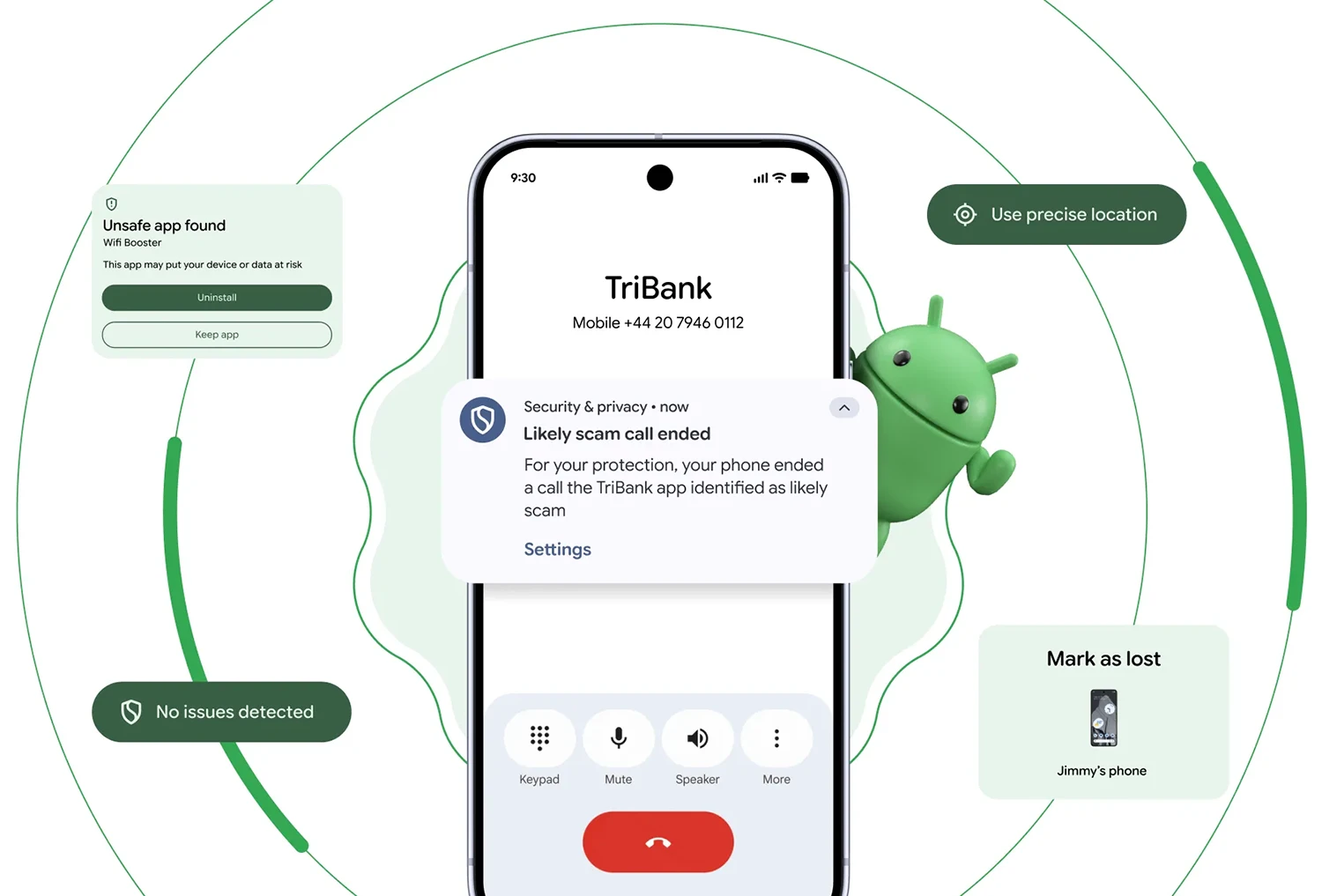
Verified Bank Calls: Cutting Off Caller ID Spoofing at the Source
Caller ID spoofing has become a lucrative attack vector, contributing to an estimated USD 980 million (approx. RM4.6 billion) in annual losses when scammers impersonate banks. Android’s new verified bank calls feature is designed to break that pattern. When a call arrives claiming to be from a financial institution, Android checks it against the bank’s official app installed on the device. If the app confirms no active call is in progress, Android automatically terminates the connection before the user even hears a scammer. Financial institutions can also mark specific numbers as inbound-only, so any outgoing call pretending to use those lines is blocked instantly. Initially rolling out on Android 11 and newer with partners like Revolut, Itaú, and Nubank, this capability pushes Android security features directly into the phone dialer, aiming to make scam prevention on Android a frontline experience rather than an optional add-on.
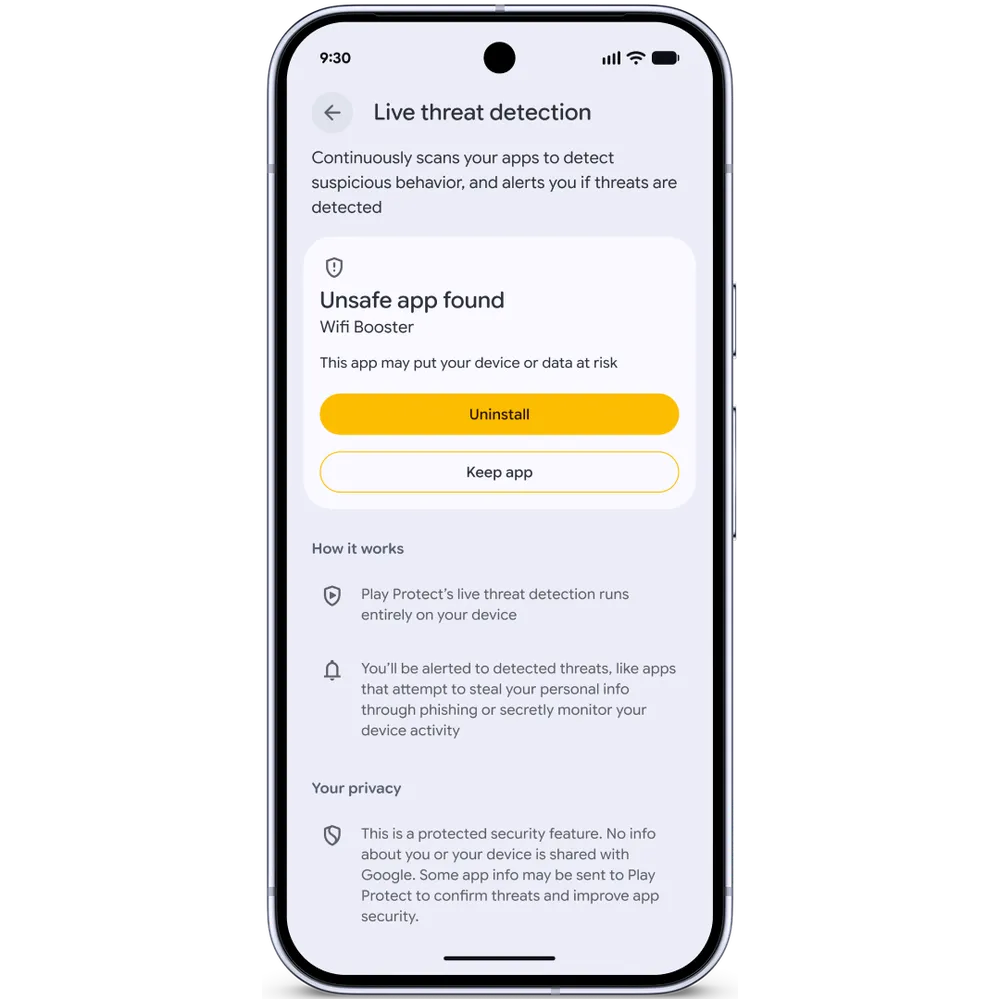
AI App Monitoring: Live Threat Detection and Dynamic Signal Monitoring
Android’s Live Threat Detection represents a shift toward continuous, AI-driven monitoring of apps rather than static checks at install time. Running entirely on-device, it observes how apps interact with system services to spot patterns commonly associated with fraud and malware. The latest upgrades focus on behaviors that scammers increasingly exploit: covert SMS forwarding, abuse of accessibility overlays, and apps hiding their icons before launching malicious actions in the background. A new capability called dynamic signal monitoring allows Android 17 devices to analyze application-system interactions in real time and receive updated detection rules as new threats appear, without waiting for full OS updates. Because processing remains local to the device, AI app monitoring aims to catch suspicious behavior without sending personal data to the cloud. Combined with Chrome’s enhanced APK download scanning via Safe Browsing, Android security features now guard both the moment you install an app and the way it behaves over its lifetime.
Advanced Protection, Intrusion Logging, and Spyware Forensics
Android’s Advanced Protection mode is evolving into a hardened environment for high-risk users and anyone who wants stricter defaults. On Android 17, it automatically removes accessibility service access from apps that are not explicitly declared as accessibility tools, closing a common avenue for screen-reading abuse. It also disables device-to-device unlocking and Chrome WebGPU support, and layers in scam detection for chat notifications. The standout addition is Intrusion Logging, an encrypted forensic trail designed to help uncover spyware and sophisticated compromises. Once enabled, it records security-relevant events such as suspicious app installs, unusual server connections, or attempts to tamper with system logs. These logs can later be analyzed by security teams or researchers to reconstruct attacks without exposing user content. Initially rolling out on devices running the Android 16 December update and newer, this capability signals a move toward built-in spyware investigation tools rather than relying solely on external forensic solutions.
Device Theft Protection: From Lock Screens to Network Access
Android 17 brings a multi-layered device theft protection strategy that assumes thieves may have seen or guessed a PIN. The Find Hub’s Mark as lost feature now requires biometric authentication to unlock a flagged device, making stolen credentials far less useful. Once a phone is marked lost, Android hides Quick Settings and blocks new Wi-Fi and Bluetooth pairings, preventing attackers from cutting connectivity or pairing accessories to help exfiltrate data. Default-on theft protections, previously piloted in one market, are expanding to more regions and to new Android 17 devices as well as recently reset phones. These protections include Remote Lock and Theft Detection Lock, which can automatically secure a device based on suspicious movement or behavior. Android 17 also reduces the number of allowed PIN guesses and increases delays between attempts, slowing brute-force unlocks. For ownership verification, the IMEI is accessible from the lock screen on Android 12 and later, helping carriers and law enforcement validate legitimate users.
A Proactive, Multi-Layered Android Security Model
Together, verified bank calls, AI app monitoring, and device theft protections form a cohesive security model aimed squarely at real-world threats: financial scams, identity theft, and malware. Instead of relying primarily on post-incident cleanup, Android’s roadmap emphasizes proactive defenses that intervene before damage is done. Verified financial calls stop spoofed conversations before they start; Live Threat Detection and dynamic signal monitoring watch for evolving fraud schemes through on-device AI; and Advanced Protection with Intrusion Logging gives at-risk users both stronger defaults and forensic visibility into sophisticated attacks. On the privacy front, Android 17’s temporary precise location sharing and redesigned contact picker let users grant narrowly scoped access, reducing data exposure to compromised apps. This layered approach positions scam prevention on Android not as a single feature but as an integrated stack, aligning OS-level safeguards, app behavior analysis, and user controls to make everyday mobile banking and communication safer by default.