Verified Bank Calls Take Aim at Phone Scam Impersonation
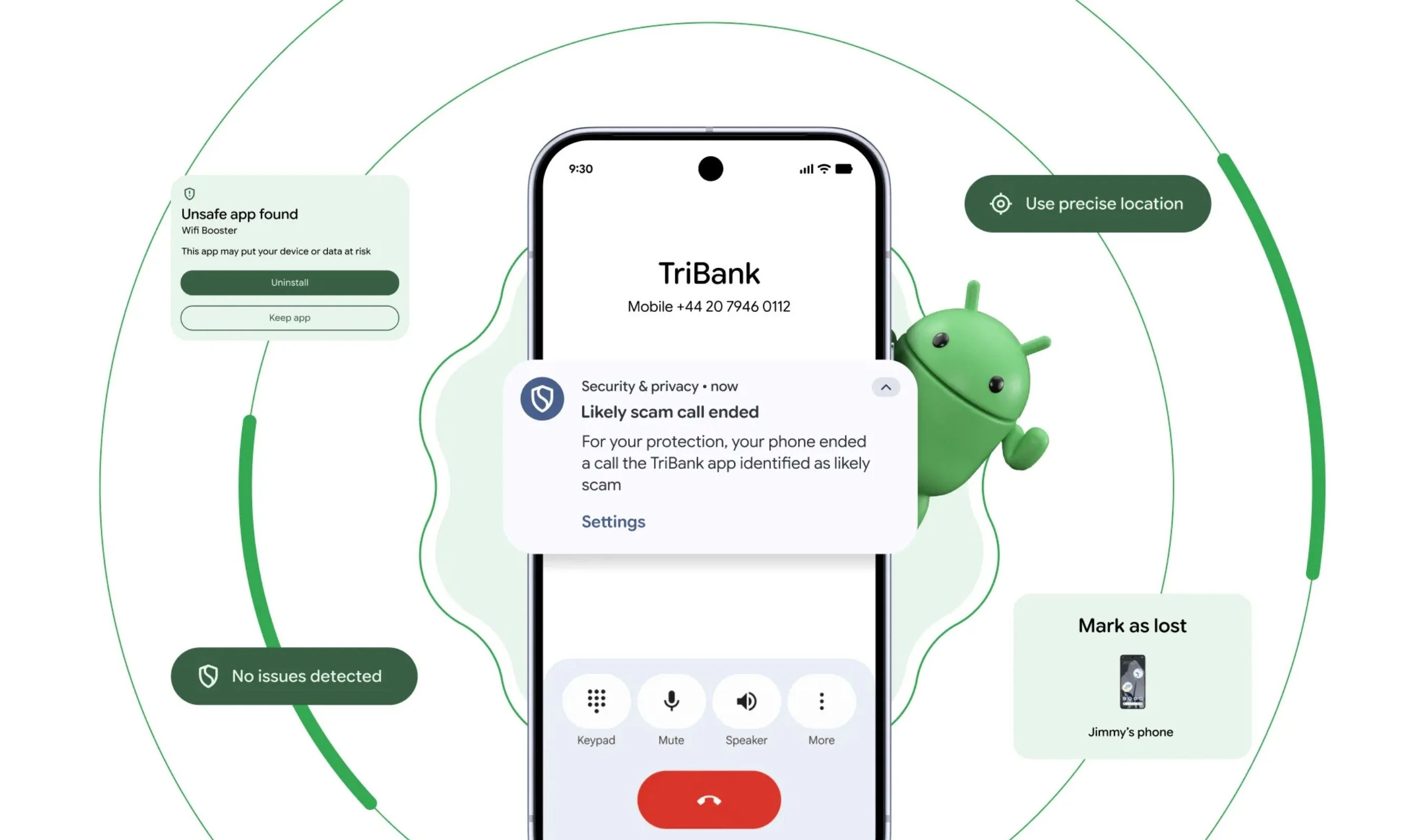
Phone scammers have long relied on spoofed caller IDs to impersonate banks, driving massive fraud losses globally. Android security 2026 upgrades introduce “verified financial calls,” a system-level check that cross‑references incoming calls with the official banking app installed on your phone. When a call claims to be from your bank, Android silently asks the bank’s app whether an outbound call is actually in progress. If the app reports no active call, the system hangs up before the phone even rings, shutting down many impersonation attempts. Banks can also mark certain numbers as inbound‑only, so any outgoing call spoofing those lines is automatically terminated. The feature is rolling out on Android 11 and newer devices with partners such as Revolut, Itaú and Nubank, and is designed to become a core layer of defense against social‑engineering scams built on fake “support” calls.
Theft Protection on Android: From Snatch Detection to Biometric Lockdown
Theft protection on Android is evolving beyond simple remote wipe. New Android 17 capabilities aim to stop thieves from using stolen devices at all. Remote Lock and Theft Detection Lock monitor device sensors for snatch‑and‑grab patterns and can instantly lock the screen when suspicious motion is detected, reducing the window for attackers to disable security. The Find Hub’s Mark as Lost feature now requires biometric authentication before the phone can be unlocked, even if a thief knows the PIN, and it automatically hides Quick Settings while disabling new Wi‑Fi and Bluetooth connections to keep tracking active. Android security 2026 enhancements also tighten PIN brute‑force limits and extend wait times after failed attempts, while exposing the IMEI from the lock screen to help carriers and law enforcement verify ownership. Together, these default‑on defenses make physical theft less lucrative and more easily traceable.
On‑Device AI Monitoring and Malware Blocking
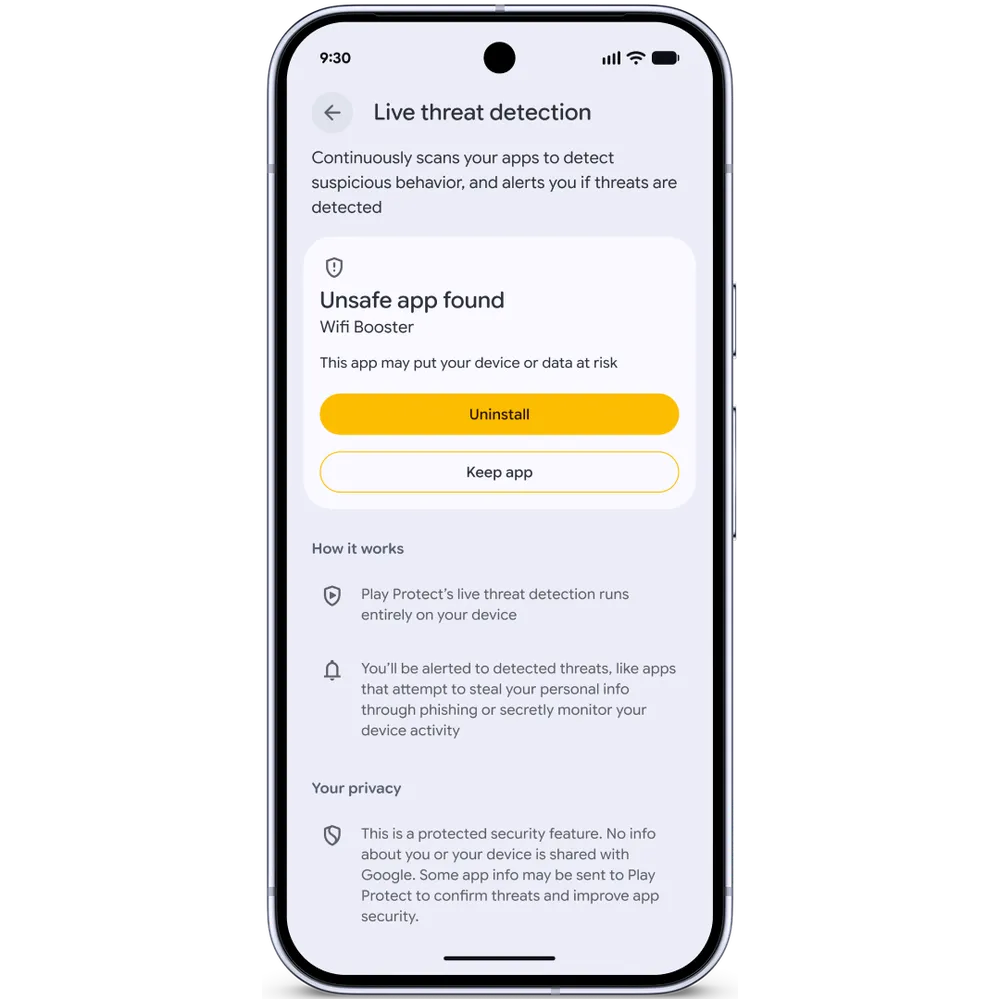
Android’s security roadmap leans heavily on on‑device AI monitoring to catch malicious behavior without exporting private data. Live Threat Detection, running locally on Android 17 devices, watches how apps behave after installation rather than relying only on pre‑install scans. It can flag apps that silently forward SMS messages, abuse accessibility overlays, or hide their icons to run covert tasks. A new dynamic signal monitoring system lets Google push updated detection rules in real time to counter emerging techniques, turning phones into adaptive security endpoints. For malware blocking at download time, Chrome on Android now scans APK files with Safe Browsing and stops known malicious packages before they reach storage. Crucially, all of this inspection happens on the device, maintaining privacy while increasing resilience against rapidly evolving malware and AI‑assisted attacks that attempt to evade traditional signature‑based checks.
Twelve Proactive Defenses: From Spyware Logs to Scam Chat Detection
Google’s 12 new proactive security upgrades focus on blocking threats before users even notice them. Advanced Protection Mode, a one‑toggle hardening profile, now strips accessibility service access from apps that aren’t declared accessibility tools, shuts off device‑to‑device unlocking, and adds scam detection for chat notifications. Intrusion Logging creates tamper‑resistant forensic records of device unlocks, app installs, network connections, and connections from tools such as forensic analyzers, offering vital evidence in spyware investigations. USB protection on supported Pixel devices counters physical exploitation via debug ports. Meanwhile, Android OS verification uses a public append‑only ledger to prove a phone is running an official build, and post‑quantum cryptography strengthens the data protection stack against future decryption attempts. Collectively, these measures work alongside verified bank calls and malware blocking to create a multilayered shield that addresses everything from consumer scam calls to sophisticated surveillance operations.
Private AI, Location Controls and the Future of Android Security
Beyond headline features like theft protection and verified bank calls, Android security 2026 upgrades quietly reshape everyday privacy. A new one‑time precise location button lets users share GPS data only while an app is actively performing a task, backed by a top‑of‑screen indicator showing recent location access. A redesigned contact picker enables apps to request a single contact or specific fields instead of the entire address book, and permissions can be kept temporary. Android also hides one‑time passwords from most apps for three hours, limiting exposure to credential‑stealing overlays. Under the hood, AISeal with pKVM isolates AI workloads in a hardware‑backed environment alongside Private Compute Core and Private AI Compute, so sensitive ambient data can be processed in a verified, on‑device enclave. Together, these controls signal a shift toward security architectures where on‑device AI, fine‑grained permissions, and verifiable system integrity reinforce each other against both human and machine‑driven attacks.