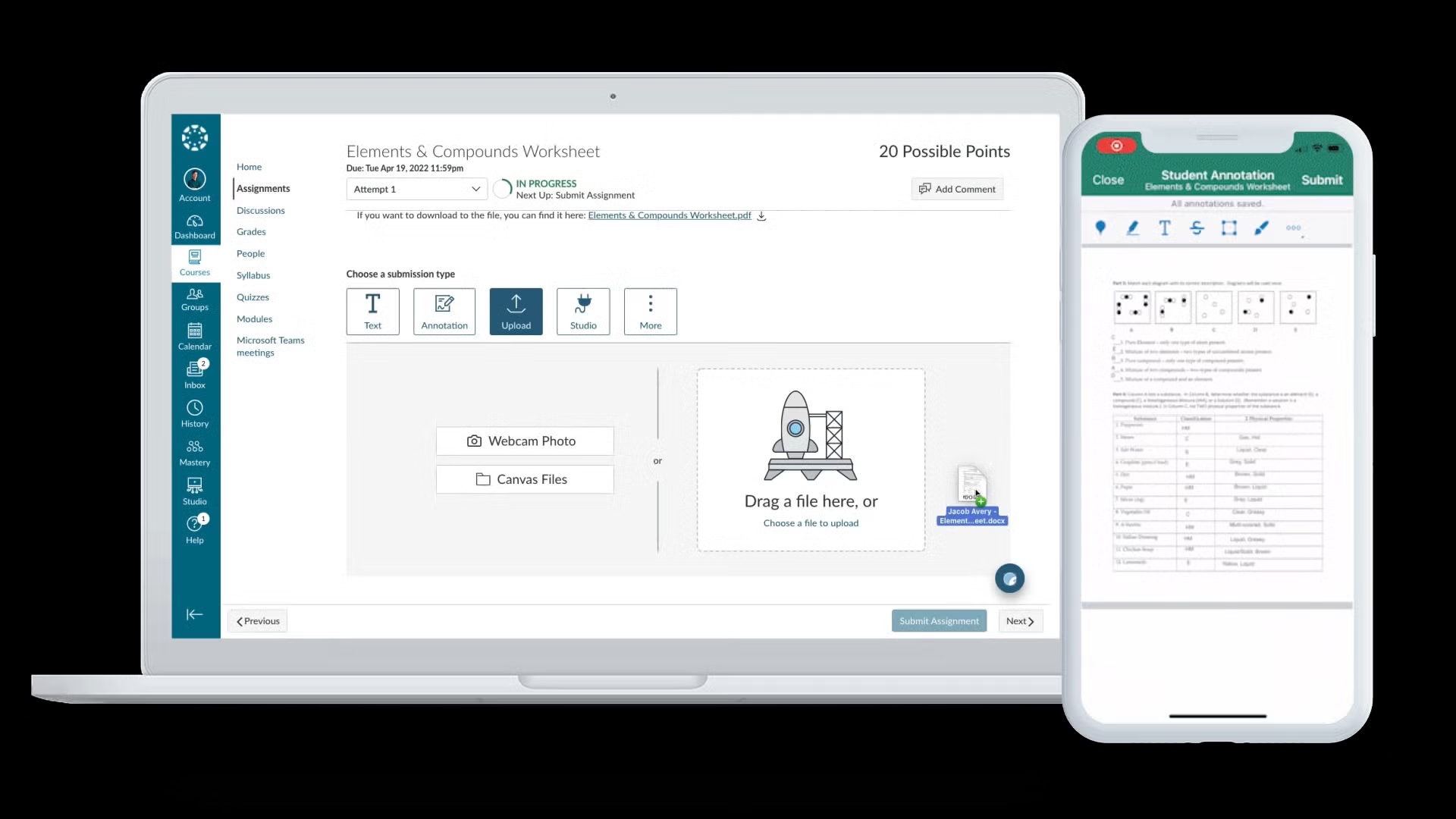
What Happened in the Canvas Data Breach
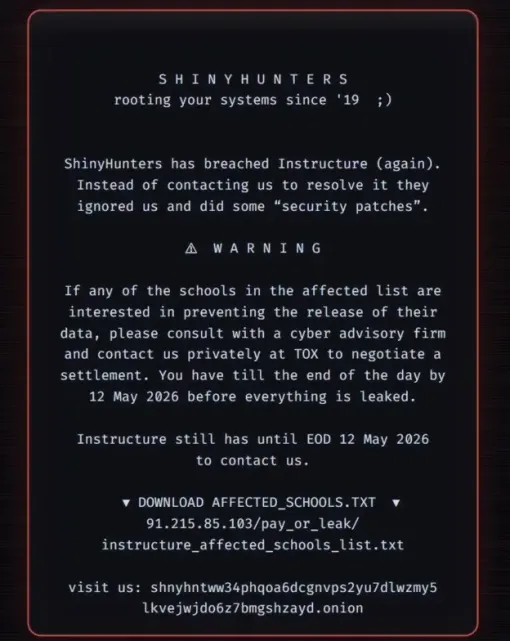
Instructure, the company behind the Canvas learning platform, recently confirmed a major security incident involving the cyber extortion group ShinyHunters. The attackers exploited an issue related to Canvas “free-for-teacher” accounts and allegedly infiltrated the company twice over the past year. On 29 April, Instructure detected unauthorised activity, followed by further incidents in early May. ShinyHunters claimed to have stolen 3.5 terabytes of data and as many as 280 million records, affecting roughly 9,000 institutions. The stolen information reportedly includes names, email addresses, messages, and student ID numbers, as well as “several billions of private messages among students and teachers,” according to the group’s ransom note. The timing, during peak exam season, led to widespread service outages and forced some universities to postpone assessments. While services have now been restored, the breach underscores the high stakes of education platform security.
Ransom Payment and Its Impact on Cybercrime
Instructure has acknowledged reaching a settlement with ShinyHunters and paying an undisclosed ransom to prevent the release of the stolen Canvas data. The company says it obtained “digital confirmation of data destruction” and commitments that the data has been returned, copies deleted, and affected institutions will not be further extorted. However, law enforcement agencies such as the FBI consistently advise against paying ransoms. Investigations into other cyber gangs show that attackers often retain copies of stolen data even after payment, leaving victims exposed to future leaks or resale. Security experts warn that paying ransoms may incentivise further attacks, especially in sectors like education where exam schedules and operational dependency create strong pressure to restore services quickly. The Canvas data breach therefore raises difficult questions about ransom payment impact, ethics, and the long-term effect on cybercrime in the education sector.

Which Institutions and Users Are Affected?
The Canvas data breach has potential consequences for millions of students, educators, and staff. ShinyHunters published a list of more than 8,800 affected institutions, and operations were reportedly disrupted at roughly 9,000 universities, colleges, and schools using Canvas. In some cases, students saw ransom notes appear directly on their screens during online exams, forcing universities such as Mississippi State University to postpone assessments. In Ireland, both the University of Galway and Munster Technological University experienced Canvas outages and service disruption following the hack. Because Canvas is widely used across higher education, schools, and training providers, the compromised data is not limited to a single campus or region. Even though Instructure says services are now fully operational and that the attackers agreed not to extort institutions further, users whose data passed through Canvas should assume their personal information may have been exposed.
Practical Steps for Institutions to Strengthen Security
Universities and colleges using Canvas should treat this incident as a catalyst to reassess education platform security. First, work with Instructure to confirm which data sets, user groups, and time periods are affected, and ensure breach notifications comply with relevant regulatory requirements. Second, enforce strong identity and access management: require multi-factor authentication (MFA) for all staff, faculty, and students, review single sign-on integrations, and immediately disable unused or legacy accounts such as “free-for-teacher” profiles. Third, harden monitoring and incident response: increase logging around learning management systems, set up alerts for unusual login patterns or mass data exports, and rehearse response plans for platform outages during exams. Finally, ensure contracts with edtech providers include clear security obligations, incident reporting timelines, and data protection standards. Treat third-party platforms as extensions of your own network, not separate, low-risk services.
How Students and Educators Can Protect Their Data Now
Individuals who use Canvas should act on the assumption that some of their information may have been exposed. Start by changing your Canvas password and any other accounts that reuse the same or similar password. Enable multi-factor authentication wherever possible, especially on email and university accounts that link to Canvas. Monitor inboxes, student portals, and financial accounts for suspicious activity, such as unexpected password reset emails or messages requesting personal details. Be wary of targeted phishing: attackers may leverage stolen names, email addresses, and message histories to craft convincing scam emails that appear to come from lecturers, administrators, or classmates. Avoid clicking links or downloading attachments from unsolicited messages, even if they reference real courses or recent assignments. Finally, follow updates from your institution’s IT or security team, as they may introduce new login procedures or additional safeguards over the coming weeks.