DeepL’s AWS Expansion Turns Infrastructure Into a Political Question
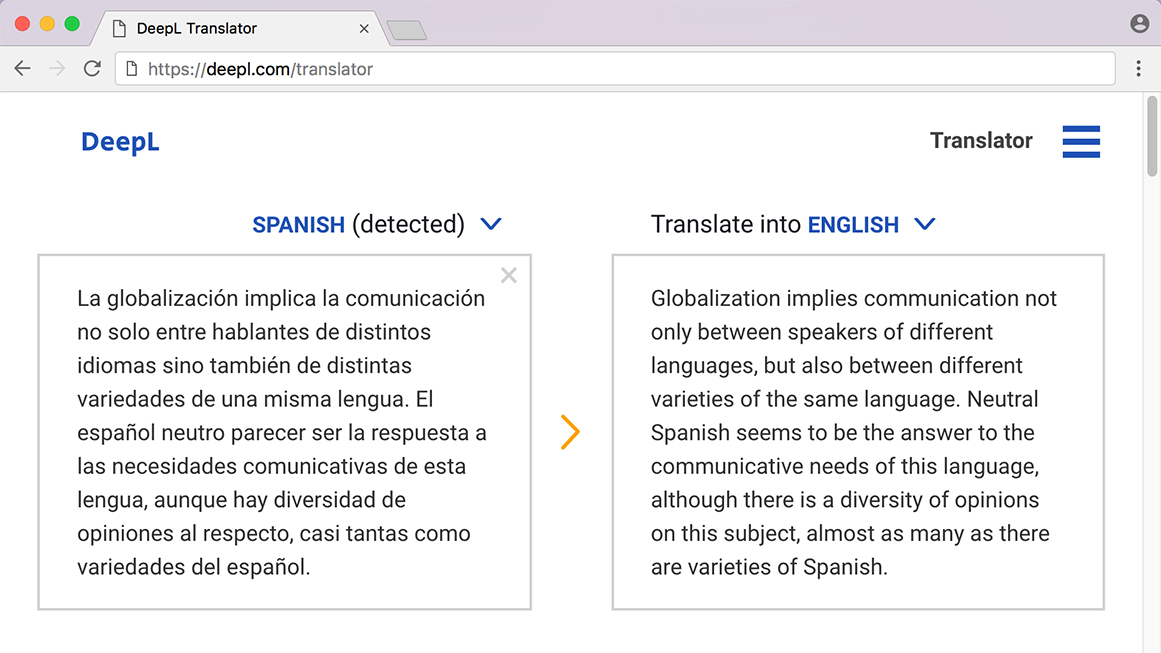
When DeepL added AWS as a sub-processor on April 23, it framed the shift as an engineering upgrade: wider global reach, lower latency, and higher availability for its Language AI platform. Standard processing moved away from a Europe-only default, aligning the DeepL translation service with the global footprint of a major hyperscaler and allowing existing AWS customers to deploy instantly through familiar procurement channels. Yet a change that might normally be seen as routine infrastructure tuning has become a lightning rod. Industry figures warn that leaning on AWS infrastructure could weaken the region’s strong position in professional machine translation and deepen dependence on U.S.-controlled platforms. What used to be a technical decision now doubles as a referendum on how far regional vendors can go in outsourcing compute while still claiming to embody European cloud sovereignty ideals.
Quality, Speed and Control: The Buyer’s Three-Way Trade-Off
For enterprise buyers, DeepL’s AWS route crystallises a familiar trade-off between translation quality, procurement speed, and tight data controls. Existing AWS customers can plug DeepL into their environment almost immediately, keeping billing, identity management, and audit trails inside systems they already trust. That speed matters when the same language engine is expected to serve support teams, legal departments, and internal knowledge tools simultaneously. But public-sector bodies and highly regulated industries interpret the same setup through a stricter lens. Security reviewers probe where default processing happens, whether AWS data residency can be guaranteed, and how deviations are documented for internal audit. Within a single organisation, cloud architects may celebrate the frictionless rollout, while compliance officers see a governance risk that clashes with formal cloud-sovereignty mandates. DeepL’s choice effectively forces customers to declare whether operational convenience outweighs discomfort with non-local infrastructure.
Sovereignty by Design or by Option? DeepL’s Data Promises
DeepL has tried to separate infrastructure dependence from data exposure, pitching its service as a GDPR compliance cloud option even as it broadens its footprint via AWS. The company emphasises that paid-service text remains protected and is not used for model training without customer consent. It also highlights SOC 2 Type II certification, encryption, access controls, audit logs, and GDPR-aligned safeguards on its security page. For customers with stricter needs, DeepL still offers a more constrained residency lane that keeps processing closer to home. Yet the shift in the default path complicates the story: optional controls can look insufficient when internal policy expects sovereignty by design rather than by exception. The result is a two-track proposition—one path optimised for AWS-based scale and performance, another optimised for regional reassurance—leaving risk-averse buyers to decide whether a configurable setting is enough to satisfy cloud-sovereignty expectations.
Why a Single Vendor Deal Matters for the Wider Cloud Landscape
DeepL’s AWS partnership fits a broader pattern of regional tech champions quietly choosing U.S. hyperscalers as they push for global growth. Translation has been one of the few AI segments where regional vendors are perceived as commercially strong, making the infrastructure choice symbolically charged. Policymakers want faster AI adoption but also worry about a future where critical digital services sit atop non-local clouds. To respond, providers like AWS have promoted offerings such as an AWS European Sovereign Cloud, designed to reassure buyers that stricter regional control is possible. Yet DeepL’s controversy shows that naming a sovereign product is not enough; the default architecture and everyday procurement routes still drive perception. As more vendors follow similar paths, the gap between formal sovereignty rhetoric and practical cloud dependencies risks widening, turning each high-profile partnership into a test of how much foreign infrastructure reliance regulators and buyers will tolerate.