Why Human-Only Threat Hunting Can’t Keep Up Anymore
Modern cyberattacks unfold across cloud services, endpoints and SaaS applications in minutes, while traditional investigations still depend on humans pivoting manually through logs, threat feeds and case management tools. This gap between attack speed and analyst capacity is widening as organisations adopt more connected systems and attackers automate their own operations. Human-led processes struggle to correlate signals from disparate platforms fast enough to spot multi-stage intrusions, leaving dwell time uncomfortably high and response delayed. As a result, security leaders are turning to AI threat hunting and threat detection automation to offload repetitive enrichment, triage and correlation tasks. The goal is not to replace analysts but to free them from data wrangling so they can focus on higher-value decisions, governance and incident leadership. AI-assisted investigations are becoming a core pillar of cyber defense AI strategies, particularly in environments where automated threat response must still align with strict oversight and compliance requirements.
Prevyn AI: Agentic Threat Hunting With Humans on the Loop
Group-IB’s Prevyn AI illustrates how AI can compress investigation time without sidelining human judgment. Embedded as the cognitive core of its Unified Risk Platform, Prevyn AI is available at no additional cost to existing Threat Intelligence and Managed XDR customers, lowering adoption friction. In threat intelligence, it orchestrates 11 specialised agents for malware analysis, threat actor tracking and dark web monitoring, all modelled on investigative logic from high-tech crime cases. Instead of relying mainly on open-source feeds, the system reasons over Group-IB’s intelligence data lake, built from cybercrime investigations and work with law enforcement, to infer attacker intent and infrastructure staging before campaigns launch. Internal testing showed more than a 20% uplift in research quality, combining accuracy and analytical depth. Within Managed XDR, Prevyn AI helps SOC teams by analysing alerts, drafting incident reports and generating structured remediation workflows, while requiring explicit human approval for every recommendation to satisfy frameworks such as the EU AI Act and DORA.
Cyber Resilience Fabric: AI Analytics Tied to Business Impact
Tech Mahindra and Cisco’s Cyber Resilience Fabric addresses another bottleneck: alert overload disconnected from business context. By combining Cisco’s Splunk Enterprise Security with Tech Mahindra’s Risk Scoring Platform, the product provides unified visibility into security events, operational signals and contextual risk data. AI-assisted analytics drive a system of contextual risk prioritisation that ranks incidents by likely business impact rather than raw alert volume, allowing teams to focus on what truly threatens critical services. This approach cuts operational noise and improves triage accuracy, while helping CISOs and CIOs demonstrate alignment with governance and regulatory demands. For enterprises, the platform aims to bring earlier threat detection, faster coordinated response and more structured recovery into a single environment. It also exemplifies how cyber defense AI is being embedded into existing SIEM and risk tooling, sidestepping rip-and-replace deployments and accelerating the real-world effectiveness of automated threat response strategies.

Peraton IRIS: Multi-Model AI for Real-Time Information Warfare
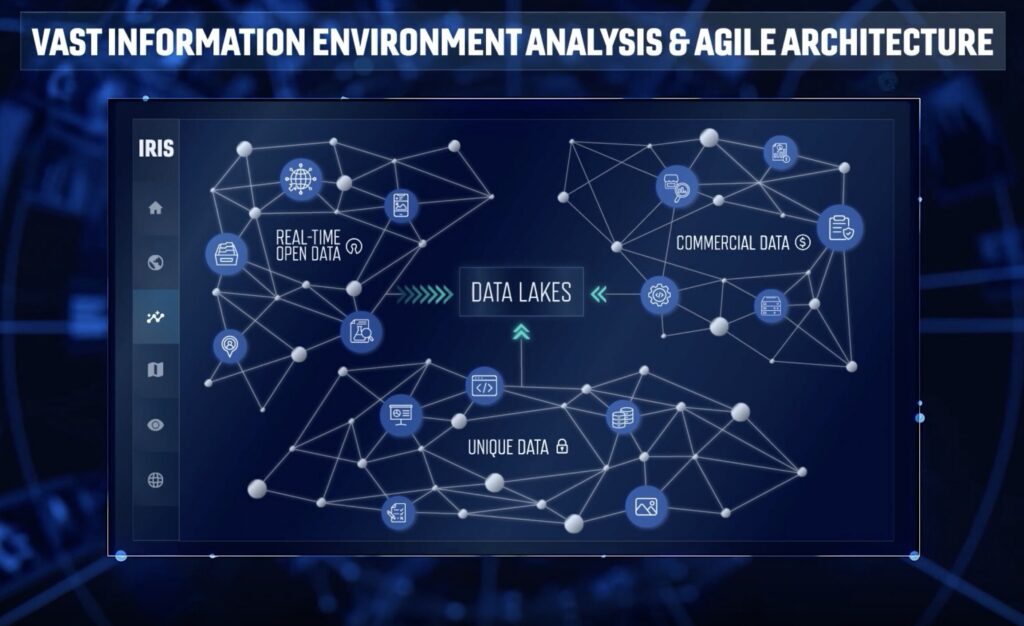
Peraton’s Interactive Realtime Information System (IRIS) extends AI threat hunting concepts into the information and cognitive domains. IRIS integrates five AI models with mission data, domain context and analytic workflows to transform large, disparate datasets into actionable intelligence. Operators can run advanced semantic searches, pose natural language questions, track sentiment trends and follow evolving narratives, enabling near real-time detection of influence operations and adversary messaging campaigns. These capabilities support Psychological Operations and Information Operations planning, including target audience analysis and data-driven counter-narrative development. Crucially, IRIS is designed for interoperability, integrating with existing systems and data sources instead of locking customers into a proprietary stack. According to Peraton, this shift from manual data aggregation to instant, citation-backed insight generation turns AI into a force multiplier, allowing human analysts to react to fast-moving cognitive threats with the same speed advantage that automated threat response brings to traditional cyber defence missions.
From Experimental AI to Embedded Security Capability
Across these deployments, a common pattern is emerging: AI is no longer a bolt-on experiment but an embedded layer within existing security infrastructure. Group-IB’s Prevyn AI operates as the cognitive core of a unified risk platform, Tech Mahindra and Cisco’s Cyber Resilience Fabric fuses AI analytics directly into SIEM and risk scoring, and Peraton’s IRIS is designed from the ground up to interoperate with current mission systems. This integration-first approach reduces deployment friction—no wholesale platform replacement is required—while accelerating time to value for AI threat hunting and threat detection automation. Governance remains central, with vendors emphasising human approval and compliance alignment to build trust. As enterprises face escalating attack speed, expanding attack surfaces and rising regulatory pressure, AI-assisted operations are becoming a practical necessity. The organisations that succeed will be those that pair cyber defense AI with clear processes, accountability and a sharp focus on business impact.

