Why Human-Only Threat Hunting Can No Longer Keep Up
Modern cyberattacks unfold at what security leaders increasingly describe as “machine speed.” Attackers automate reconnaissance, lateral movement, and payload deployment, overwhelming security teams that still rely on manual investigations and ticket-driven workflows. Even well-staffed security operations centers struggle to correlate thousands of daily alerts, extract intelligence from fragmented tools, and turn it into timely, automated threat response. The result is a widening gap between compromise and containment, where minutes or hours of delay can translate into data loss, business disruption, or successful influence operations. This speed deficit is driving a shift toward AI threat hunting and cybersecurity automation, where intelligent systems assist analysts by triaging noise, enriching alerts with context, and proposing next-step actions. Rather than replacing humans, these systems aim to offload repetitive analysis so analysts can focus on higher-value decisions and complex incident command.
Prevyn AI: Turning Threat Intelligence Into Real-Time Defense
Group-IB’s Prevyn AI illustrates how embedded AI threat hunting is reshaping defensive operations. As the cognitive core of its Unified Risk Platform, Prevyn AI taps into a large intelligence data lake built from cybercrime investigations, regional research, and collaboration with international law enforcement. Instead of leaning mainly on open-source feeds, the system is designed to reason about attacker behavior and intent, improving faster threat detection across connected systems. Within Threat Intelligence, it coordinates 11 specialized agents that mirror the investigative logic used in high-tech crime cases, from malware analysis to dark web monitoring. Internal tests showed more than a 20% increase in research quality, measured by accuracy and analytical depth. In Managed XDR, Prevyn AI automates alert analysis, drafts incident reports, and generates structured remediation workflows, enabling automated threat response while letting human operators retain final decision authority.
Governed Automation: Keeping Humans in Control of AI Decisions
One of the most important design choices in modern cybersecurity automation is how much autonomy AI systems receive. Prevyn AI requires human approval before any recommended action is executed, aligning with governance frameworks such as DORA and the EU AI Act. This approval loop is emerging as a template for enterprises that want the speed of automated threat response without surrendering control of high-impact decisions. By automating investigation tasks—correlating indicators, summarizing incidents, drafting remediation plans—AI reduces the manual workload but stops short of executing irreversible changes on its own. This balance addresses concerns about over-reliance on opaque models while still accelerating operations. It also allows organizations to standardize decision criteria, document rationale, and demonstrate compliance, all while benefiting from faster threat detection and analysis at a scale that would otherwise require significantly more security staff and specialized expertise.
IRIS Shows How Domain Context Supercharges AI Threat Analysis
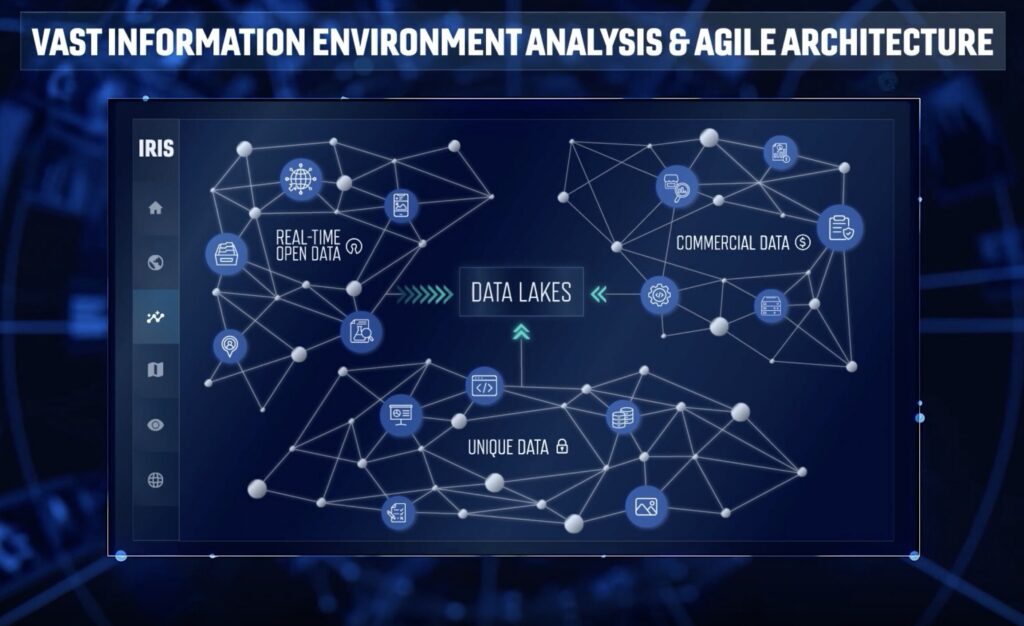
Peraton’s Interactive Realtime Information System (IRIS) highlights a parallel trend: real-time AI systems infused with rich domain context. IRIS unifies five AI models with mission data and analytical workflows to transform large, complex datasets into usable intelligence within seconds. Operators can run semantic searches, ask natural language questions, and perform sentiment trend analysis to detect influence operations and track adversary narratives in near real time. This domain-aware design mirrors advances in AI threat hunting for cyber defense—accuracy and relevance depend on fusing models with high-quality, mission-specific data rather than generic training alone. By mapping messaging strategies and supporting Psychological Operations and Information Operations planning, IRIS demonstrates how AI can act as a force multiplier in cognitive environments. The same pattern—contextual, workflow-integrated AI—underpins the next generation of security tools aimed at shrinking the gap between attack and response.
Toward Predictive, AI-Assisted Security Operations
Taken together, platforms like Prevyn AI and IRIS signal a shift from reactive security to predictive, AI-assisted operations. Instead of waiting for alerts to pile up, AI threat hunting systems analyze infrastructure staging, attacker tooling, and narrative signals to infer intent before an attack fully launches. This pre-vision approach lets defenders prioritize hardening, adjust detection rules, and prepare automated threat response paths in advance. Crucially, these gains do not require proportionally larger security teams; they come from smarter use of existing data, tighter integration with workflows, and governed automation that keeps analysts in charge. As threat actors continue to operate at machine speed, organizations that successfully combine real-time AI, domain-specific context, and responsible control models will be best positioned to achieve faster threat detection and maintain resilience against both technical intrusions and information-centric operations.

