From Tap to Transaction: How Contactless Payments Talk
When you tap your phone at a checkout terminal, two core technologies quietly spring into action: NFC and EMV. Near-field communication (NFC) is the short-range wireless link that connects your phone to the payment reader when they are just a few centimeters apart. It acts like a secure cable replacement, transmitting payment data only over this tiny distance and only for a brief moment. On top of NFC sits EMV, the global standard defining how chip-based cards and digital wallets authenticate and authorize transactions. In practical terms, NFC is the transport layer, while EMV governs the rules for validating cards, running cryptographic checks, and routing requests through banks and payment networks. This layered approach ensures that even though the physical action is just a quick tap, a structured, standards-based security protocol is orchestrating each step of the transaction flow in the background.
Payment Tokenization Explained: Why Your Real Card Number Stays Hidden
One of the biggest pillars of contactless payment security is tokenization. Instead of storing or sending your actual card number, digital wallets like Apple Pay create a special substitute called a token. When you add a card, Apple Pay works with your bank and a Token Service Provider to generate a Device Account Number (DAN) unique to that device. The DAN, along with cryptographic keys and a CVV key, is stored inside a tamper-resistant chip known as the Secure Element. During a purchase, the DAN is used to create a one-time cryptogram and a dynamic CVV linked to that specific transaction. Merchants receive only this tokenized data, never your real card number. Even if their systems are compromised, attackers gain only limited-use tokens, not the underlying account. This is why contactless payment security can actually be stronger than swiping or typing in card details online.
Biometric Checks and Mobile Payment Encryption
Before any payment data leaves your device, biometric authentication usually stands in the way. Features such as Face ID, Touch ID, or a device PIN unlock the Secure Element that holds your payment token and keys. This means a thief cannot simply wave your phone at a terminal without first bypassing that second layer of protection. Once unlocked, the Secure Element generates encrypted payment credentials, including the cryptogram and dynamic CVV, using keys provisioned during card setup. These values are tightly bound to the token and the transaction details, making them useless if intercepted or reused. Over NFC, the communication between the phone and terminal follows EMV-defined encryption and verification rules. In short, biometrics protect access to the wallet, while strong cryptography and mobile payment encryption protect the data itself as it moves from your device to the merchant’s system.
Real-Time Authorization: How Banks Decide in Seconds
After your phone sends encrypted, tokenized data to the payment terminal, the merchant’s payment service provider takes over. It decrypts the payload and constructs a 3D Secure–style authorization request, then forwards it through the card network, such as Visa or Mastercard. Because a token like Apple Pay’s Device Account Number is used, the network consults the Token Service Provider to map that token back to the underlying card. The TSP validates the request using its private keys and supplies the real card data only to the payment network, which then passes it to your bank. Your bank verifies the dynamic CVV and checks whether the transaction fits your account status before approving or declining. The response flows back through the same chain to the point of sale and, in many cases, back to your phone over NFC. All of this typically finishes in just a few seconds.
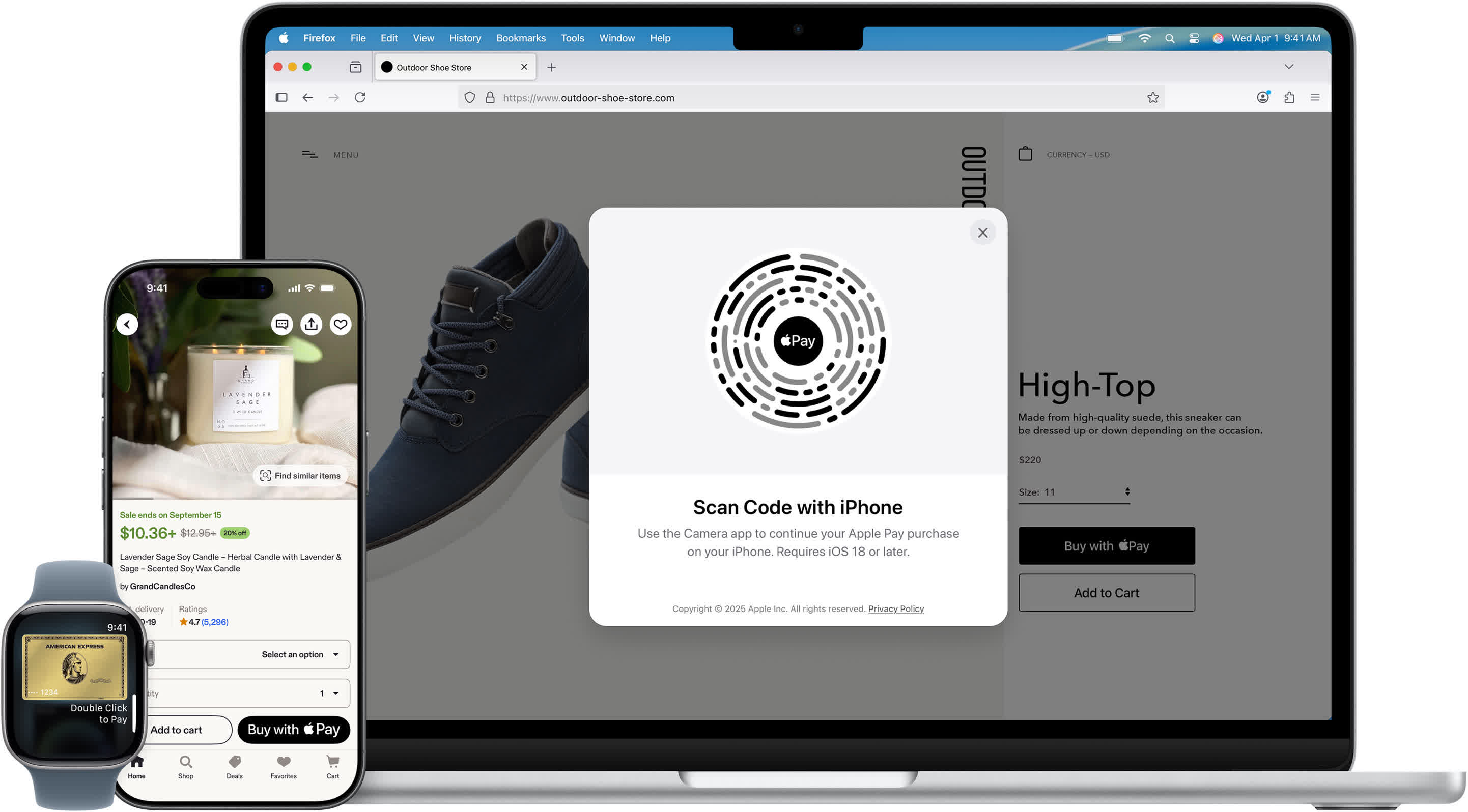
How Apple Pay Works vs. Other Mobile Wallets
Although different digital wallets share the same EMV and NFC foundations, their implementations vary. To understand how Apple Pay works, it helps to note that the system does not store your actual card number on Apple’s servers. Instead, the Device Account Number and its keys live inside the device’s Secure Element, and only tokenized data is shared with merchants. Google Pay follows the same EMV tokenization principles but uses a slightly different architecture: when you register a card, Google stores the card information on its servers and then sends a token to your phone for use at terminals. In both cases, tokenization, cryptograms, and real-time authorization protect the underlying card. For everyday users, the result is the same: tapping your phone leverages multiple layers of cryptography and contactless payment security, often making it safer than using a physical card.