Why iOS 26.5 Is a Must-Install Security Update
Apple’s latest iOS 26.5 security update delivers over 60 iPhone security patches, targeting some of the most sensitive parts of the operating system. Among the fixes are at least six critical kernel vulnerabilities, one of which (CVE-2026-28951) could allow a malicious app to gain full root privileges. Apple also addressed around a dozen WebKit issues, including CVE-2026-28962, where simply interacting with malicious web content might expose sensitive user data. Another flaw, CVE-2026-28995, affects App Intents and could let an app break out of its sandbox—one of iOS’s core defenses. Together, these issues form the kind of exploit chains attackers rely on to silently compromise devices. Although Apple has not reported any of these bugs as actively exploited, the scope and depth of the iOS 26.5 security update make delaying installation a serious risk.

Kernel, WebKit, and Wi‑Fi: High-Value Targets for Attackers
The newly released iPhone security patches focus heavily on components attackers most often chain together: the kernel, WebKit, Wi‑Fi, and sandbox protections. Kernel fixes span privilege escalation, kernel memory disclosure, race conditions, and out‑of‑bounds writes that could lead to arbitrary code execution at the highest privilege level. On the WebKit side, Apple has closed vulnerabilities that could bypass Content Security Policy, leak sensitive information, crash Safari, or corrupt memory via crafted web content. Wi‑Fi and networking bugs also received serious attention, including an issue where a crafted Wi‑Fi packet could enable code execution with kernel privileges, and denial‑of‑service flaws in Wi‑Fi and mDNSResponder traffic handling. These weaknesses are especially dangerous because they often require minimal user interaction—sometimes just visiting a website or being on the same wireless network. Installing iOS 26.5 ensures these high‑impact paths into your device are sealed.
Who Needs to Update—and Which Devices Are Covered
iOS 26.5 is available for iPhone 11 and later models, while compatible iPad devices from the 8th‑generation iPad and iPad mini 5th generation onward receive a matching security level. For users on slightly older hardware, Apple has released iOS 18.7.9 and iPadOS 18.7.9, targeting iPhone XS, iPhone XS Max, iPhone XR, and the 7th‑generation iPad. Even legacy devices are not left behind: iPadOS 17.7.11, iOS 16.7.16, and iOS 15.8.8 extend protection to models such as iPhone X, iPhone 6s, iPhone 7, the first‑generation iPhone SE, iPad Air 2, and iPad mini 4. These older-branch updates address many of the same underlying issues, including notification handling and core security components. If your device can install any of these updates, it should—Apple’s ongoing support for older hardware means you can still benefit from critical kernel vulnerability fixes and WebKit security improvements.

AI, Threat Hunters, and Why Speed Matters
The discovery and reporting of these vulnerabilities underscore how closely modern threat hunters watch iOS. One kernel issue, CVE-2026-28943, was reported by Google’s Threat Analysis Group, which routinely tracks sophisticated, state-backed attackers and high-risk targets. Another WebKit security fix, CVE-2026-28942, was credited to Anthropic researchers working with the Claude AI system. Apple’s advisories also acknowledge contributions from Google Project Zero, TrendAI Zero Day Initiative, and other security firms, highlighting a growing role for AI on both defense and offense. While Apple states that none of the patched flaws are currently known to be exploited, the same classes of bugs—kernel privilege escalations, WebKit memory corruption, sandbox escapes—are often used in real-world attack chains. The window between disclosure and exploitation can be short, so installing iOS 26.5 and related updates as soon as possible is essential to stay ahead of emerging threats.
How to Update Safely and Reduce Ongoing Risk
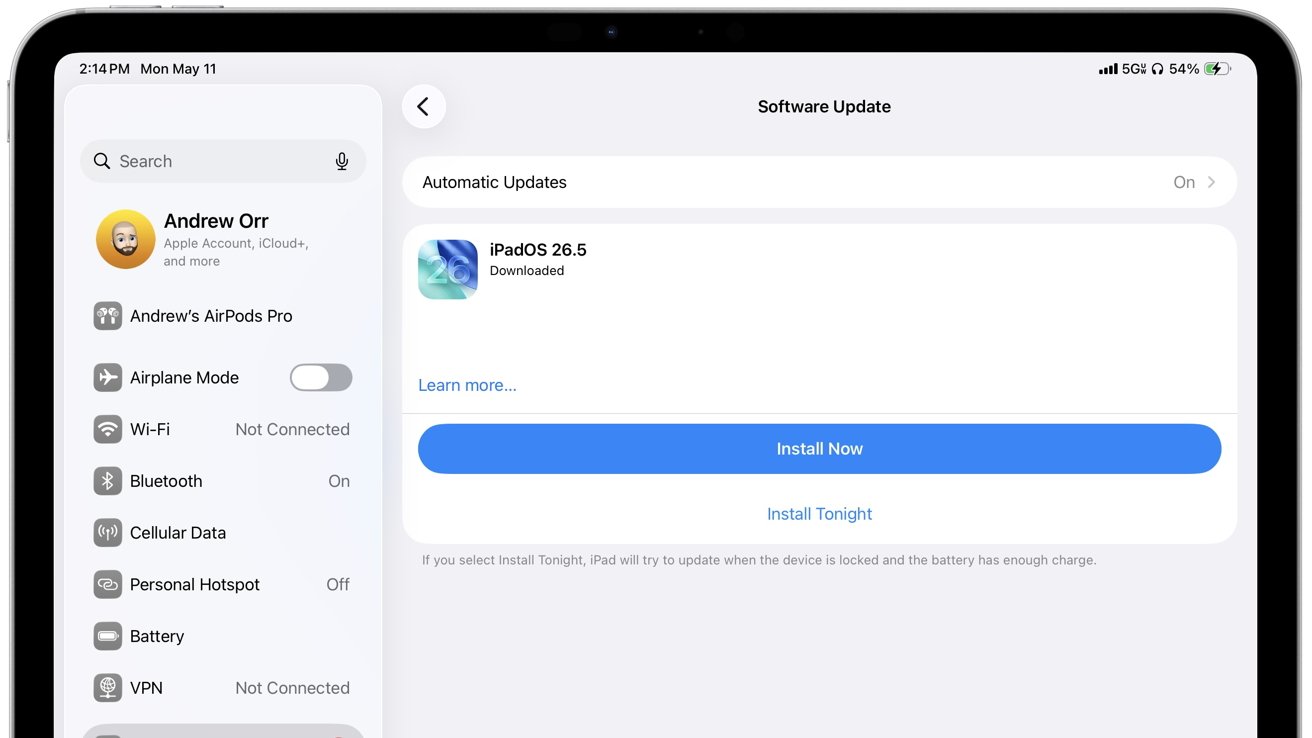
To apply the iOS 26.5 security update, open Settings, go to General, then Software Update, and install the latest version offered for your device. Make sure to restart afterward so kernel and Wi‑Fi patches fully take effect. For iPhones and iPads on older branches, such as iOS 18.7.9, 17.7.11, 16.7.16, or 15.8.8, the process is the same—accept any available update and complete the reboot. Beyond patching, you can further reduce risk by avoiding untrusted apps, refusing unknown configuration profiles, and steering clear of suspicious links and unsafe Wi‑Fi networks. Because many of the patched flaws involve malicious web content and crafted files, keep Safari and any system browsers fully updated. If your hardware no longer receives security updates, avoid using it for sensitive tasks like banking or password management, as older systems will remain exposed to future kernel and WebKit vulnerabilities.