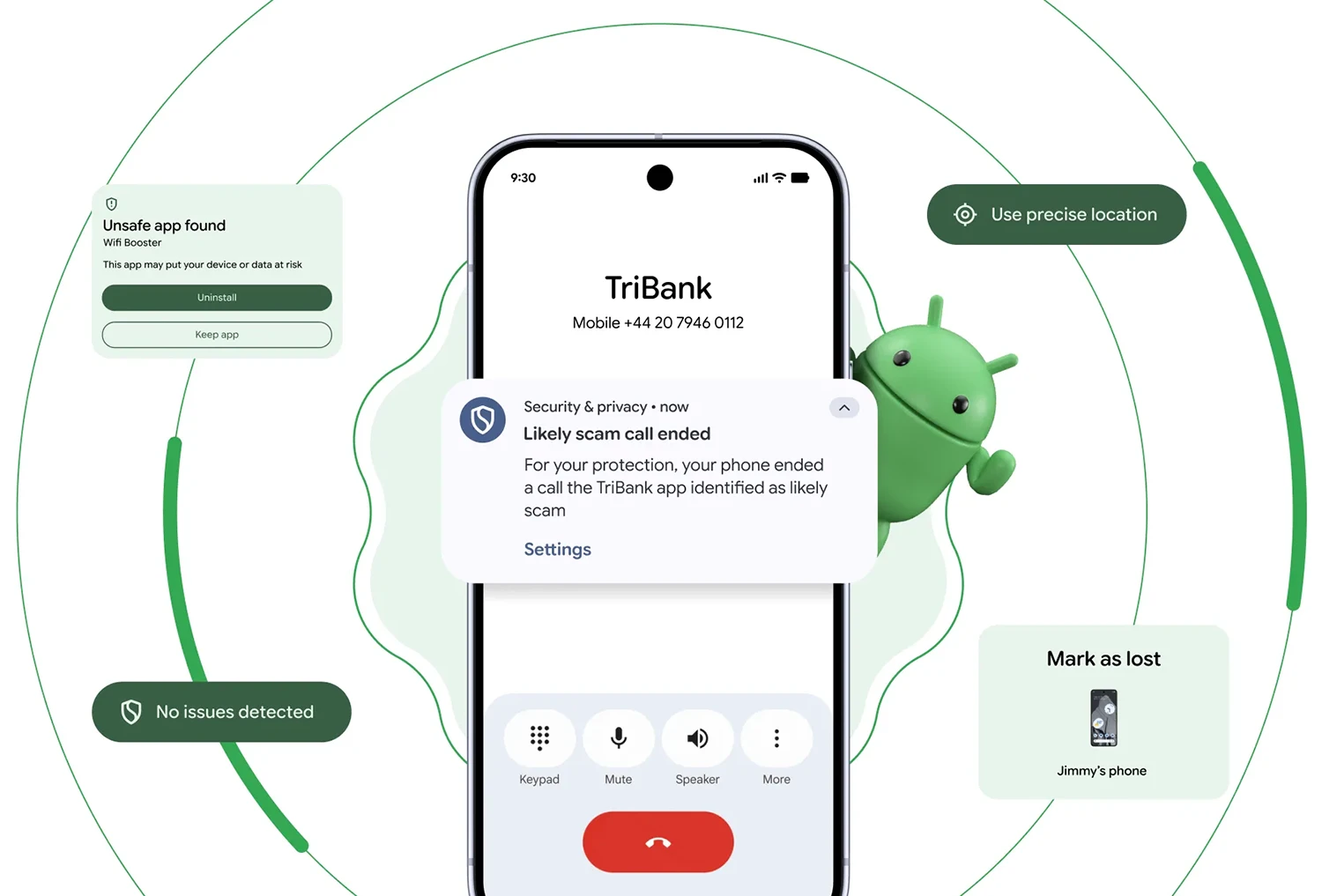
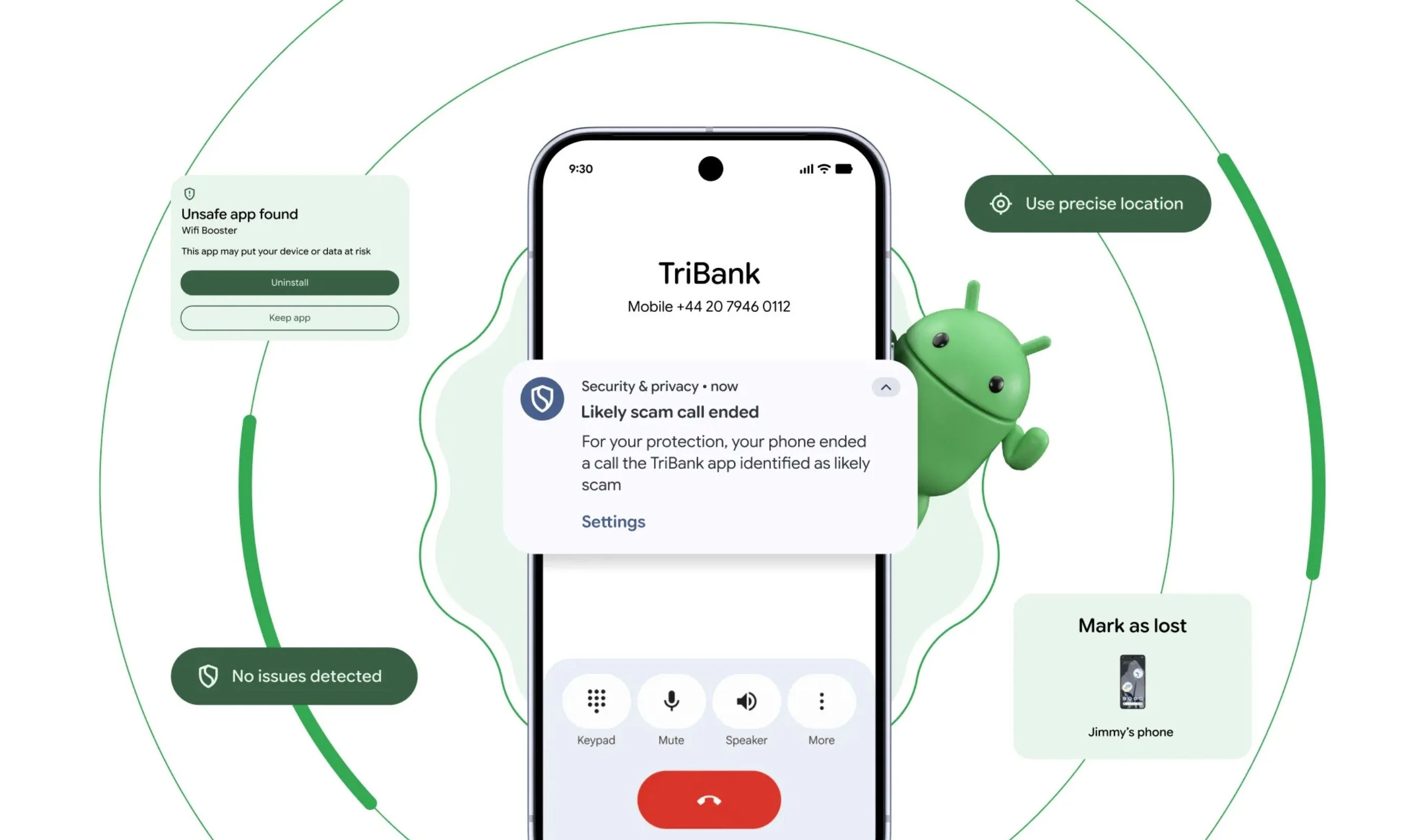
Verified financial calls: Auto-hanging up on bank impersonators
Android’s new verified financial calls feature directly targets phone spoofing scams that have driven an estimated USD 950–980 million (approx. RM4.37–4.51 billion) in annual losses worldwide. When a call comes in claiming to be from your bank, Android now checks in real time with the official banking app installed on your phone. If the app confirms it is not calling you, the system automatically hangs up before you can even pick up. Banks can also tag certain numbers as inbound-only, so any outgoing call appearing from those lines gets dropped instantly. At launch, support includes banks like Revolut, Itaú, and Nubank, with more institutions expected to join. Because this is a system-level feature rolling out to Android 11 and newer devices, it acts as a universal scam call blocking layer that works across dialer apps and mobile networks without any extra setup.
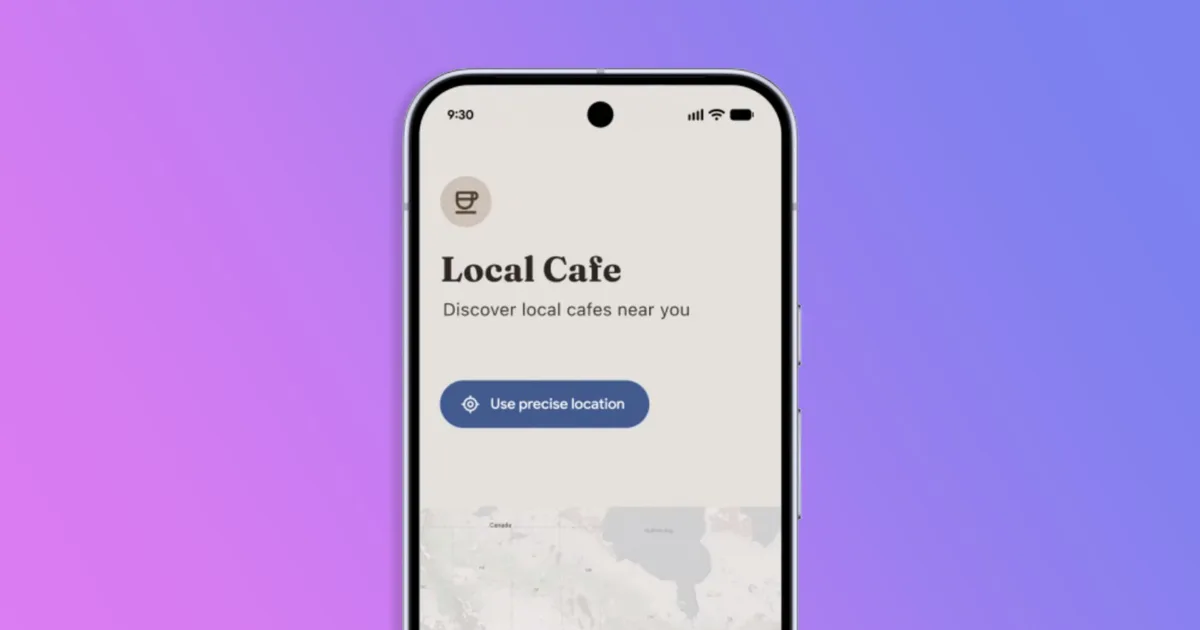
Location privacy and contact controls that work by default
Android 17 tightens location privacy without drowning you in permission pop-ups. A new on-screen location indicator appears at the top of your display whenever any app accesses your location, mirroring existing camera and microphone indicators. Tapping it reveals a “Recent app use” panel where you can instantly dial back or revoke access. There is also a new location button that lets you grant precise location only while an app is open; once you close it, the permission is automatically revoked. On the contacts side, Android 17 replaces all-or-nothing address book access with a system-level Contacts Picker. Apps call the picker instead of grabbing READ_CONTACTS, and you choose specific contacts on a session basis, including from work profiles or private spaces. Access ends when the task ends, so a simple tool or game can no longer quietly retain full, permanent access to your entire address book.
Three privacy defaults: Contacts Picker, local network block, and SMS OTP delay
Beyond user-facing toggles, Android 17 quietly enforces three privacy defaults for apps targeting its latest API level. First, the Contacts Picker becomes the standard path for sharing contact details, replacing broad address book permission with granular, session-based selection of specific contacts and even specific fields like phone number only. Second, a new ACCESS_LOCAL_NETWORK runtime permission stops apps from silently scanning your Wi‑Fi network, a technique used for “network fingerprinting” to track you by the devices and access points around you. Apps now must either request this permission explicitly or use a system device picker when they need to talk to local hardware. Third, Android introduces a three-hour delay before apps can read SMS one-time passwords (OTPs), blocking the most common method malicious apps use to intercept login or payment codes. All three measures are enabled automatically, with no settings to configure and no extra prompts.
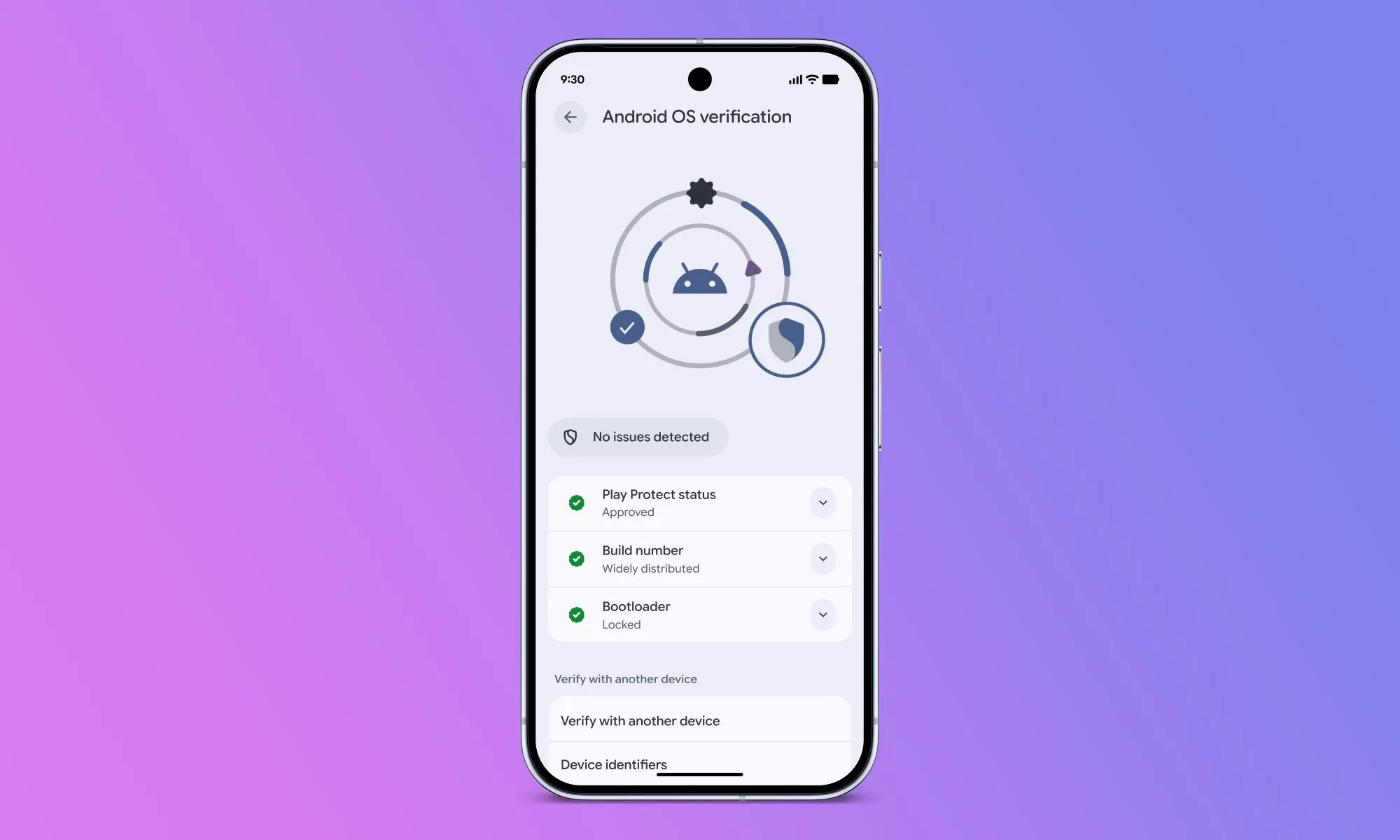
OS verification, app transparency, and Live Threat Detection
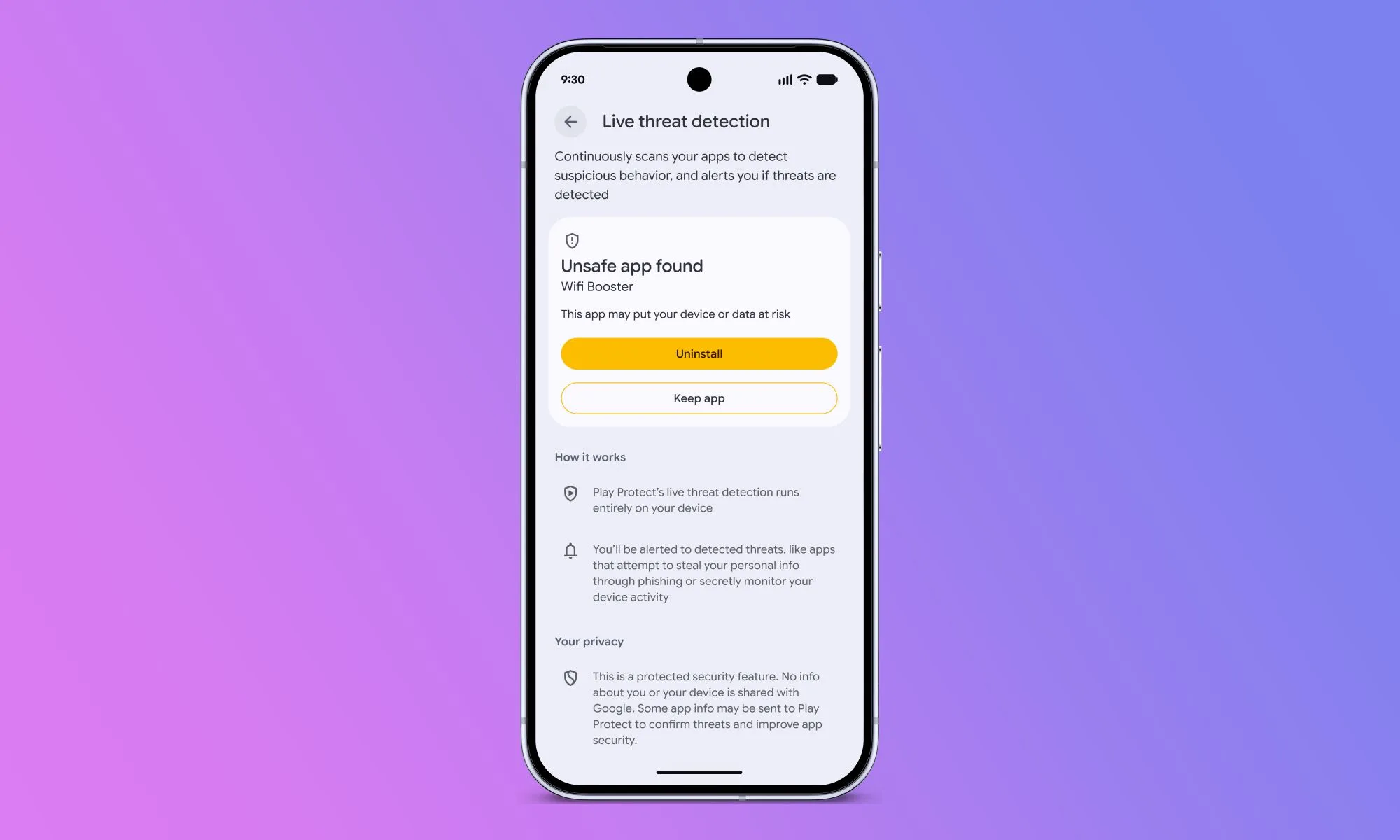
Android 17 adds OS verification, giving you a simple way to confirm that your phone is running an authentic, Google-blessed build instead of a malicious fork designed to imitate stock Android. The verification view surfaces Play Protect status, bootloader state, and build information, and can be cross-checked with another device. In parallel, Google is expanding Android Binary Transparency, backed by a public ledger, to let users and security researchers verify that Google-distributed Android apps and binaries have not been tampered with in the supply chain. On the runtime side, Live Threat Detection’s on-device AI gains dynamic signal monitoring in Android 17. It looks for behaviors such as SMS forwarding, accessibility overlay abuse, apps that hide or change their icons, or software that launches hidden background activity. Google can push new detection rules in real time, turning Android into a moving target for malware and spyware authors.
Twelve proactive upgrades that block scams, malware, and spyware
The verified financial calls system is just one of 12 security upgrades Google is rolling out to automatically block threats. Chrome on Android now checks APK downloads with Safe Browsing and can block known-malicious packages before they reach your storage. Live Threat Detection has been upgraded to watch for apps that secretly forward SMS messages or misuse accessibility features to draw hidden content over your screen. With dynamic signal monitoring arriving in Android 17 on select devices, these AI models can adapt quickly to emerging attack patterns. For high‑risk users targeted by commercial spyware, Advanced Protection Mode layers on USB protections and an Intrusion Logging feature that stores encrypted, tamper-resistant forensic logs in your Google account, capturing events such as unlock times, app installs, network connections, and forensic-tool attachment attempts. Together, these changes create a multi-layered defense that runs mostly in the background, reducing the chances that a single mistake leads to a major compromise.