Why Older Apple Devices Need Immediate Security Updates
Apple has rolled out a major Apple security update focused on older iPhones, iPads, and Macs that no longer run the latest operating systems. These releases address critical flaws in WebKit, the system kernel, Wi‑Fi components, and app sandboxes—areas attackers often target to gain deep access to a device. While the newest platforms get the largest patch sets, Apple is still pushing essential fixes to legacy systems so long‑owned hardware does not become an easy target. Delaying these updates leaves older operating systems exposed to known weaknesses that researchers have already documented and reported. Even though Apple has not flagged any of the vulnerabilities as currently exploited in the wild, the technical details are now public enough that attackers can attempt to reverse‑engineer them. Updating promptly closes these gaps before they become reliable tools for malware or spyware campaigns.
Which iPhones, iPads, and Macs Are Affected?
The latest macOS security patch set spans multiple generations of Apple’s desktop platform, including macOS Tahoe 26.5, macOS Sequoia 15.7.7, and macOS Sonoma 14.8.7. On mobile, iOS 18.7.9 and iPadOS 18.7.9 cover devices such as the iPhone XS, iPhone XR, and the seventh‑generation iPad. Apple has also issued iPadOS 17.7.11 for the sixth‑generation iPad, the 10.5‑inch iPad Pro, and the second‑generation 12.9‑inch iPad Pro, primarily to fix a Notification Services issue where deleted alerts could remain stored. Even older hardware remains supported via iOS 16.7.16 and iPadOS 16.7.16 on devices like the iPhone X and first‑generation 12.9‑inch iPad Pro, and through iOS 15.8.8 and iPadOS 15.8.8 for devices such as iPhone 6s, iPhone 7, the first‑generation iPhone SE, iPad Air 2, and iPad mini 4, extending critical protection to hardware released more than a decade ago.

The Risks: WebKit, Kernel, Wi‑Fi, and Sandbox Vulnerabilities
These updates deliver a broad WebKit vulnerability fix set, along with patches for an iPhone kernel flaw and other low‑level issues that can undermine core protections. In WebKit—the engine behind Safari, App Store previews, and in‑app browsers—Apple has corrected problems that could bypass Content Security Policy rules, leak sensitive information, crash browser processes, or corrupt memory via malicious web content. Kernel patches tackle root privilege escalation, kernel memory disclosure, integer overflows, out‑of‑bounds writes, race conditions, and Gatekeeper bypasses using crafted disk images or ZIP archives. Networking components also receive important fixes, including a Wi‑Fi vulnerability that could allow arbitrary code execution with kernel privileges, and denial‑of‑service issues triggered by specially crafted Wi‑Fi packets or mDNSResponder traffic. Together, these flaws could allow attackers to escape sandboxes, gain elevated privileges, or quietly access protected user data if left unpatched.
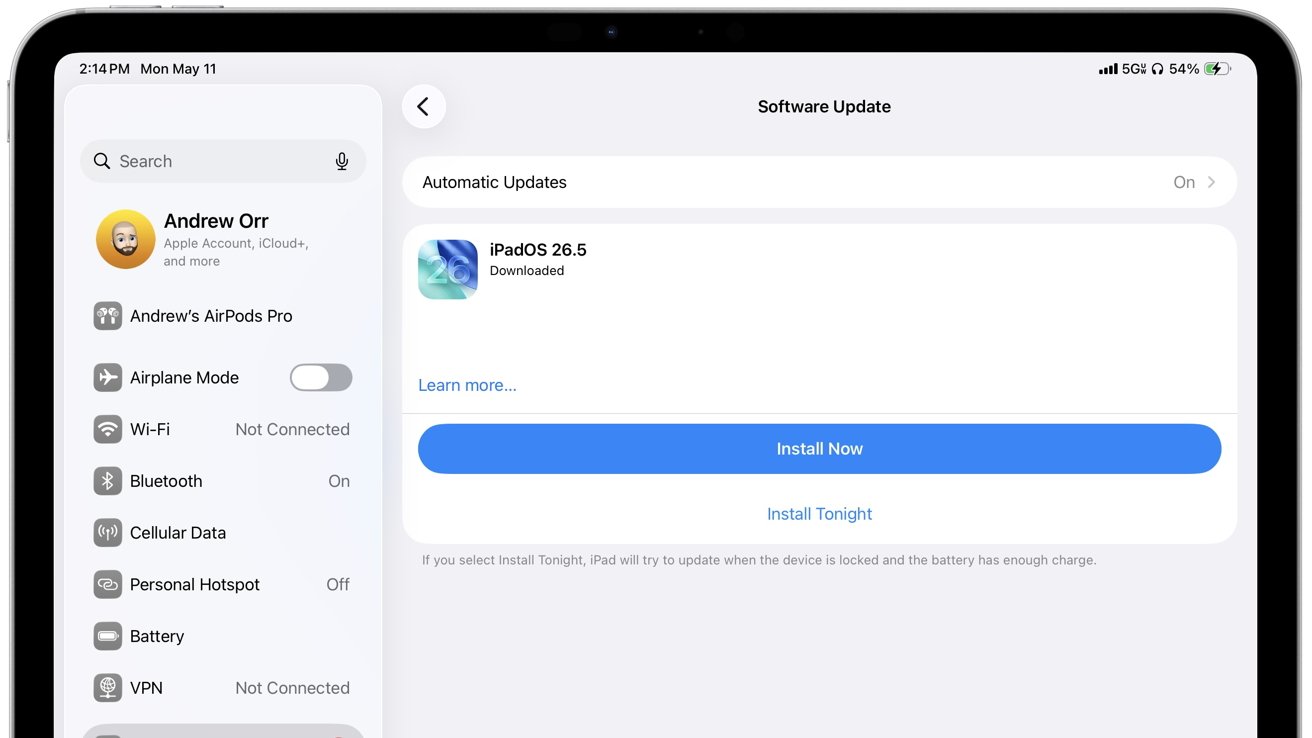
Practical Steps: How to Protect Your Older Apple Devices
To reduce risk, install the latest Apple security update for your device as soon as it appears in Software Update, then restart so kernel and networking fixes fully apply. Prioritize devices used for sensitive activities such as email, work files, or password management, since many of the patched issues involve WebKit, Wi‑Fi, sandbox escapes, and privacy controls. Until you update, avoid clicking unknown links, opening unexpected attachments, or installing apps and configuration profiles from untrusted sources. Steer clear of unsecured or unfamiliar Wi‑Fi networks, which could be used to trigger wireless vulnerabilities. Safari and system browser updates are particularly important because WebKit underpins many apps beyond the browser itself. If you own hardware that no longer receives iOS, iPadOS, or macOS security patches at all, consider reserving it for low‑risk tasks and avoid using it for banking, personal communications, or storing sensitive information.