Inside the Canvas Data Breach and Ransom Settlement
Instructure, the company behind the Canvas education platform, recently confirmed it reached a settlement with the cyber extortion group ShinyHunters after a major Canvas data breach. Attackers reportedly accessed vulnerabilities in Instructure’s infrastructure and exploited an issue tied to its “free-for-teacher” accounts, infiltrating the platform twice over the past year. The latest attack, detected on April 29 and again on May 7, paralysed operations at roughly 9,000 institutions and was timed to hit during peak exam season. ShinyHunters claimed to have stolen 3.5 terabytes of data and up to 280 million records, including names, email addresses, messages and student ID numbers. Instructure says the group has returned the stolen data, deleted copies and agreed not to extort affected institutions. The company also says it obtained “digital confirmation of data destruction,” though it has not disclosed what it provided in return or the sum paid in this ransomware settlement.

Service Disruptions Show the Human Cost of Platform Dependence
The Canvas data breach was not just a technical incident; it directly disrupted teaching and assessment for thousands of institutions and millions of students. In some cases, students reported seeing ransom notes appear mid-exam, forcing universities such as Mississippi State University to postpone assessments. In Ireland, universities including the University of Galway and Munster Technological University experienced platform outages and exam-time disruptions as Canvas services went offline. This underscores how deeply embedded learning management systems have become in everyday academic operations. When a single education platform serves thousands of organisations, a security incident can cascade into timetable chaos, delayed graduations and heightened anxiety for students and staff. The breach highlights how education platform security is no longer a back-office issue; it is integral to continuity of learning, reputation management and student trust. Institutions now need to factor prolonged digital outages into their academic and risk planning processes.
Why the Ransom Deal Raises Difficult Security and Ethical Questions
Instructure’s decision to settle with ShinyHunters highlights a growing tension between immediate student data protection and long-term cybercrime deterrence. Law enforcement bodies such as the FBI and the UK’s National Crime Agency routinely advise organisations not to pay ransoms, warning that payments fuel the criminal ecosystem and provide no guarantee that data is truly deleted. Past investigations into other groups, like LockBit, have shown that attackers sometimes keep stolen data even after being paid. Yet Instructure argued that obtaining digital assurances of deletion was necessary to give customers peace of mind and avoid further extortion of universities or students. Security experts note that attackers are increasingly shifting from pure encryption-based ransomware to broader extortion tactics that target organisational dependencies and reputational risk. This case illustrates a “consent or pay” dynamic, where critical services and personal information are effectively held hostage, forcing institutions and vendors into painful trade-offs.

Lessons for Education Platform Security and Vendor Management
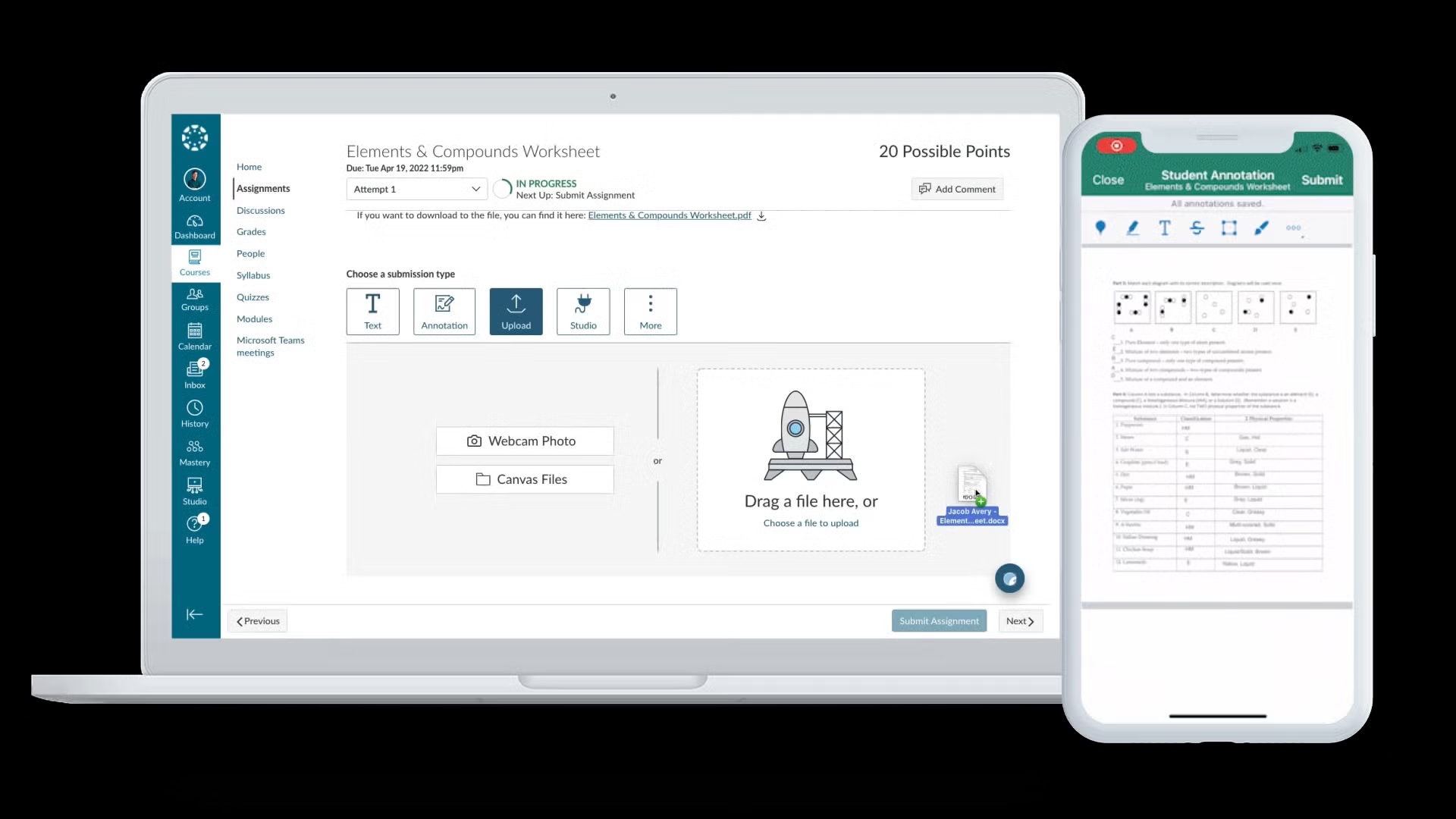
For schools and universities, the breach is a stark reminder that outsourcing to cloud-based platforms does not outsource risk. The exploitation of Canvas’s “free-for-teacher” accounts and broader infrastructure issues shows how a single feature misstep can expose vast amounts of student data. Institutions must treat education platform security as a shared responsibility, demanding transparency into vendors’ security controls, regular penetration testing and clear remediation timelines. Contracts should include explicit incident response obligations, data breach notification requirements and limits on how student data is stored and accessed. Governance teams should also scrutinise optional or legacy features that may introduce unexpected attack paths. Beyond due diligence, institutions need to regularly review access controls, monitor unusual activity in their learning management systems and ensure that their own integrations and customisations do not weaken platform defences. The Canvas incident demonstrates that even established providers can become high-value targets for sophisticated extortion groups.

Building Stronger Student Data Protection and Incident Response
In the wake of the Canvas data breach, institutions should reassess both their student data protection practices and their readiness for future incidents. First, they need a clear inventory of what data resides in external platforms, how long it is retained and who can access it. Minimising sensitive data stored in third-party systems, enforcing strong authentication and segmenting access for staff and students can reduce the impact of future breaches. Second, organisations must maintain an incident response plan aligned with their dependence on digital learning tools. This includes predefined procedures for switching to contingency assessment methods, communicating with students and regulators and coordinating with vendors and law enforcement. Regular tabletop exercises involving IT, academic leadership and communications teams can surface gaps before a crisis hits. Ultimately, resilience will depend on combining stronger technical safeguards with a culture that treats cybersecurity as a core part of educational quality and student welfare.