Why Signal Is Adding Phishing Alerts Now
Signal is expanding its messaging app security with new in-app warnings aimed at phishing and social engineering protection. The update follows targeted phishing campaigns against high‑risk users such as government officials and journalists, and a wider wave of account hijackings where scammers posed as Signal support. These attacks rarely rely on technical exploits; instead, they trick you into handing over sensitive information like registration codes or PINs. To counter this, Signal now focuses on fake message detection and clear user education directly inside the app, rather than expecting people to read external help pages. The changes are rolling out on both Android and iOS, and Signal has already indicated that they are only the first step in a broader push to strengthen messaging app security for everyone. Understanding how these alerts work is key to keeping your account safe.

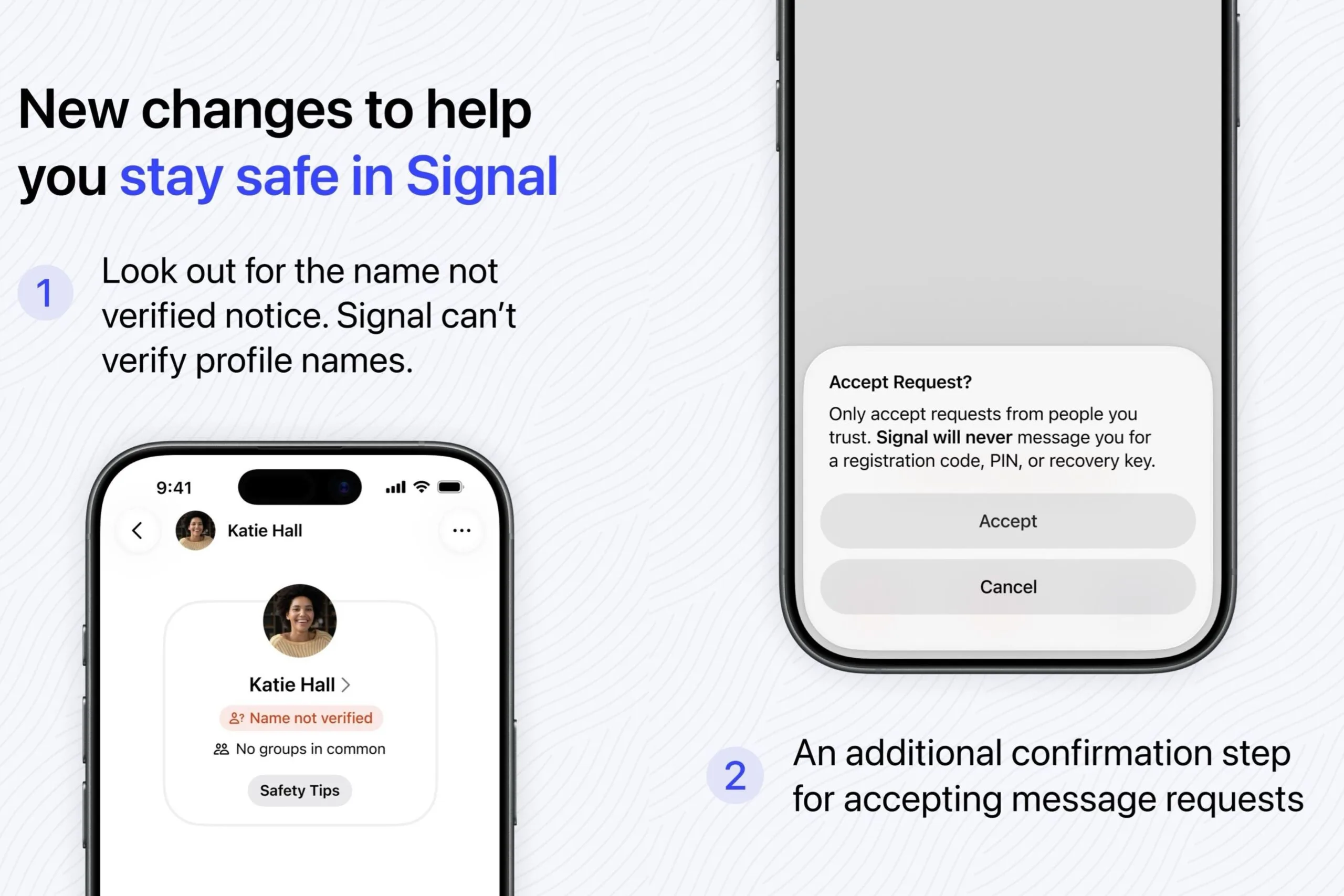
New In-App Warnings: Name Notices and Message Requests
The most visible change is a new “name not verified” notice on profiles. Signal cannot confirm any profile name you see; it’s chosen entirely by the user, which means anyone can pretend to be a colleague, contact, or even Signal itself. The alert is a reminder to verify identities through other channels before trusting what you read. Signal has also upgraded how it handles risky unsolicited messages. When you receive a message request from someone you have not chatted with before, you now see an “Accept Request” pop‑up urging you to only accept chats from people you trust. You can accept or cancel the conversation, similar to other secure messengers, but with stronger emphasis on social engineering protection. These small friction points are intentional, giving you a moment to pause and question whether the new contact is genuine.
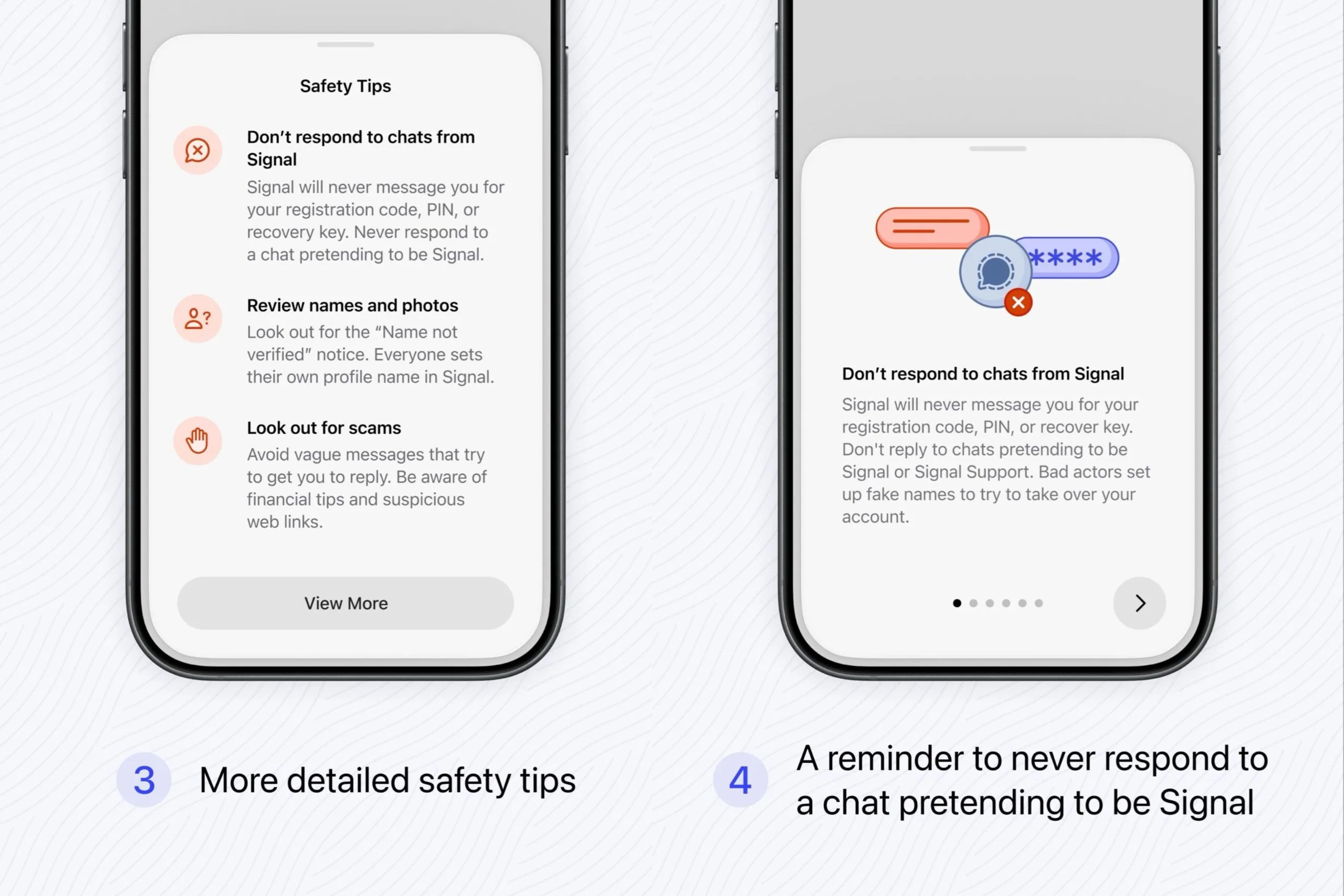
How Signal Flags Suspicious Chats and Fake ‘Signal’ Accounts
Signal’s new safety guidance focuses on fake message detection and impersonation attempts. The app now clearly states that Signal will never message you for a registration code, PIN, or recovery key, and it will not reach out for support issues directly in a chat. Any conversation claiming to be “Signal Support” and asking for codes is almost certainly a scam. You may also see pop‑ups that highlight vague or oddly generic opening lines designed to lure you into replying, suspicious web links, or chats pushing financial “tips.” These patterns are common in phishing attempts and social engineering, where attackers first try to build rapport before asking for sensitive information. By surfacing these red flags in context, Signal helps you recognize that something is off before you click, respond, or share anything that could compromise your account.
Practical Tips: Using Signal’s Tools to Stay Safe
Signal’s new defenses work best when you combine them with cautious behavior. Whenever you see an “Accept Request” prompt, stop and ask yourself how and why this person is contacting you. If the profile claims to be someone you know but carries a “name not verified” notice, confirm using a separate channel, such as an existing verified chat, a call, or email you already trust. Never share registration codes, PINS, or recovery keys in any chat, even if the account looks official. Treat vague intros, random investment advice, or unexpected links with suspicion, and consider blocking or reporting the sender rather than engaging. Regularly review Signal’s educational pop‑ups instead of dismissing them quickly; they are tuned to current scam tactics. With these new Signal phishing alerts and a bit of healthy skepticism, you can significantly reduce your risk of being tricked.
