A New Kind of Default: Privacy That Just Works
Android 17 reshapes privacy by changing what apps can see on your phone before you ever open Settings. Instead of relying on users to dig through menus, the system now ships with three key protections turned on by default: a Contacts Picker, a local network access block, and a delay on SMS one-time-password (OTP) access. Together, these Android 17 privacy settings narrow what apps can automatically reach—your address book, devices on your Wi‑Fi, and incoming verification codes—without breaking everyday tasks. Most apps targeting the new API level 37 never even show a permission prompt, because they interact through system pickers or controlled APIs instead of broad app permission controls. The result is a quieter, less nagging experience where sensitive data stays locked down by design, and only truly trusted or clearly justified apps can ask to go further.
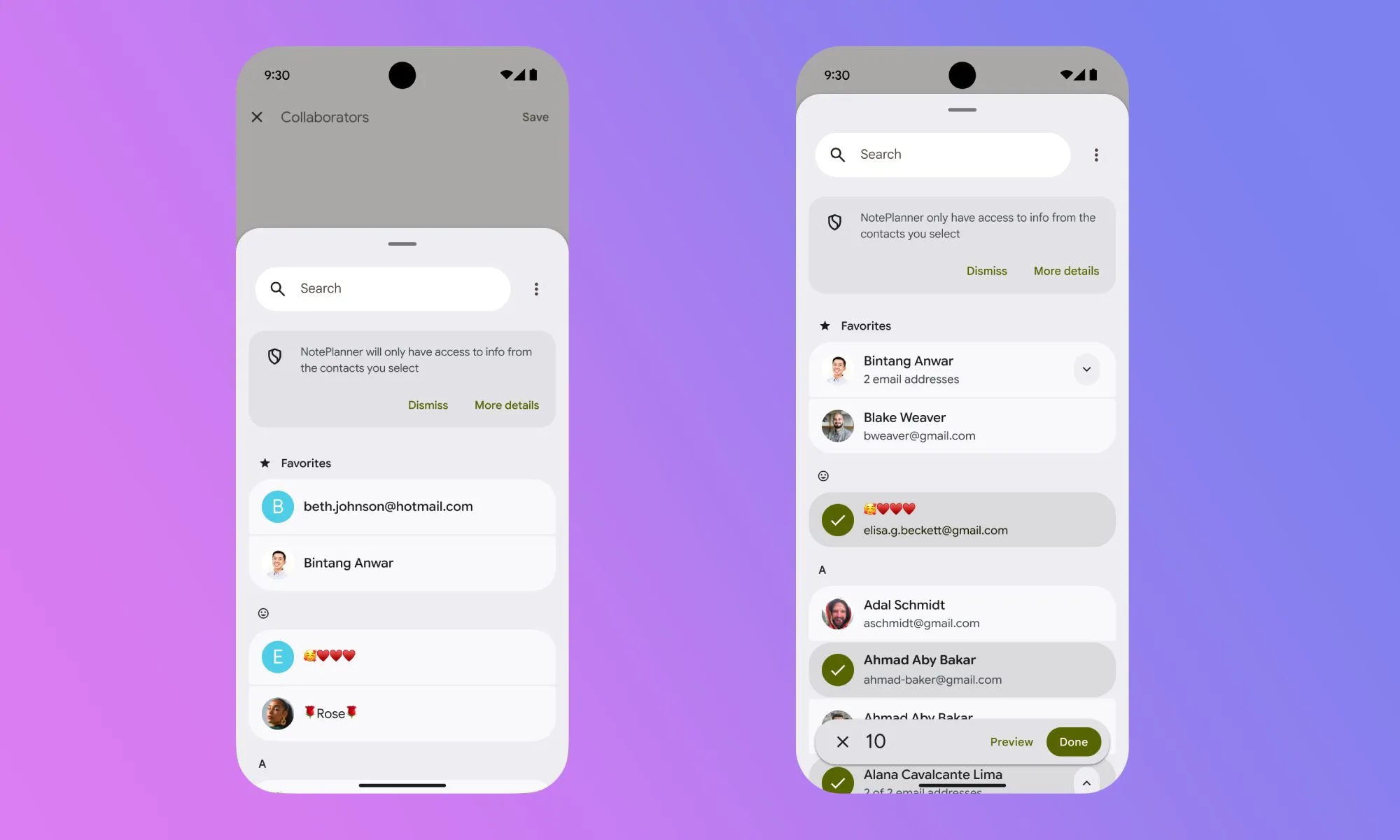
Contacts Picker: Contact Access Restrictions Without the Hassle
Historically, granting contact permission meant handing an app your entire address book—names, numbers, emails, and notes included. Android 17 fixes this with a system-level Contacts Picker that replaces blanket contact access with contact-by-contact sharing. When an app needs a contact, it calls the picker instead of requesting broad READ_CONTACTS permission. You choose specific entries, the app gets only what it asked for—such as just a phone number—and access is temporary and session-based. Once you leave that screen or finish the task, access ends automatically. This approach also respects work profiles and private spaces, letting you pick from either without exposing full lists from both. The big win is that contact access restrictions now happen by default. You still get the feature you wanted—like sharing a phone number or email—without silently giving a simple app long-term visibility into hundreds of contacts.
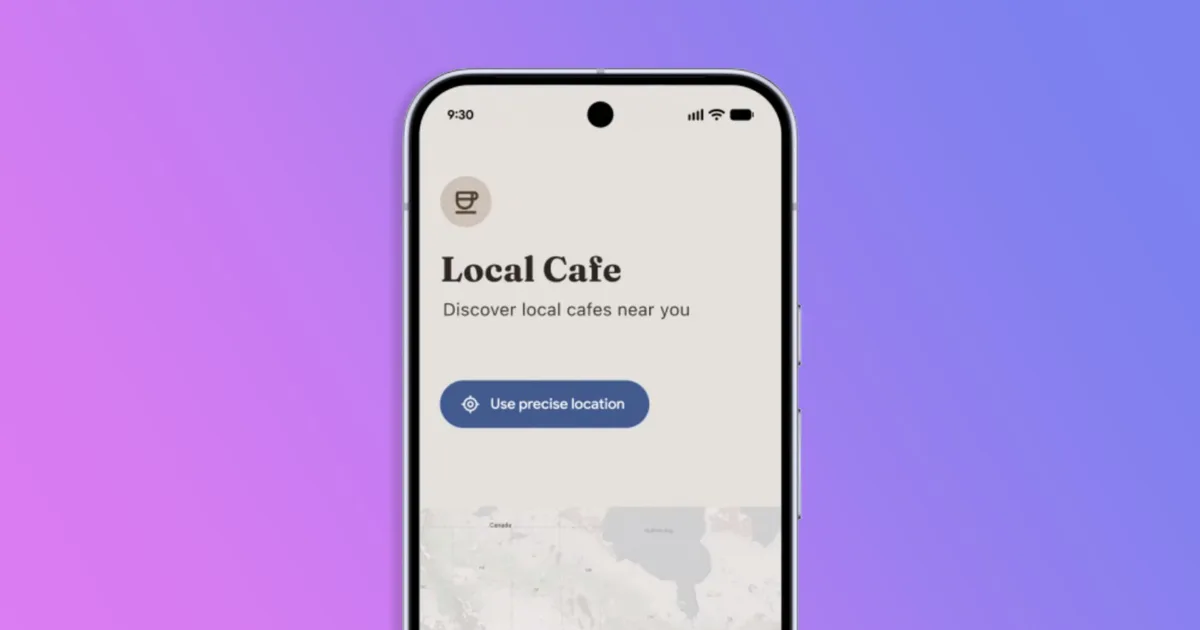
Local Network Block: Stopping Silent Scans of Your Home Devices
Before Android 17, almost any installed app could quietly scan your local Wi‑Fi network. A shopping app, a casual game, or a forgotten utility might map the devices connected to your router and nearby access points, contributing to a network fingerprint that tracks you across services without ever touching the wider internet. Android 17 introduces a new runtime permission, ACCESS_LOCAL_NETWORK, to shut down this behavior by default. Apps targeting API level 37 must now either use a system device picker for one-off connections or explicitly request local network access when they legitimately need persistent communication, such as for smart home control or local media streaming. Most people will never see this prompt, because compliant apps rely on the picker instead of broad access. The quiet scanners that had no real business probing your network simply stop working, giving you built‑in protection against subtle background tracking.
Delayed SMS OTP Access: SMS Security Protection Against Code Theft
SMS-based two-factor authentication remains common, but it has a weakness: any app with SMS read permission could intercept one-time passwords the instant they arrived. Android 17 addresses this by adding a three-hour delay before most third-party apps can programmatically read SMS messages containing OTP codes, for apps targeting API level 37. By the time an app can access those messages, the codes are long expired and useless to attackers. Crucially, this delay does not affect your default SMS app, assistant apps, or verified companion apps, nor does it interfere with services that use Google’s SMS Retriever or SMS User Consent APIs, which already involve clear user approval. For you, SMS still works as usual—codes arrive, you read them, and log in. The difference is that silent code-grabbing apps lose their edge, giving you stronger SMS security protection without requiring any manual settings or new habits.
What You Need to Do (And Why This Matters)
The most important part of these Android 17 privacy settings is that you do not have to configure anything. As your phone updates and apps target the new platform level, the Contacts Picker, local network permission, and SMS OTP delay start working automatically. You continue installing and using apps as usual, but now with tighter app permission controls quietly guarding sensitive data. If an app genuinely needs broader access—say for managing smart lights or acting as your default messaging client—it will either guide you through a transparent permission prompt or rely on the system’s safer pickers and APIs. Taken together, these defaults push the ecosystem toward minimal data access by design. Instead of expecting users to be security experts, Android 17 bakes privacy into the OS itself, so your contacts, home network, and verification codes are better protected every day, whether or not you ever open the Settings app.