Why Android 17 Privacy Defaults Matter
Android 17 introduces a major shift in how app permissions work by tightening access to your data before you even touch the settings menu. Three new privacy defaults roll out automatically for apps targeting API level 37: a system-level Contacts Picker, a local network access block, and a delay on SMS one-time password (OTP) access. Together, they change how apps can reach your address book, your home or office network, and your text messages. Unlike traditional app permissions on Android, these protections do not rely on you noticing or responding to prompts. They are baked into the system as the new baseline, which significantly reduces the attack surface for tracking, profiling, and account takeover. You can still override them on a per-app basis when a feature genuinely needs broader access, but the platform now starts from a privacy-first position instead of assuming full trust.
Contacts Picker: Sharing People, Not Your Whole Address Book
Previously, granting contact access on Android meant handing an app your entire address book: every name, phone number, email, and note. Android 17 replaces that model with a system-wide Contacts Picker feature. When an app needs a contact, it calls the picker instead of requesting blanket READ_CONTACTS permission. You then choose exactly which contact or contacts to share, and access is session-based—once you finish the interaction, the app’s window into your contacts effectively closes. The picker also respects work profiles and private spaces, letting you draw from either without exposing your full lists to the app. Developers can ask only for specific fields, such as a phone number without an email, limiting data exposure even further. For users, this means Android 17 privacy controls now make it far harder for simple apps to quietly harvest hundreds of contacts just because you tapped “allow” once.
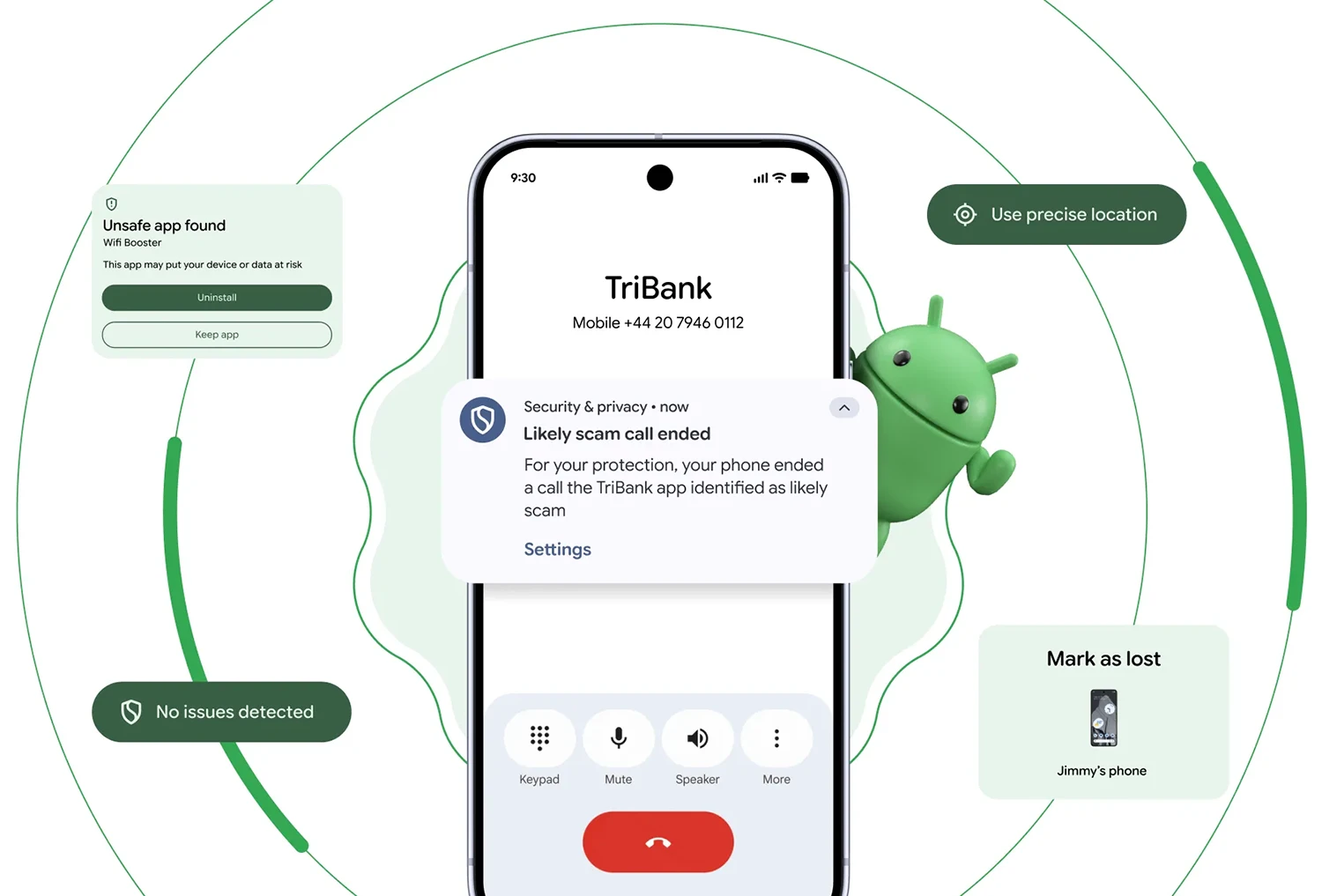
Local Network Access: Blocking Silent Scans of Your Devices
Until Android 17, most apps had silent, open access to your local network. A shopping app, a casual game, or a forgotten utility could scan devices on your router, read nearby access points, and use that information for network fingerprinting—building a persistent profile of you that ignores ad blockers and privacy settings because it never leaves your Wi‑Fi. Android 17 introduces a new runtime permission called ACCESS_LOCAL_NETWORK that changes this behavior. Apps targeting API level 37 must explicitly request permission before they can discover or connect to devices on your local area network. Many will instead use a system device picker, which connects to specific devices without granting broad LAN visibility. Only apps that truly need ongoing communication, like home automation or media servers, should surface a prompt. The quiet scanners simply stop working, shrinking another hidden channel for tracking and tightening app permissions on Android around your home network.
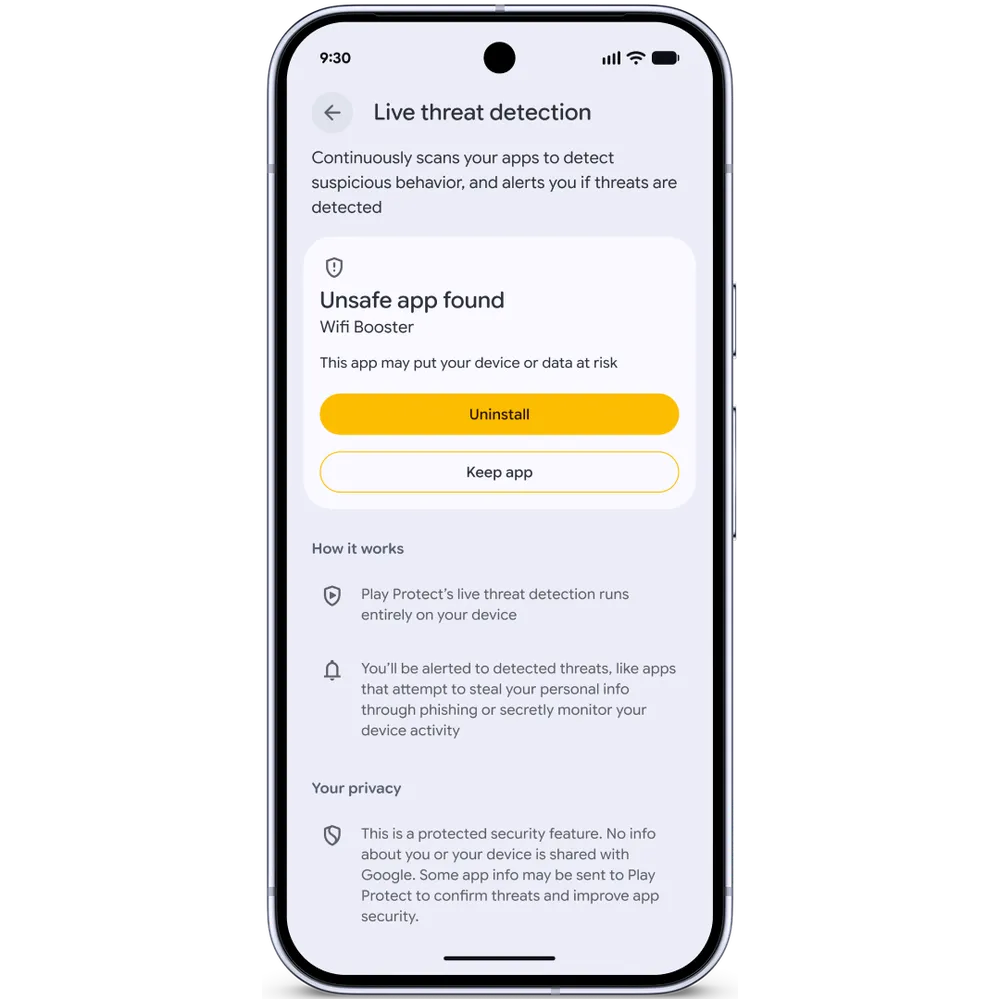
SMS OTP Delay: Strengthening One-Time Password Security
SMS OTP security has long been undermined by apps that request SMS read permission and silently intercept verification codes the moment they arrive. Android 17 plugs this gap by adding a three-hour delay before most third-party apps can programmatically read SMS containing one-time passwords, provided those apps target API level 37. The system carves out sensible exceptions: your default SMS app, assistant apps, and verified companion apps can still function normally. Apps using the official SMS Retriever or SMS User Consent APIs also remain unaffected because they follow user-approved workflows. The practical effect is that opportunistic apps can no longer auto-read fresh OTPs in real time, which helps counter SIM swap attacks and code interception. You can still type codes manually, but automated reading becomes a privileged capability. Combined with other Android 17 privacy measures and new scam protections, this delay makes SMS-based authentication less vulnerable without demanding extra effort from most users.
Living With Privacy-First Defaults (And When to Override Them)
These new Android 17 privacy defaults are designed to be invisible most of the time. You may never see a permission dialog for contacts, local network access, or SMS OTP reading because many apps will adapt to the system pickers and approved APIs. When you do encounter prompts—such as an app requesting local network access or broader SMS permissions—it is a signal to pause and consider whether that request matches the app’s purpose. Granting access remains possible, but the expectation flips: apps must justify why they need more than the safer defaults. For everyday users, this means less silent data collection, fewer paths for scammers and trackers, and stronger protection against account hijacking. For developers, it nudges design toward granular, minimally invasive permissions. The net effect is an Android ecosystem where privacy is not an advanced setting but the starting point for how apps interact with your data.