From Tap to Approval in Two Seconds
When you make a contactless payment, it feels like magic: double‑click, authenticate, tap, done. In reality, contactless payment security relies on a tightly choreographed exchange that unfolds in just a couple of seconds. Your phone or watch uses near‑field communication (NFC) to talk to the point‑of‑sale terminal at very short range, typically a few centimeters. NFC is just the secure "wire" in the air. The real brains come from the EMV standard, which dictates how cards, devices, banks, and payment networks prove that a transaction is legitimate. In systems like Apple Pay, the device doesn’t simply beam your card number. Instead, it sends carefully structured payment credentials governed by EMV rules. These credentials are checked by the merchant’s payment service provider, card network, token service provider, and your bank, all in real time. Each party verifies cryptographic data before the terminal shows “Approved,” dramatically reducing the risk of card cloning or interception.
Payment Tokenization Explained: Your Card Number Never Leaves Home
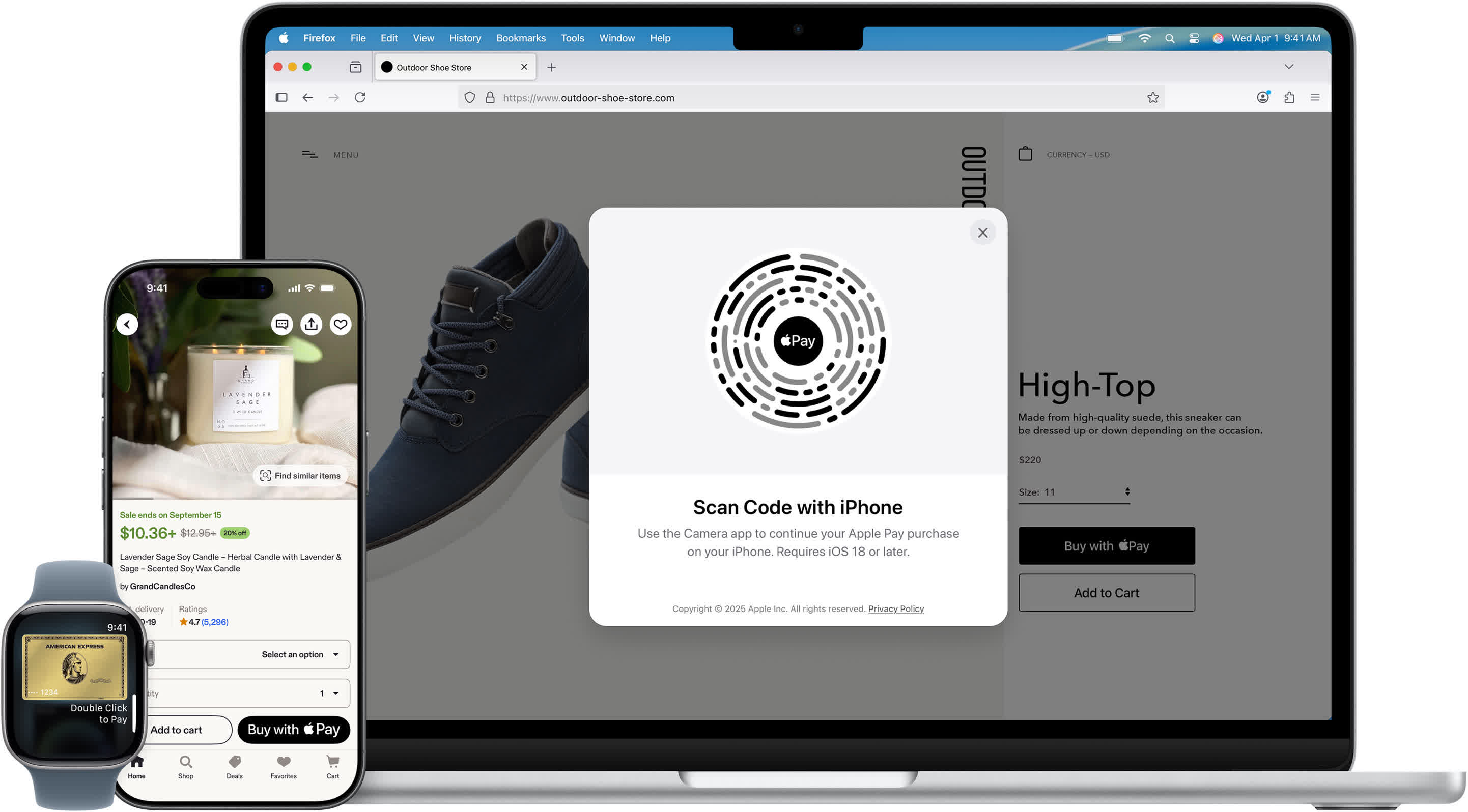
At the core of modern mobile payment encryption is tokenization. Rather than storing or transmitting your actual card number, digital wallets generate a stand‑in called a payment token. In Apple Pay, this is known as a Device Account Number (DAN), created when you add a card to your Wallet. Your card details are sent to Apple, which identifies your bank. The bank then works with a Token Service Provider (TSP) to create a unique token plus associated cryptographic keys. That token is provisioned into the device’s secure element, a tamper‑resistant chip similar in spirit to a security module in a computer. Each device gets its own unique token, so your phone, watch, and laptop never share the same credential. During payments, the merchant sees only this token, not your real card. Even in the event of a retailer data breach, attackers would obtain disposable identifiers that are useless outside their intended context.
How Apple Pay Works During a Tap: Cryptograms and Dynamic Codes
Once you authenticate with Face ID, Touch ID, or a PIN, the secure element springs into action. It combines the device’s token (DAN), token keys, the transaction amount, and other parameters to generate a unique cryptogram for that specific payment. At the same time, a dynamic CVV is created using a special CVV key that was set up when your card was enrolled. These values are transmitted via NFC to the merchant terminal, then passed to the merchant’s payment service provider (PSP). The PSP decrypts the package and builds a 3D Secure authorization request. Because the payment network only sees the DAN, it forwards the request to the TSP to recover your real card number securely. The TSP validates the cryptogram, returns the underlying card data to the network, and your bank checks the dynamic CVV and account status. Only if everything matches does the approval flow back through the network to the PSP, terminal, and finally your phone.
Why Merchants Can’t See or Reuse Your Payment Data
A key benefit of contactless payment security is that merchants never get your actual card number. They receive the device‑specific token plus transaction‑specific cryptographic data generated on the fly. That token is bound to your device and to strict rules enforced by the bank and token service provider. The dynamic CVV and cryptogram are valid for that transaction only. Because of this design, stolen payment data from a compromised point‑of‑sale system is far less valuable. Attackers can’t reconstruct your real card number from a token, and they can’t replay an old cryptogram or dynamic CVV to authorize a new payment. In many implementations, Apple itself also avoids storing your raw card numbers, relying instead on tokenization. The result is a layered defense: device‑bound tokens, one‑time cryptographic codes, and strict verification by the card network and issuing bank make each tap a controlled, disposable event rather than a reusable credential.
Biometrics and Device Security: The First Line of Defense
All of this cryptography would be less reassuring if anyone could trigger it with a stolen phone. That’s where biometric authentication and secure hardware come in. Before the secure element will release payment credentials, your device must be unlocked using Face ID, Touch ID, or a PIN. This step ensures that the person tapping to pay is the authorized user, not someone who just grabbed your device. The secure element itself is isolated from the main operating system, designed to withstand both software exploits and physical tampering. It stores the DAN and keys in a dedicated environment that normal apps can’t access directly. Even if malware infects your phone, it shouldn’t be able to extract or misuse those secrets. Combined with real‑time bank authorization and tokenization, biometric checks form an additional barrier. In practice, a thief would need your device, your biometric or passcode, and the cooperation of multiple financial systems to complete a fraudulent tap—and that’s an extremely high bar.