What the Canvas Data Breach Reveals About Modern EdTech Risk
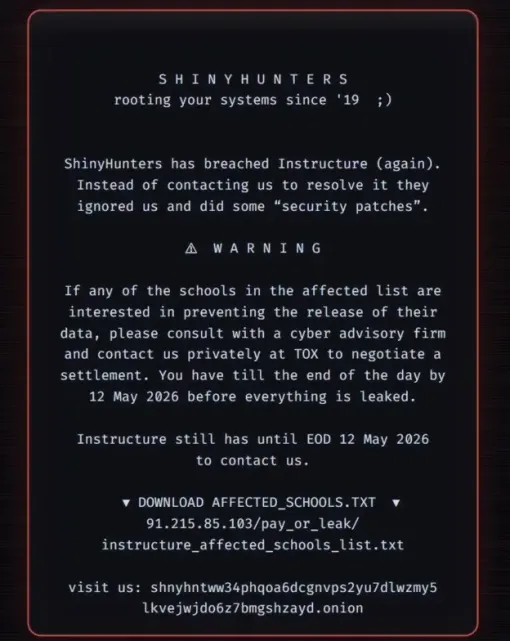
The recent Canvas data breach is a stark reminder that EdTech security threats are now systemic, not hypothetical. Instructure, the company behind Canvas, disclosed that an extortion group known as ShinyHunters infiltrated its infrastructure twice within a year, ultimately stealing 3.5 terabytes of data and impacting roughly 9,000 institutions. The attackers claimed access to 280 million records, including names, email addresses, messages, and student ID numbers, and even threatened to leak billions of private messages between students and teachers. The targeting of a cloud-native learning platform during peak exam season shows how attackers now look for maximum leverage and disruption, not just technical weaknesses. For universities, this Canvas data breach demonstrates that relying on a single learning management system creates a critical dependency: when it fails, teaching, assessment, and student communications can all be paralysed at once.
Ransomware Settlements and the New ‘Consent or Pay’ Reality
Instructure’s decision to reach a settlement with ShinyHunters underscores a troubling evolution in university cybersecurity. The company confirmed it obtained “digital confirmation of data destruction” and a promise that institutions and students would not be further extorted, but did not disclose what was paid or conceded. This move runs against longstanding advice from agencies such as the FBI and the UK’s National Crime Agency, which warn that ransom payments fund the cybercrime ecosystem and offer no guarantee that data is truly deleted. Investigations into other groups, like LockBit, have shown that attackers often keep stolen information even after being paid. The Canvas incident illustrates a growing “consent or pay” dynamic: tech providers are pressured to accept attackers’ terms to maintain operations and customer trust. Universities must assume that any ransomware settlement leaves residual risk and should plan as if stolen data may resurface later.
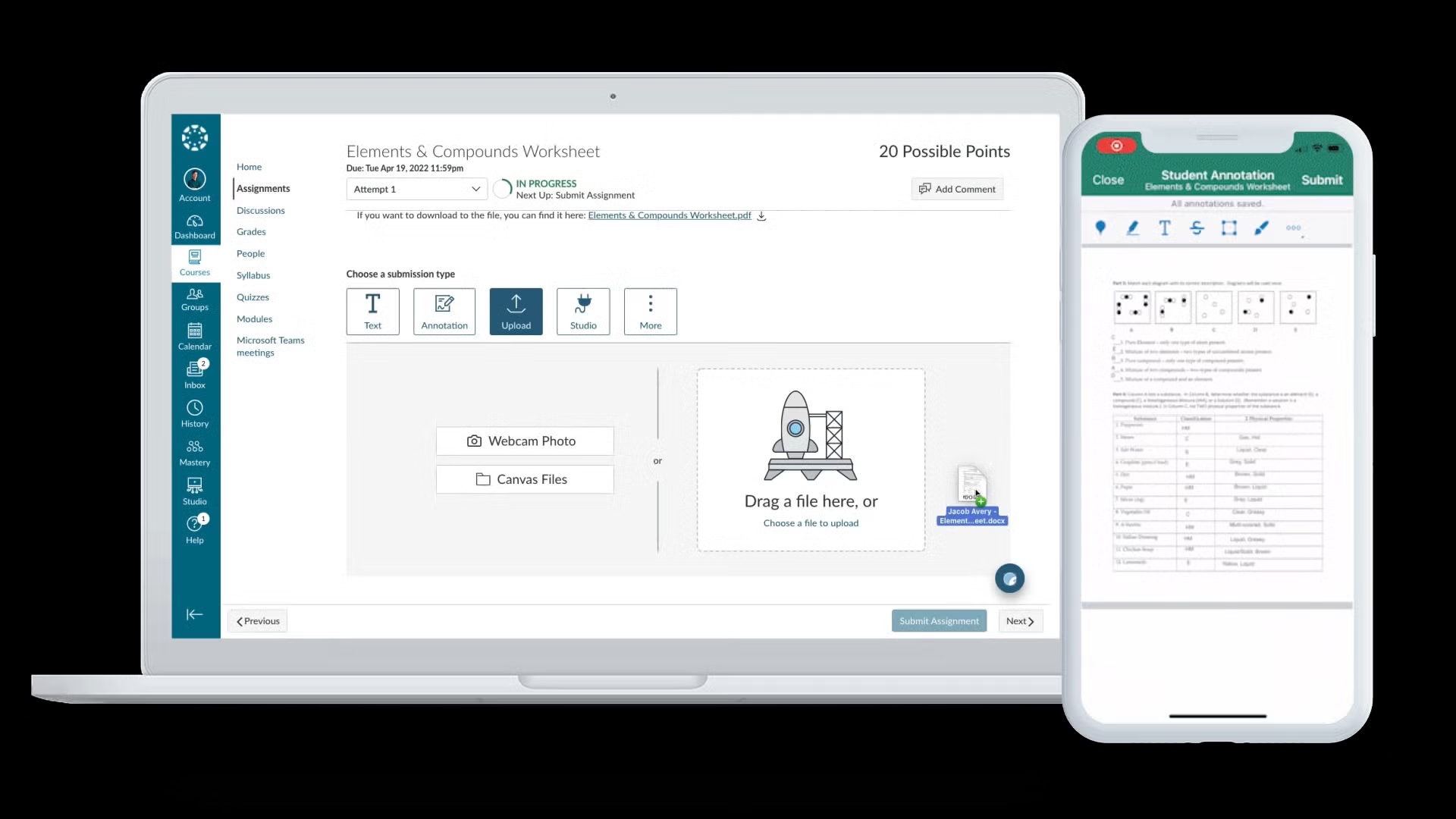
Operational Fallout for Universities and Students
The Canvas data breach was not just a back-end security event; it directly disrupted teaching and exams. Institutions using Canvas, including University of Galway and Munster Technological University, reported service outages that interrupted access to coursework and assessment tools. At Mississippi State University, students even saw ransom notes appear on their screens mid-exam, forcing postponements. ShinyHunters deliberately timed the attack for exam season, maximising pressure on both Instructure and its academic customers. This highlights how university cybersecurity is now inseparable from academic continuity planning: a compromised LMS can halt online assessments, delay graduations, and undermine student confidence. The incident also exposed how dependent many institutions have become on a single EdTech platform for everything from messaging to grading. Universities should treat LMS disruptions as a core business risk, not just an IT problem, and develop contingency plans for teaching and assessment when cloud services fail.

Strengthening University Cybersecurity for EdTech Platforms
To prevent a repeat of the Canvas data breach, universities need to harden their defences around cloud-based EdTech platforms and their own integrations. First, enforce strong identity and access management for staff and students, including multi-factor authentication and strict role-based permissions for LMS access. Second, maintain an accurate inventory of all third-party tools connected to the LMS and apply continuous security monitoring to those connections. Third, universities should require vendors to disclose how features like “free-for-teacher” accounts are secured, and insist on regular third-party security assessments and penetration tests. Data minimisation and segmentation are also crucial: limit the student data stored on external platforms and segregate sensitive information such as ID numbers and assessments where possible. Finally, institutions must ensure logging, anomaly detection, and incident response tooling can detect unusual activity in shared cloud platforms, not just on local networks.
Building Robust Incident Response and Data Protection Protocols
Given the rise of ransomware settlements and sophisticated extortion tactics, universities must assume breaches will occur and plan accordingly. A modern incident response plan should define decision-making authority (including when to involve law enforcement), communication strategies with students and staff, and clear criteria for engaging with third-party providers like LMS vendors. Regular tabletop exercises should model scenarios in which attackers exfiltrate student data and threaten public leaks. Data protection protocols need to prioritise encryption in transit and at rest, strict retention policies for messages and assessment records, and systematic backup strategies that support rapid recovery without paying ransoms. Universities should also clarify contractual obligations with EdTech providers around breach notification, forensic access, and post-incident transparency. By treating EdTech security threats as a strategic governance issue, not just a technical one, institutions can reduce the impact of future attacks and better protect student trust.