the safest option the standard.
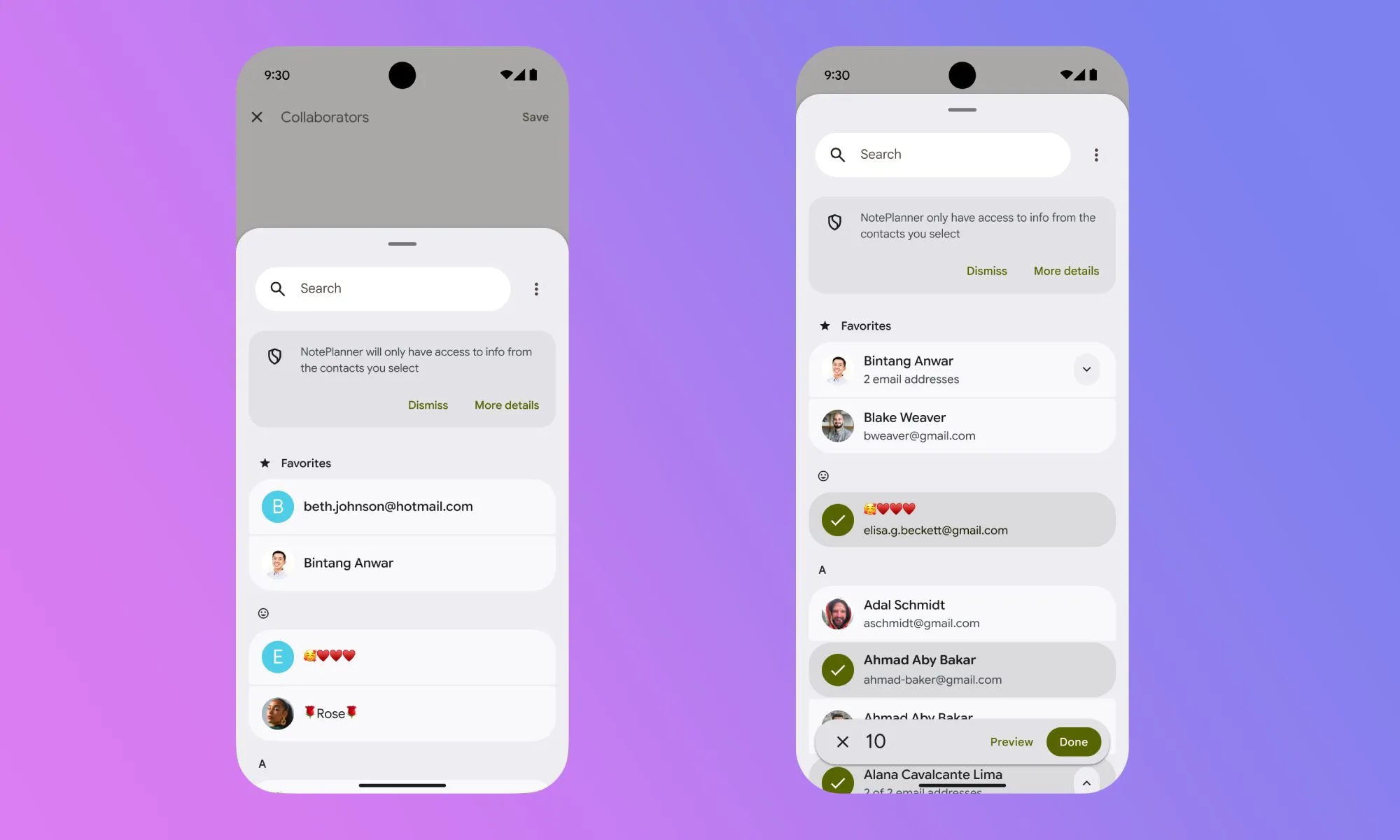
Contacts Picker: Sharing One Contact, Not Your Entire Address Book
Until now, app permissions on Android treated your address book as all‑or‑nothing: grant contacts access and the app could read every name, number, email, and note you had stored. Android 17 fixes this with a new contacts picker feature that mirrors the system photo picker. Instead of requesting broad READ_CONTACTS permission, apps call a system‑level picker that lets you choose exactly which contact or contacts to share for that specific task. Access is temporary and session‑based; once you finish the interaction, the app’s access ends. Apps can also request only particular fields, such as just a phone number, rather than the full contact card. This is a major shift in app permissions on Android because it removes the leverage apps had to demand blanket access as the price of using a single feature. By default, your address book stays private, and only the sliver of data you explicitly select is shared.
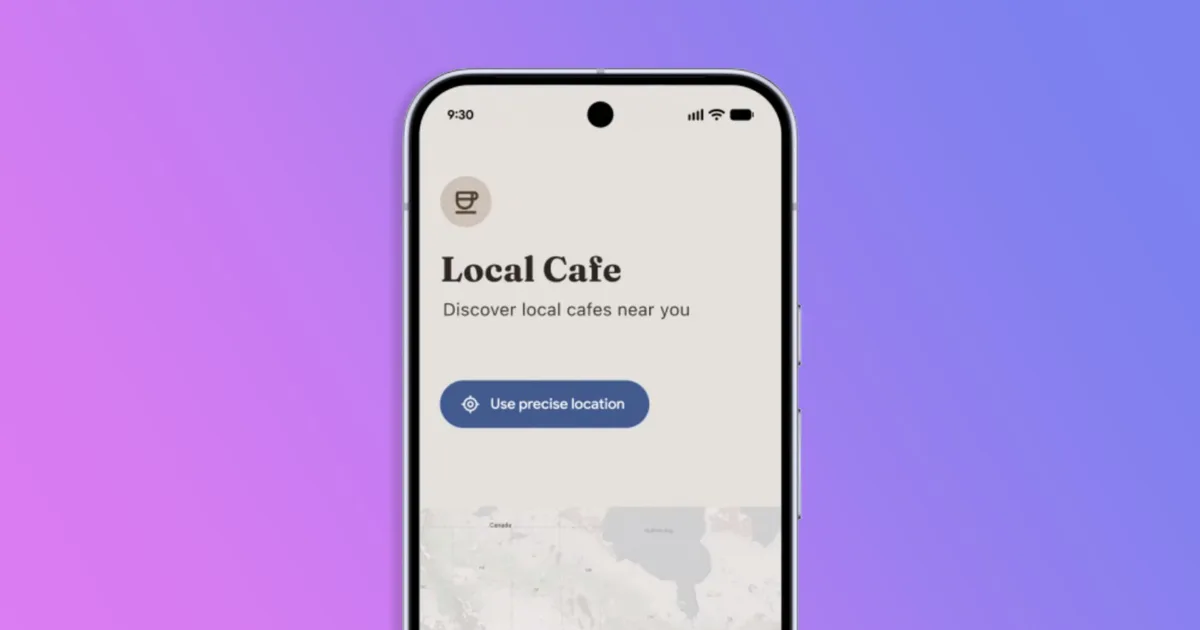
Local Network Block: Stopping Quiet Scans of Devices on Your Wi‑Fi
Behind the scenes, many apps have historically enjoyed unrestricted visibility into your local area network. A casual game, an old utility, or a shopping app could quietly scan your Wi‑Fi, see which devices were connected, and use that information for network fingerprinting—building a profile of you based on your home or office setup. Android 17 introduces a new runtime permission, ACCESS_LOCAL_NETWORK, to shut this down by default. Apps targeting API level 37 must now either use a system device picker, which handles connections without revealing the entire network, or explicitly request local network access at runtime. Most users will never encounter a prompt, because well‑designed apps can rely on the picker instead of broad scanning. Only apps that genuinely need persistent LAN communication, such as smart home controllers or media servers, should ask. Quiet scanners that previously mapped your network for tracking purposes will simply stop working, without fanfare or extra effort from you.
SMS OTP Delay: Adding Friction to Silent Code Theft
SMS OTP security has long been undermined by apps that request broad SMS read permissions and then automatically intercept verification codes the moment they arrive. Users often never realise an app is silently reading their text messages in the background. Android 17 tackles this by adding a three‑hour delay before most third‑party apps can programmatically access SMS containing one‑time passwords. This delay applies to apps targeting API level 37 that rely on general SMS permissions rather than dedicated APIs. There are important exceptions: your default SMS app, assistant apps, verified companion apps, and apps using the SMS Retriever or SMS User Consent APIs are not affected. For you, OTPs still arrive normally in your messaging app, but any opportunistic app trying to read them will see only expired codes. By making code interception useless, Android 17 closes a common attack path without forcing you to change habits or switch authenticator tools.
Why These Privacy Defaults Are Opt‑Out for Developers, Not Opt‑In for Users
A key theme in Android 17 privacy is that Google is no longer asking users to opt into safer behaviour. Instead, the platform assumes privacy‑preserving options by default and requires developers to adapt. If the contacts picker were optional or the local network block a hidden toggle, most people would never enable them, leaving the old, broad permissions in place. By tying these protections to API level 37, Google pushes the responsibility onto app makers: they must use system pickers, justify network access, or adopt safer SMS OTP security APIs. Users gain stronger protection with fewer decisions and fewer confusing prompts. At the same time, the new model still allows legitimate use cases—as long as they are narrow, transparent, and time‑bound. The net effect is a quiet but significant shift: Android is moving away from “ask the user everything upfront” toward “limit data by design and only expand access when absolutely necessary.”