From Tap to Approval: What Happens in Those Two Seconds
When you hold your phone or watch near a card reader, a surprisingly complex security dance begins. The device and terminal talk over near-field communication (NFC), a short‑range wireless link that only works at a distance of a few centimetres. On top of that, the global EMV standard defines how cards, banks, and payment networks authenticate each other and approve the purchase. In practice, that means your device never just “shouts” your card number. Instead, it follows a strict script: you unlock a digital wallet, confirm your identity with a face scan, fingerprint, or PIN, and only then does a tiny, tamper‑resistant chip release cryptographic payment data. The terminal passes this data through the merchant’s systems to the payment network and your bank. Within moments, the bank runs risk checks and sends back an approve or decline message. All of this feels instant, but it’s a carefully orchestrated flow designed to keep card details hidden at every step.
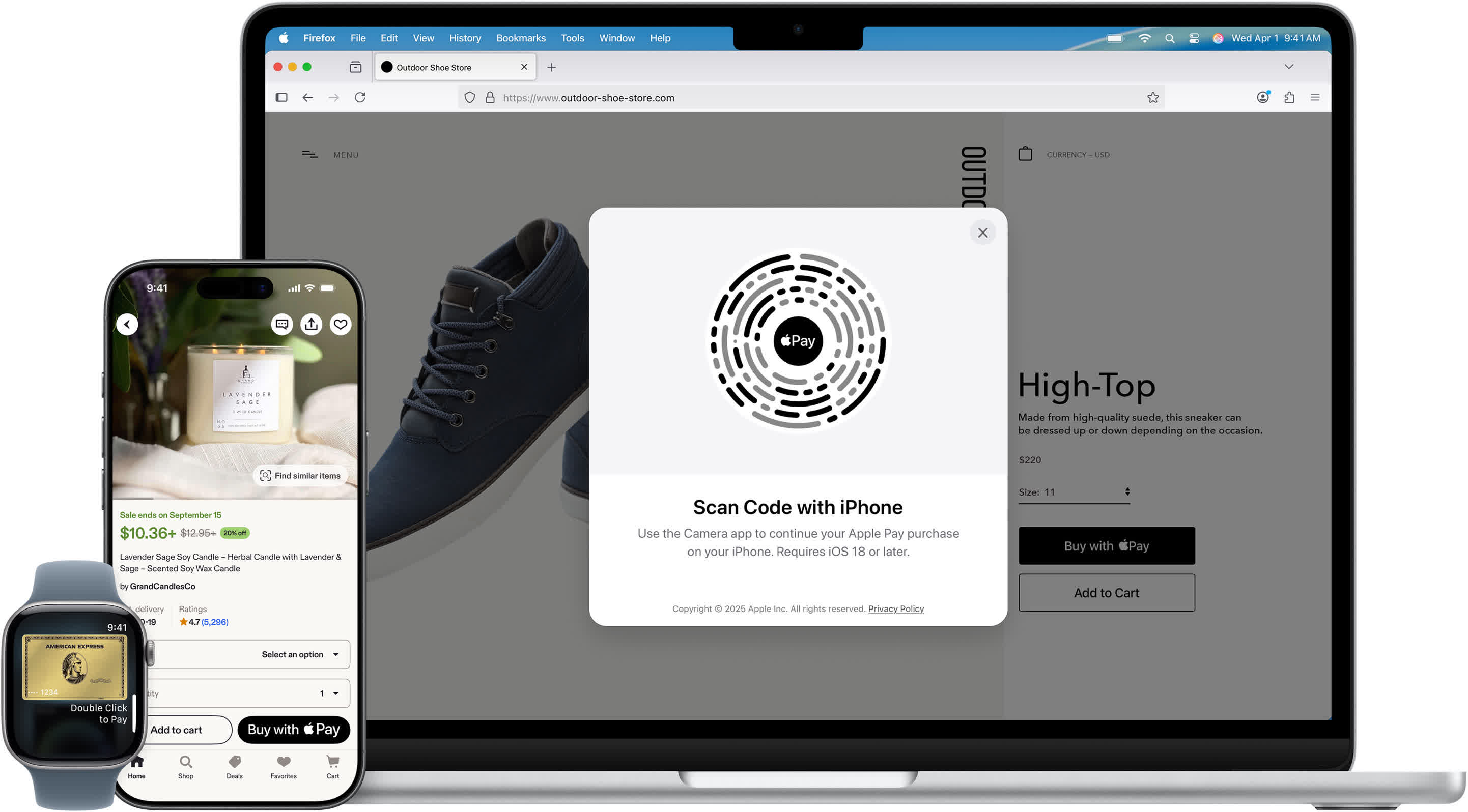
Payment Tokenization Explained: Turning Card Numbers into Safe Stand‑ins
The most important idea in contactless payment security is tokenization. Instead of storing or transmitting your actual card number, your wallet uses a substitute called a payment token. In systems like Apple Pay, this token is often called a Device Account Number, or DAN, and it is created when you first add a card to your digital wallet. Here’s how it works in simplified terms. Your wallet sends your card details to your bank, which contacts a Token Service Provider that follows EMV standards. That provider generates a unique token plus special cryptographic keys, and your bank sends this bundle back to your device. From then on, tap‑to‑pay transactions use the token, not the real card number. Even if a hacker copied this token from a merchant’s database, it would be useless elsewhere. It is tied to a specific device and heavily constrained, so it cannot be reused like a normal card number.
Inside the Two‑Second Journey: Real‑Time Authorization and Dynamic Codes
When you authorize a purchase, your device’s secure chip combines the token with transaction details such as the amount and merchant data. It then generates a cryptogram—essentially a cryptographic proof that this specific device approved this specific transaction. At the same time, a dynamic security code, similar in spirit to a CVV, is computed using a key shared only with your bank. This package travels from the merchant’s terminal to their payment service provider, which wraps it in a 3D Secure message and forwards it to the card network. Because the network sees a token instead of a card number, it calls back to the Token Service Provider to recover the actual card details. The bank verifies the cryptogram and dynamic code, checks your account, and returns an approval. The response flows back through the same chain, and the terminal confirms payment—often sending a brief confirmation to your phone. All of this occurs in real time without exposing your true card credentials.
Device‑Level Shields: Secure Elements, Biometrics, and Mobile Payment Cryptography
Beyond the network, contactless payment security depends heavily on the device itself. Modern phones and watches include a secure element, a dedicated hardware chip that stores sensitive data like tokens and cryptographic keys. This chip is isolated from the main operating system, so even a compromised app cannot read payment credentials in usable form. Before the secure element releases any payment data, the device requires strong user authentication—typically Face ID, Touch ID, or a PIN. Once unlocked, the secure element signs each transaction inside the chip, meaning the raw keys never leave in readable form. This is the core of mobile payment cryptography: private keys remain sealed, while only signed, time‑limited messages are sent out. Different wallets implement this in their own ways, but the principle is consistent. Whether you are learning how Apple Pay works or using another digital wallet, your phone is not just a convenience tool; it is a tightly controlled cryptographic device designed to keep your financial life sealed off from prying eyes.