Why Signal Is Tightening Its Defenses Against Phishing
Signal has introduced a suite of new message security features aimed squarely at phishing and social engineering protection. The move follows recent waves of account hijackings and targeted phishing campaigns against high‑risk users such as journalists and officials. Instead of relying only on encryption, Signal is now focusing on the human side of security: helping people recognize when a conversation feels off. Scammers have increasingly impersonated Signal itself, posing as “Signal Support” or using display names that look official. Because this kind of attack tricks you into handing over keys to your account, rather than hacking the app’s infrastructure, user education is critical. These new in‑app prompts are designed to meet you where the risk happens—inside your chats—so you can react before sharing sensitive information or approving a malicious login.

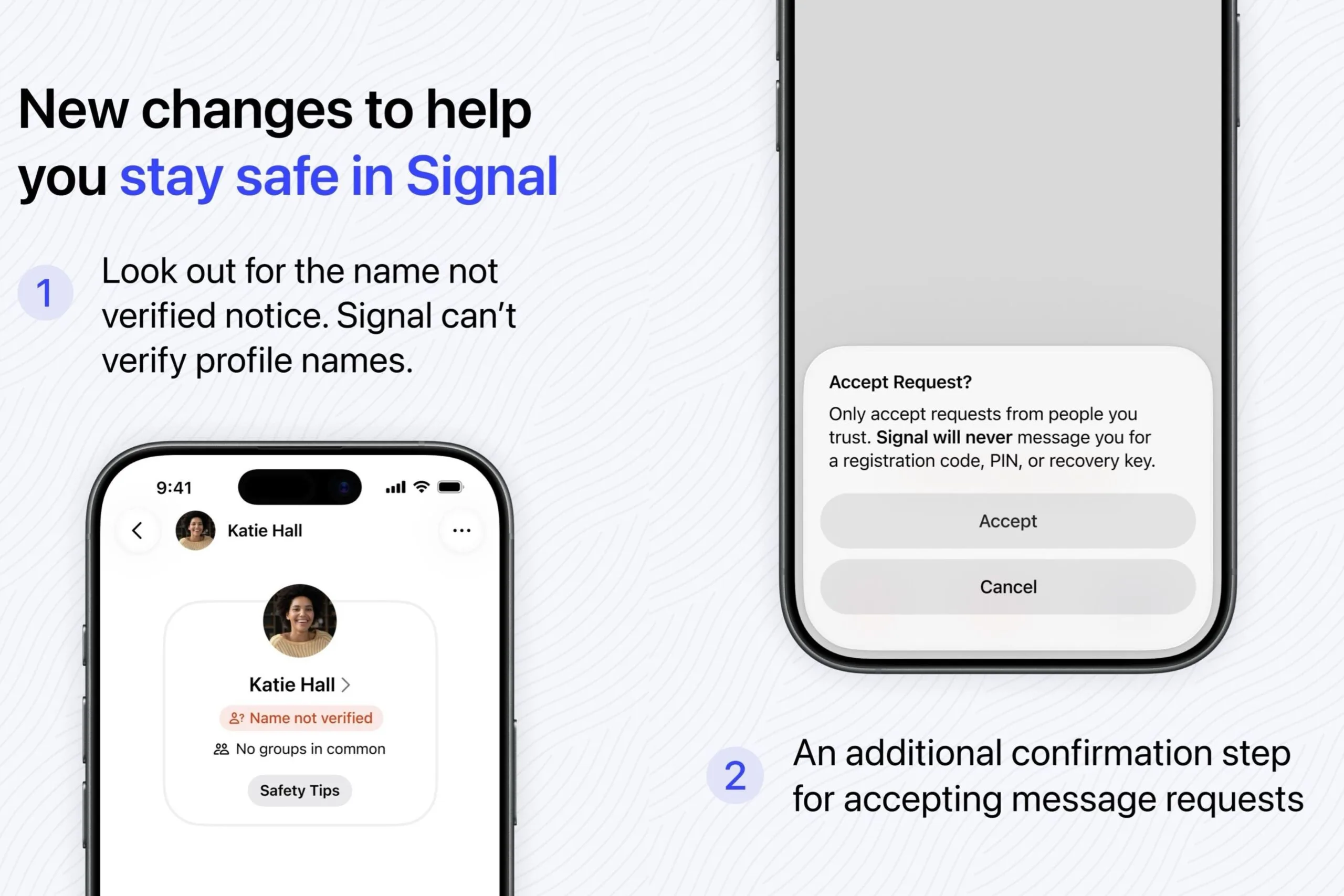
New Unsolicited Message Warnings and Name Alerts
One of the most visible changes is how Signal now treats messages from people you have never spoken to before. When a new conversation starts, you will see an “Accept Request” prompt reminding you to be cautious with unsolicited message warnings. The prompt clearly states that you should only accept requests from people you trust and that Signal will never ask for your registration code, PIN, or recovery key. Another important addition is the “name not verified” notice on profiles. Signal cannot validate the names users choose, so anyone can claim to be a friend, a colleague, or even the app itself. By explicitly highlighting that profile names are self‑selected, Signal nudges you to verify identities out‑of‑band—such as confirming via a known number or another channel—before sharing anything sensitive.
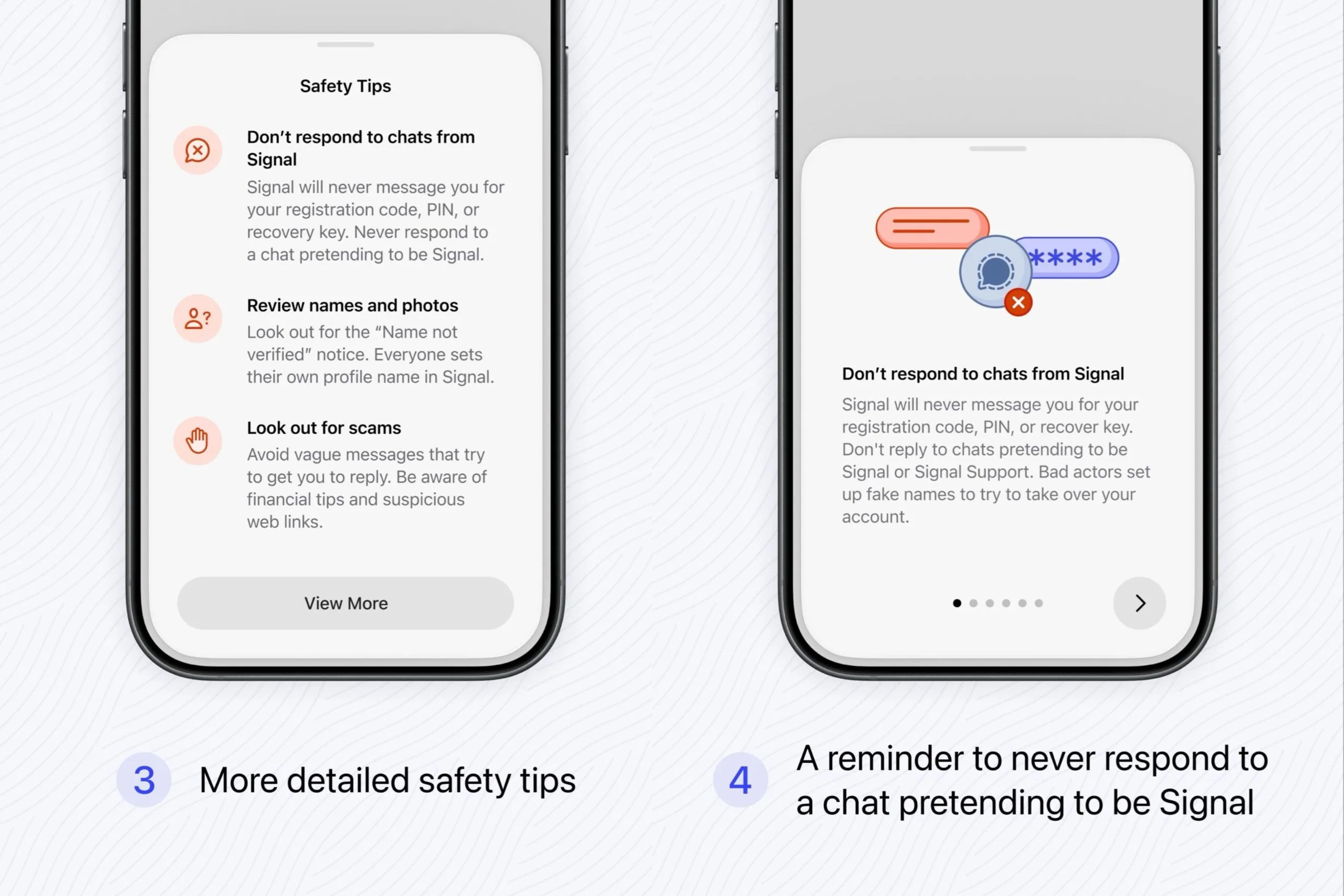
In‑App Education: How Signal Teaches You to Spot Scams
Beyond simple pop‑ups, Signal has embedded continuous education into its interface to strengthen social engineering protection. You will now see clear instructions not to respond to chats claiming to be from “Signal” or “Signal Support,” because the company will never message you directly inside a conversation to request codes or keys. The app also surfaces safety reminders about vague, generic opening lines that are designed to lure a response, suspicious web links, and chats pushing financial “tips” or investment opportunities. Additional educational prompts encourage you to carefully review each contact and pay attention when Signal warns that it cannot confirm you are speaking to the right person. By bringing these security tips into everyday use, Signal reduces the gap between knowing good security practices and actually applying them in real‑time chats.
How to Use These Features to Protect Your Account
To get the most out of Signal’s new message security features, treat every unexpected message request as a potential risk until proven otherwise. If you see the “Accept Request” screen, pause and confirm who the sender is via a trusted method. If a chat uses the name “Signal,” “Support,” or anything that sounds official, remember the app’s own warning: do not respond to chats claiming to be Signal, and never share your registration code, PIN, or recovery key. Treat the “name not verified” label as a reminder to double‑check identities, especially when the conversation includes links, login prompts, or financial advice. If something feels off, cancel the request, block the contact, and report the profile. These small habits, combined with Signal’s new safeguards, make it far harder for scammers to hijack your account.
Part of a Broader Push for Stronger Account Security
Signal has made it clear that these phishing alerts are only the beginning of a broader security upgrade. The recent additions—unsolicited message warnings, name‑not‑verified labels, and in‑app guidance against impostor accounts—are all responses to real‑world account takeovers driven by social engineering. By explicitly stating that it will never message you for codes or keys and by flagging risky behaviors inside chats, Signal is tightening the boundary between legitimate communication and fraud. This approach reflects a growing recognition that encrypted apps must also help users manage human‑level risks, not just technical ones. Signal has already signaled that more protections are coming, so users can expect the platform to keep refining how it detects and communicates risk. Staying attentive to these prompts is one of the easiest ways to keep your private conversations—and your account—secure.
