Why Apple’s Latest Security Updates Demand Immediate Attention
Apple has released a sweeping Apple security update for iPhones, iPads, and Macs, closing more than 60 critical security flaws across current and older operating systems. The updates focus on high‑impact components such as WebKit, the kernel, Wi‑Fi, and sandbox protections—precisely the areas attackers typically chain together in advanced mobile and desktop exploits. iOS 26.5 patches multiple kernel and WebKit issues, App Intents bugs, and other vulnerabilities that could allow apps to gain elevated privileges or escape their sandbox. Even though Apple reports no evidence that these flaws are being actively exploited, the mix of kernel-level bugs, WebKit vulnerability fix entries, and sandbox escapes means the risk is too serious to ignore. Users running older macOS, iOS, and iPadOS versions are also being covered, showing Apple’s continued support for devices that are years out of date—but only if you install the updates.

Inside iOS 26.5: Over 60 Fixes for Kernel, WebKit, and Sandbox Escapes
iOS 26.5 patches a dense cluster of critical security flaws affecting iPhone kernel security, WebKit, and app isolation. Six kernel-level bugs were fixed, including issues like CVE-2026-28951, which could allow an app to obtain root privileges, and CVE-2026-28943, reported by Google’s Threat Analysis Group. These kinds of bugs can undermine core system protections by enabling arbitrary kernel code execution or leaking sensitive memory. On the WebKit side, roughly a dozen vulnerabilities were addressed, such as CVE-2026-28962, where malicious web content could expose private user data. Apple also fixed CVE-2026-28995 in App Intents, a flaw that could let a malicious app escape its sandbox. Security experts note that kernel memory issues, WebKit bugs, and sandbox escape weaknesses are often chained together in modern mobile attacks, making the iOS 26.5 patches particularly vital for iPhone 11 and newer devices.
Critical Fixes for Macs and Older iPhones and iPads
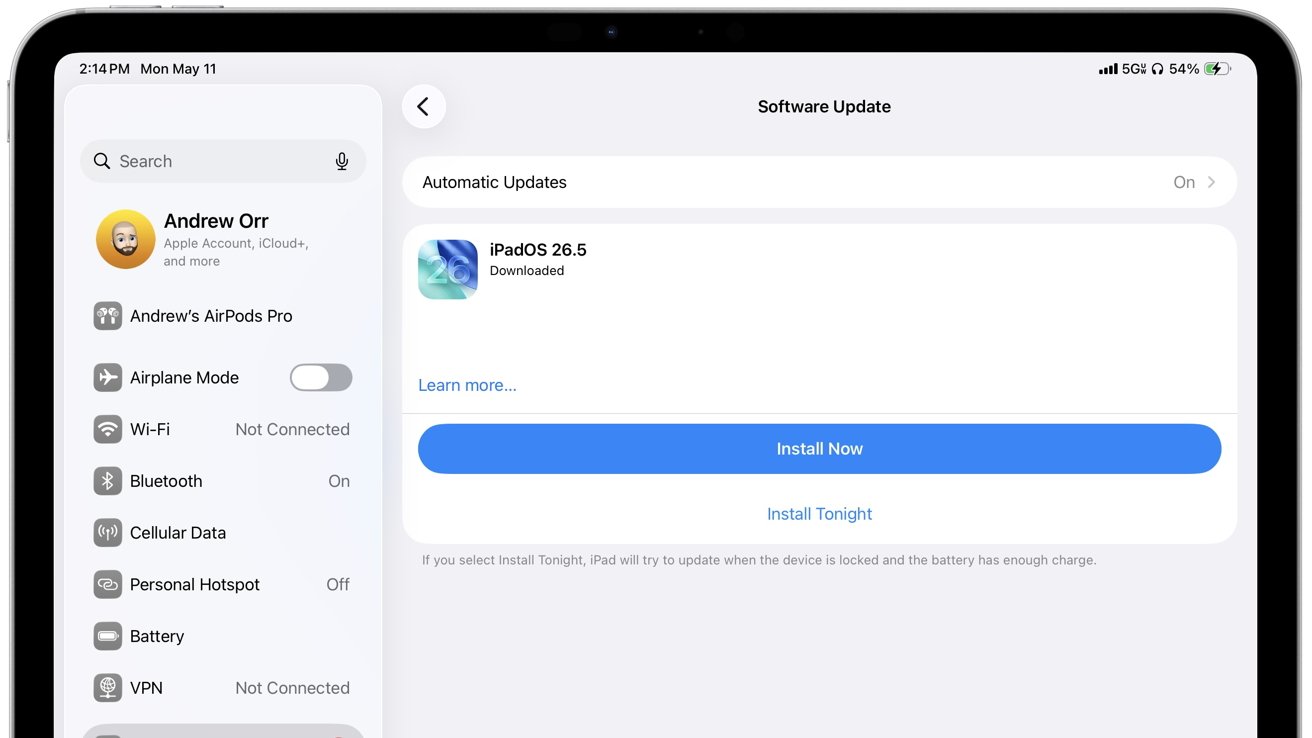
Apple’s May 11 security release is not limited to the latest iPhones. macOS Tahoe 26.5, along with Sequoia 15.7.7 and Sonoma 14.8.7, delivers extensive patches for Macs, covering privilege escalation, sandbox escape, denial-of-service, Gatekeeper bypass, and arbitrary kernel-level code execution flaws. On the mobile side, Apple shipped iOS 18.7.9 and iPadOS 18.7.9 for iPhone XS, iPhone XR, and the seventh‑generation iPad, as well as iPadOS 17.7.11, iOS 16.7.16, and iOS 15.8.8 for older hardware. These releases address WebKit vulnerabilities, Wi‑Fi flaws, kernel memory issues, and a Notification Services bug where deleted alerts could remain on-device. Notably, Apple is still maintaining hardware going back to devices like the iPhone 6s and early iPad Pro models. However, receiving these protections requires updating promptly; staying on outdated versions leaves WebKit, Wi‑Fi, and kernel weaknesses exposed across older iPhones, iPads, and Macs.

Why WebKit and Wi‑Fi Vulnerabilities Are Especially Dangerous
Many of the most serious issues addressed in this Apple security update involve WebKit and Wi‑Fi—components that sit at the heart of everyday device use. WebKit powers Safari, embedded in‑app browsers, App Store previews, and countless web views on iOS and macOS. Newly patched flaws could bypass Content Security Policy protections, leak sensitive information, crash browsing sessions, or corrupt memory when you visit a booby‑trapped website. Similarly, fixed Wi‑Fi vulnerabilities include an out-of-bounds write leading to arbitrary code execution with kernel privileges, and denial-of-service attacks triggered by crafted wireless packets or mDNSResponder traffic. Because these subsystems handle untrusted data from the internet and local networks, bugs here can often be exploited remotely without obvious user interaction. That’s why the WebKit vulnerability fix set in iOS 26.5 patches, macOS Tahoe 26.5, and related updates is critical for protecting both browsing and app security.
How to Prioritize Updates and Protect Your Devices
To reduce risk, install the latest updates on every Apple device you own, prioritizing systems used for sensitive tasks such as banking, email, or password management. iPhone 11 and newer models should move to iOS 26.5 immediately to benefit from the 60+ critical security flaws resolved there, especially the iPhone kernel security and WebKit fixes. Compatible iPads should likewise update to the latest available iPadOS branch, while Macs should upgrade to macOS Tahoe 26.5 or their newest supported version. After updating, restart devices so kernel and networking patches fully apply. Beyond patching, avoid sideloaded or untrusted apps, unknown configuration profiles, suspicious links, unsecured Wi‑Fi networks, and unsolicited file downloads. If you own devices that no longer receive security updates, do not use them for sensitive data. The combination of advanced exploits and AI‑assisted discovery means staying current with Apple security updates is now a baseline requirement, not an optional best practice.