Privacy by Default: Android 17 Changes the Ground Rules
Android 17 marks a decisive move from privacy as an optional setting to privacy as the baseline. Instead of relying on users to dig through menus or understand complex permission dialogs, Google is changing what apps can see by default the moment the update lands. Three pillars define this shift: a mandatory Contacts Picker, a new local network permission, and a delay on SMS one‑time password (OTP) access. Crucially, most users will never see a new pop‑up or toggle for any of these. Apps targeting the new API level must simply live with the tighter rules. For everyday users, that means less silent data harvesting, fewer background trackers, and more control over sensitive information without extra effort. For developers, it means redesigning flows that previously depended on broad, always‑on access to contacts, Wi‑Fi devices, or incoming text messages.
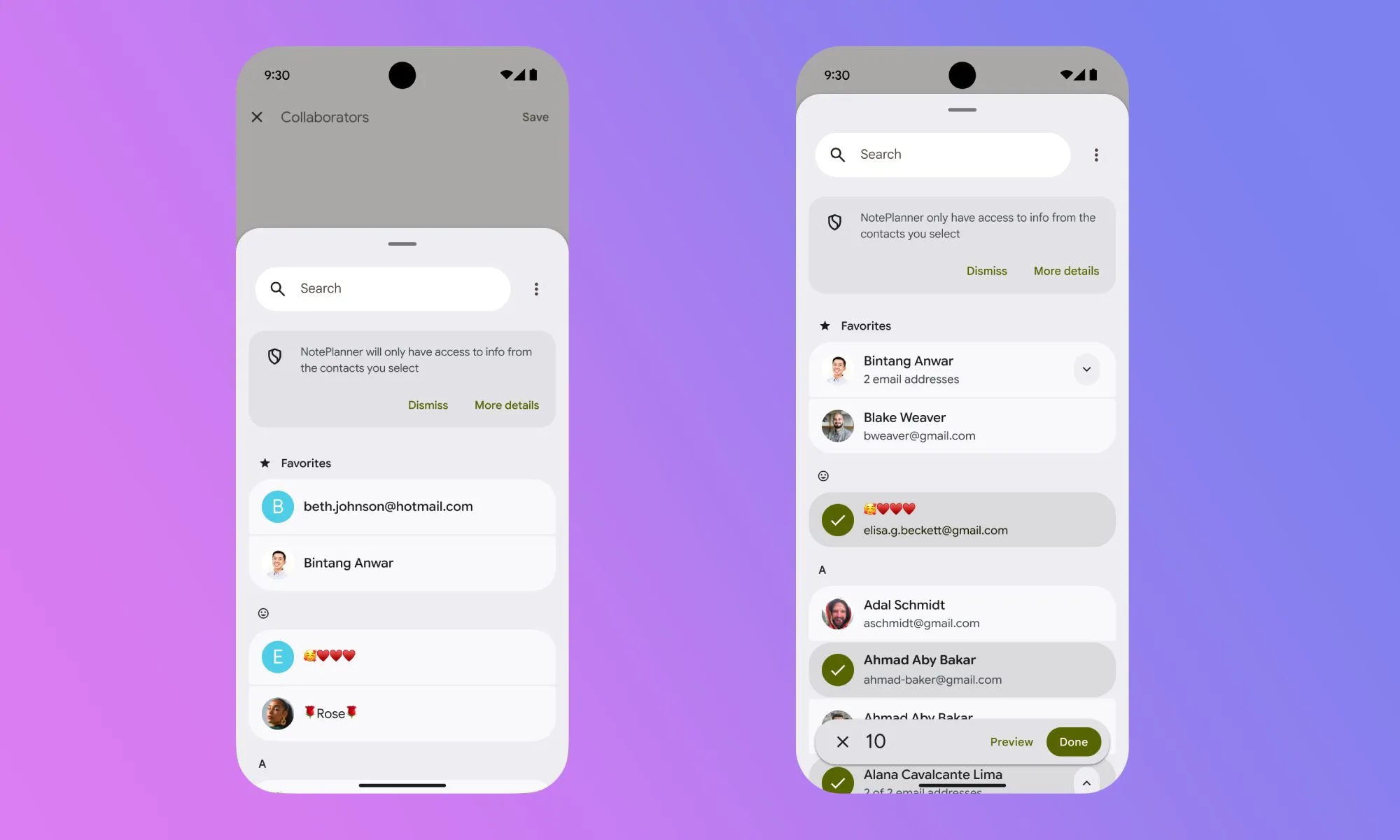
Contacts Picker: Contact-by-Contact Sharing Instead of Full Address Book Access
Historically, granting an app access to your contacts meant handing over your entire address book in one shot. Android 17 fixes this with a system‑level Contacts Picker that mirrors the existing photo picker model. Instead of requesting broad READ_CONTACTS permission, compliant apps invoke a picker intent to request just the contacts they actually need. You select specific entries, and access is temporary and session‑based: once the interaction ends, the app’s window into your contacts closes. The picker also respects work profiles and private spaces, letting you choose items from either without exposing the full datasets behind them. Apps can request only certain fields, such as a phone number without an email address, reducing unnecessary data exposure. For users, this delivers contacts picker security by default; for developers, it removes the option to block features unless you surrender your entire address book.
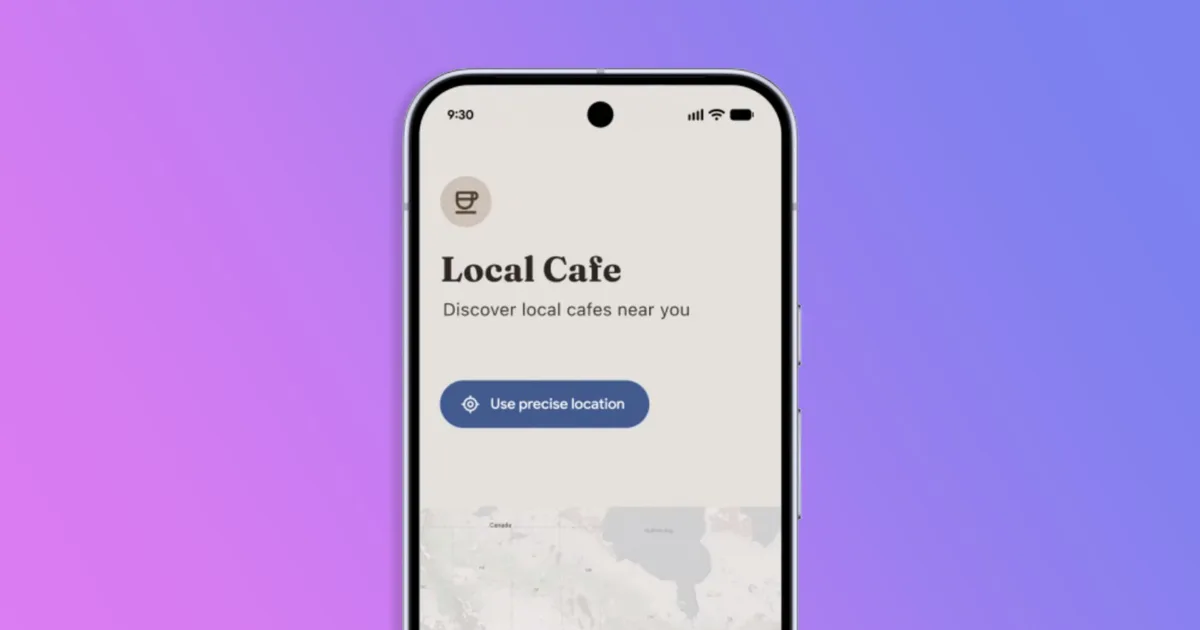
Local Network Permissions: Stopping Silent Scans of Your Home Devices
Before Android 17, almost any installed app could quietly inspect your local Wi‑Fi network, spotting connected devices and nearby access points. This kind of network fingerprinting can help build long‑term tracking profiles that bypass traditional ad‑blocking and privacy tools. Android 17 introduces a new runtime permission, ACCESS_LOCAL_NETWORK, to cut off that free access. Apps targeting the latest API must either request this permission explicitly or use a system‑provided device picker when they need to connect to something on your LAN. In practice, that means only apps with a clear reason—such as home automation or media streaming tools—will surface a prompt for local network permissions. Many others will simply lose the ability to scan in the background. Users get better protection without extra configuration, while developers are nudged toward scoped, user‑visible connections instead of broad, invisible network access.
SMS OTP Protection: A Built-In Delay Against Code-Sniffing Apps
SMS remains the most common second factor for account logins, but it has also been an easy target. Any app with broad SMS read permission could intercept one‑time passwords the moment they arrived, sometimes before you even saw them. Android 17 introduces a three‑hour delay before most third‑party apps can programmatically read messages containing OTP codes, dramatically reducing the value of stolen messages for banking trojans and account‑takeover malware. The delay applies to apps targeting the new API level, with key exemptions: your default SMS app, assistant apps, verified companion apps, and apps using official SMS Retriever or SMS User Consent APIs are unaffected. For users, the experience of receiving codes via text does not change, but SMS OTP protection quietly hardens the system against automated interception. Developers who relied on blanket SMS access will need to adopt the sanctioned, user‑approved flows instead.
What It Means for Users and Developers Going Forward
These Android 17 privacy defaults are part of a broader shift toward automatic safeguards. Alongside the new Contacts Picker, local network block, and SMS OTP delay, Android is also adding finer controls over app location access and on‑screen indicators that highlight when location is in use. For users, the pattern is clear: more protections turn on by themselves, and sensitive data stays locked down unless you actively choose to share it in the moment. For developers, this means designing around granular, time‑bound access instead of permanent, background privileges. App flows that once depended on silent data collection must become transparent and justifiable. In the long run, this privacy‑by‑default architecture should reduce abusive tracking and data hoarding while still allowing legitimate apps to function—provided they respect the new constraints and explain their needs clearly to users.