A Canvas Data Breach That Brought Campuses to a Standstill
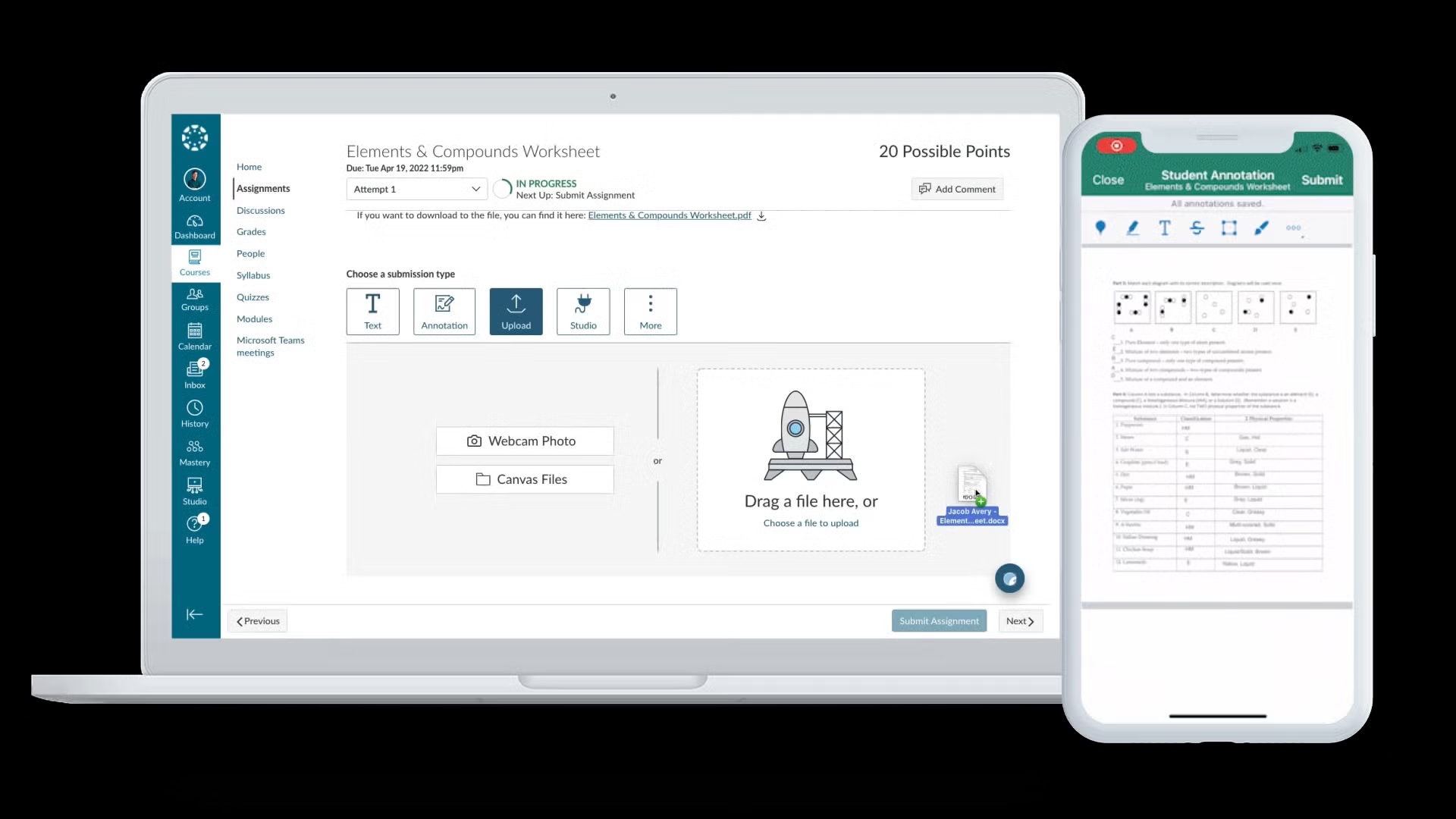
The Canvas data breach was not just another security incident; it crippled day-to-day academic operations across thousands of institutions. Instructure, the developer of the cloud-based education platform Canvas, discovered a major intrusion on 29 April, later identifying further unauthorised activity on 7 May. The ShinyHunters hackers claimed responsibility, saying they had accessed 3.5 terabytes of data and stolen 280 million records, including names, email addresses, messages and student ID numbers. Around 9,000 institutions using Canvas were reportedly affected, with outages hitting during peak exam season. Students at Mississippi State University even reported ransom notes appearing mid‑exam, forcing postponements. In Ireland, the University of Galway and Munster Technological University experienced service disruptions as they scrambled to restore access. The scale and timing of the attack exposed just how dependent modern education has become on a small number of cloud platforms to deliver teaching, assessment and communication.
Instructure’s Ransomware Payment: A Controversial Incident Response
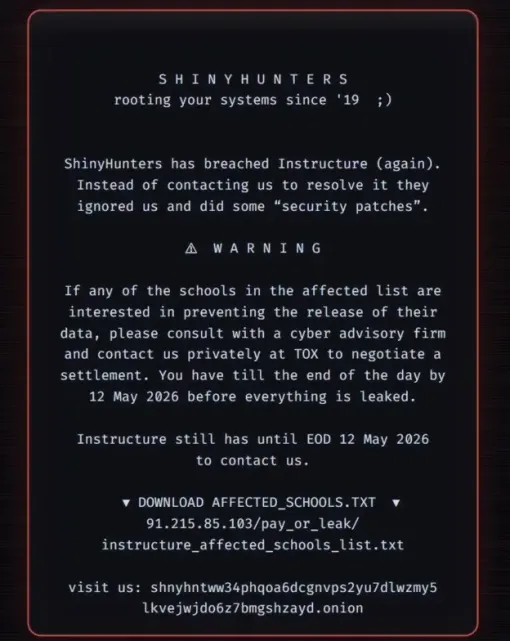
Under intense pressure from disrupted universities and students, Instructure chose a response strategy that many security leaders view as a last resort: it reached a settlement with ShinyHunters. The company confirmed that it paid an undisclosed ransom to obtain what it called “digital confirmation of data destruction” and an agreement that the hackers would return stolen data, delete copies and refrain from further extortion of affected institutions and individuals. Instructure framed the decision as a pragmatic step to give customers peace of mind after an attack that threatened to leak billions of private messages between students and teachers. However, the move runs counter to guidance from law enforcement agencies such as the FBI and the UK’s National Crime Agency, which argue that paying cybercriminals fuels the extortion economy and offers no technical guarantee that stolen information will not resurface later on underground markets.

How ShinyHunters Exploited Platform Weakness and Exam Pressure
ShinyHunters, an English‑speaking extortion group active since around 2020, has built a reputation by targeting high‑profile organisations from technology companies to major brands. In the Canvas breach, the group allegedly exploited issues in Instructure’s infrastructure, including a weakness tied to its “free‑for‑teacher” accounts, which has now been shut down. The attackers claimed to have compromised Canvas twice over the past year before this large‑scale operation, suggesting a persistent focus on the platform. Crucially, ShinyHunters timed the attack to coincide with exam season, when universities were most reliant on Canvas for assessments and grading. As one cybersecurity CEO noted, this maximised leverage: institutions needed the platform up and running, making it an “agree to terms or lose customers” situation for Instructure. The case illustrates a broader shift in cybercrime tactics from pure technical lockouts to strategic disruption of business‑critical timelines.
Implications for Education Cybersecurity and Ransomware Strategy
The ransomware payment in the Canvas data breach underscores the difficult trade‑offs universities and edtech providers face when core services are taken hostage. While paying may seem to protect students from further harm, it can also label an organisation as a lucrative, compliant target, inviting repeat attacks. Law enforcement experience with groups like LockBit shows that even when victims pay, hackers often retain copies of stolen data for future sale or leverage. For the education sector, this incident is a warning to move beyond perimeter defences and invest in continuous monitoring, rigorous third‑party risk management, and incident‑ready backup and recovery plans. Institutions also need clear playbooks for communicating with students and staff during outages, and for making principled decisions about ransom demands. Ultimately, the case highlights a troubling “consent or pay” dynamic, where the privacy of academic communities becomes a bargaining chip in global extortion schemes.