Inside the Canvas Data Breach and Ransom Deal
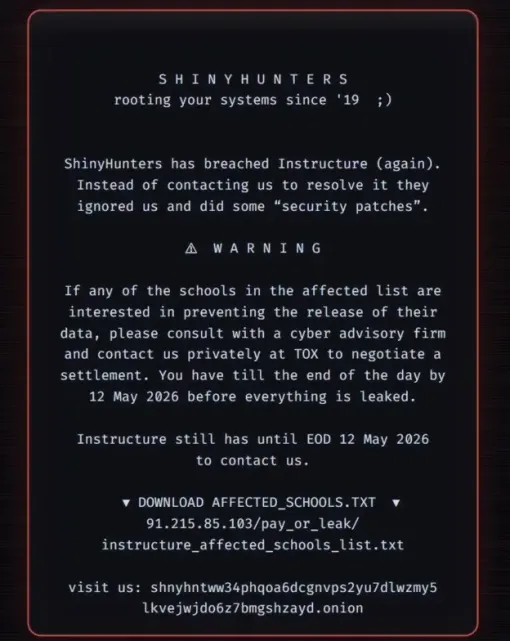
Instructure, the company behind the Canvas education platform, has confirmed it reached a settlement with the cyber extortion group ShinyHunters after a major data breach. The attackers claimed to have stolen 3.5 terabytes of student and university data, including an estimated 280 million records, and to have accessed multiple Canvas databases. Universities were reportedly given a deadline to negotiate before the hackers threatened to leak “several billions of private messages among students and teachers.” Instructure says the agreement secured the return of stolen data, deletion of copies, and a promise not to extort affected institutions or students. The company also obtained what it described as “digital confirmation of data destruction,” though it did not disclose what was provided in exchange. This response places the Canvas data breach squarely within a wider pattern of ransom payment cyber attacks targeting large technology platforms.
Service Disruptions Hit Universities at the Worst Possible Time
The breach had immediate, visible consequences for universities relying on Canvas during critical academic periods. Operations at roughly 9,000 institutions were disrupted, with outages affecting campuses across several regions and causing significant interruption to teaching and assessment. In some cases, students reported ransom notes appearing directly within their online exam environments. At Mississippi State University, assessments were postponed after such messages surfaced mid-exam, forcing administrators to improvise contingency plans. Institutions in multiple countries, including well-known universities, experienced downtime as they rushed to restore access, verify data integrity, and communicate with students and staff. Some Irish universities, for example, publicly acknowledged disruption but stressed that services had returned to full operation after Instructure temporarily disabled its “free-for-teacher” feature, which was identified as the entry point exploited by the attackers. The episode underlines how deeply embedded education platforms have become in routine academic operations.

Why Paying Ransoms Risks Future Attacks on Education Platforms
Instructure’s decision to pay a ransom runs counter to guidance from agencies such as the FBI and the UK’s National Crime Agency, which warn that ransom payments encourage further attacks. Law enforcement experience shows there is no technical guarantee that data is truly deleted, even when attackers claim to have destroyed it. Investigations into other groups, such as LockBit, have revealed that cybercriminals sometimes retain stolen data for future leverage despite accepting payment. Security experts note that groups like ShinyHunters increasingly focus on high-impact targets, timing attacks for maximum disruption and negotiating leverage—such as during exam season. Once an organisation is seen to pay, it may be marked as a valuable future target, and other education platforms may face copycat incidents. This Canvas data breach illustrates how ransom payment cyber attacks can erode trust in education platform security and normalise “consent or pay” dynamics in digital risk management.

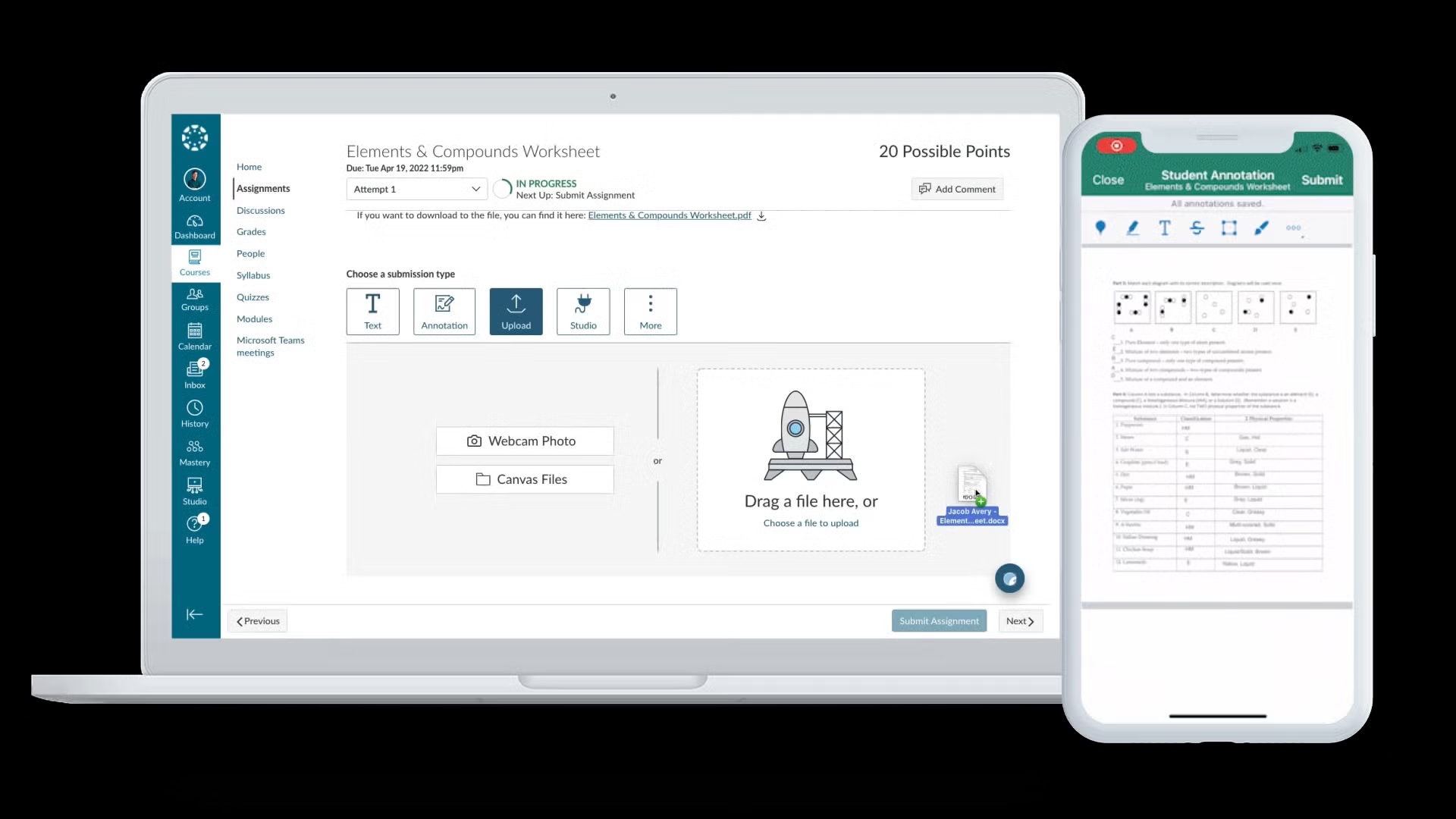
What the Breach Reveals About EdTech Vulnerabilities
Details emerging from the incident highlight systemic weaknesses in education technology infrastructure. Instructure has said the attackers exploited an issue related to its “free-for-teacher” accounts, a feature designed to lower barriers to entry for educators. This underscores how convenience-focused features can unintentionally widen the attack surface. ShinyHunters, an English-speaking group active since around 2020, has previously been linked to high-profile breaches at major enterprises and even public-sector platforms. Their pivot to an education platform shows that student data protection is now a prime target for financially motivated cybercrime. Analysts point out that attackers are shifting tactics: instead of only encrypting systems, they threaten large-scale data leaks, reputational damage, and operational chaos. For universities deeply reliant on cloud-based learning management systems, this raises uncomfortable questions about vendor oversight, shared responsibility for security, and the resilience of digital classrooms under sustained attack.

Steps Students and Institutions Should Take Now
In the wake of the Canvas data breach, both students and institutions should assume that core identifiers—such as names, email addresses, student IDs and messages—may have been exposed. Individuals should monitor email accounts for targeted phishing attempts referencing their courses, instructors or grades, and treat unexpected login prompts or file-sharing links with caution. Where possible, students and staff should enable multi-factor authentication on university and personal accounts and avoid reusing passwords across platforms. Institutions, meanwhile, need to audit their Canvas integrations, review permissions for third-party tools and ensure that incident-response plans cover cloud-based learning systems. Universities should also clearly communicate what data was affected, how it is being secured and what support is available to those concerned about student data protection. Finally, procurement and governance processes should place greater emphasis on education platform security, including vendor transparency and regular independent security assessments.