What Apple Just Fixed on Older iOS, iPadOS, and macOS Devices
Apple has released a broad Apple security update for users still running older versions of iOS, iPadOS, and macOS, targeting critical weaknesses in core system components. The latest patches cover macOS Tahoe 26.5, macOS Sequoia 15.7.7, macOS Sonoma 14.8.7, iOS 18.7.9, iPadOS 18.7.9, iPadOS 17.7.11, iOS 16.7.16, and iOS 15.8.8. These updates are not just routine maintenance; they address high‑impact flaws in WebKit, the operating system kernel, Wi‑Fi networking, and key privacy and sandboxing protections. Even though these devices no longer run Apple’s newest platforms, they remain deeply integrated with sensitive data and online services. Leaving them unpatched significantly increases the risk of exploitation through malicious web content, crafted files, or compromised apps. If your iPhone, iPad, or Mac is still on one of these legacy systems, installing the latest software update is now a critical security priority.
Why WebKit, Kernel, and Wi‑Fi Vulnerabilities Are So Dangerous
Many of the most serious issues in this release involve a WebKit vulnerability fix and an extensive kernel security patch set. WebKit powers Safari, embedded browsers inside apps, App Store previews, and countless in‑app web views, so any bug here can be triggered just by visiting a malicious website or opening hostile web content. Apple’s updates address flaws that could leak sensitive data, bypass Content Security Policy, corrupt memory, or crash browser processes. At the same time, kernel vulnerabilities are particularly severe because they sit at the heart of the operating system. The new kernel fixes target privilege escalation, kernel memory disclosure, race conditions, and out‑of‑bounds writes that could enable attackers to execute arbitrary code with root‑level permissions. On the networking side, patched Wi‑Fi bugs could have allowed arbitrary code execution via crafted wireless packets, as well as denial‑of‑service attacks against devices connected to hostile networks.
Sandbox Escapes and Privacy Weaknesses: How Apps Could Break Out
Beyond browser and kernel risks, Apple’s latest patches close multiple sandbox escape vulnerability chains and privacy leaks. The sandbox is designed to isolate apps so they can’t freely access system resources or other data. According to Apple’s advisories, several flaws could have allowed malicious or compromised apps to gain elevated privileges, escape sandbox restrictions, or access protected user information. Additional fixes address issues in Notification Services where deleted notifications might remain stored on‑device, as well as problems involving installed app enumeration, App Privacy Report bypasses, IP address tracking, unauthorized Contacts access, and even screen capture enabled by camera metadata exposure. Combined, these weaknesses could give attackers a clearer view of your activity, your installed apps, and parts of your personal data. Applying these updates helps restore the integrity of Apple’s app isolation model and reduces the chance that a seemingly harmless app could quietly overreach its permissions.
Legacy Hardware Still Supported—But Only Safe If You Patch
Notably, Apple is still shipping security fixes for hardware released as far back as devices like the iPhone 6s, iPhone 7, first‑generation iPhone SE, iPad Air 2, and iPad mini 4, via iOS 15.8.8 and iPadOS 15.8.8. iOS 16.7.16 and iPadOS 16.7.16 extend protection to models such as the iPhone X and the first‑generation 12.9‑inch iPad Pro, while iPadOS 17.7.11 specifically targets the sixth‑generation iPad and several older iPad Pro models with a Notification Services fix. This continued support means you can keep using older hardware more safely—but only if you install updates promptly. Devices that no longer receive any security updates should not be used for high‑risk tasks such as banking, password management, or storing sensitive personal data. If your aging iPhone, iPad, or Mac is still supported, updating now significantly lowers your exposure to many classes of modern attacks.

How to Stay Protected: Practical Steps for Users
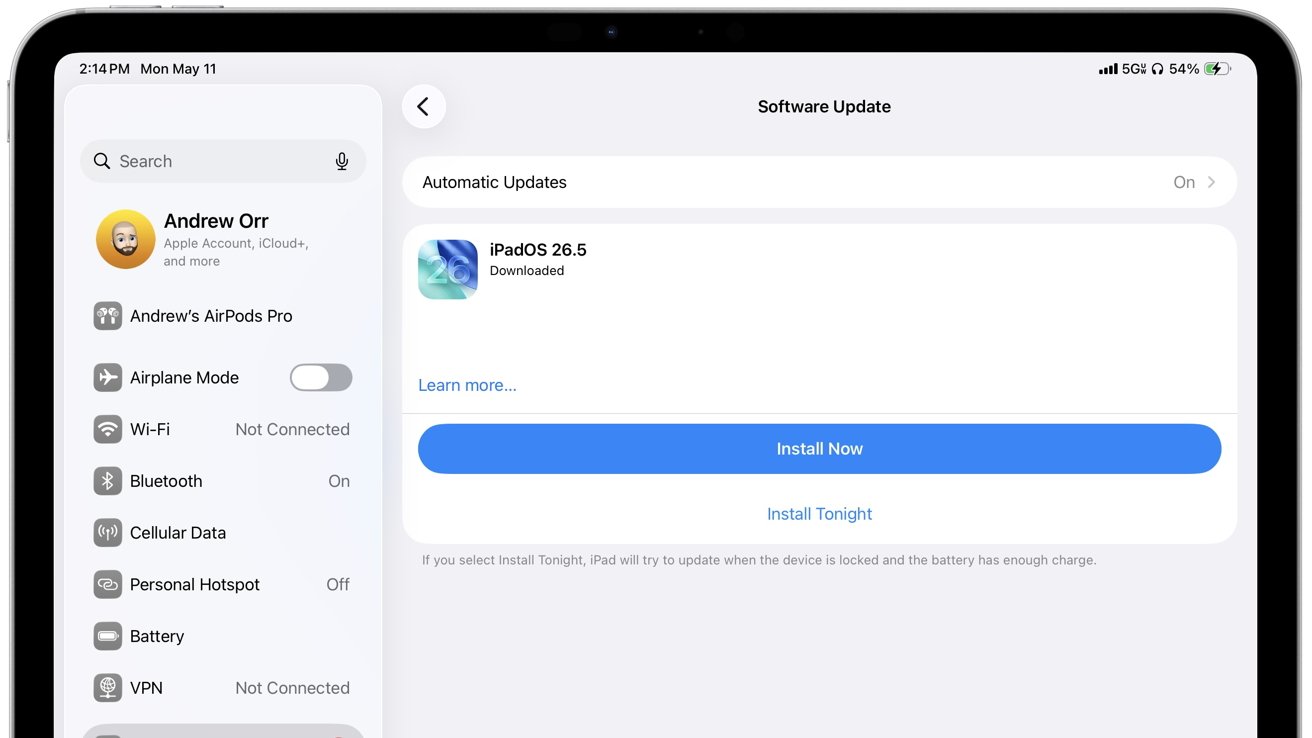
To benefit from these security fixes, you must install the updates and restart your devices so kernel and Wi‑Fi patches fully apply. On iPhones and iPads, go to Settings > General > Software Update and apply any pending downloads. On Macs, open System Settings or System Preferences and check for software updates. Beyond patching, minimize risk by avoiding untrusted apps and configuration profiles, steering clear of suspicious links and email attachments, and not joining unsecured or unknown Wi‑Fi networks. Be cautious when opening ZIP archives or disk images from unverified sources, as some patched vulnerabilities involved Gatekeeper bypasses and crafted files. Because many of the fixed issues involve malicious web content, ensure Safari and any system browser components are up to date. If your device is no longer supported at all, consider limiting it to offline or low‑sensitivity tasks and moving critical activities to a fully patched device.