Inside the ADT Data Breach and the ShinyHunters Leak
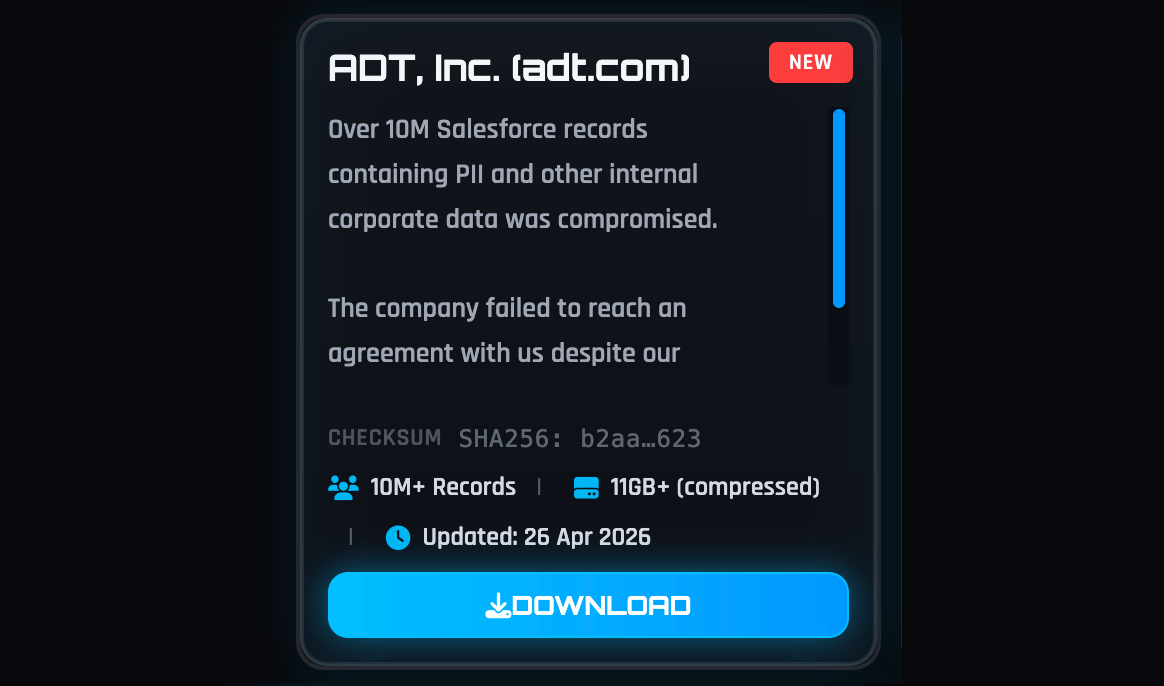
Home security giant ADT has confirmed a data breach after the ShinyHunters extortion group broke into its systems and stole personal information tied to millions of people. ADT, the oldest and largest home security company in the United States, provides monitored security and smart home solutions to over 6 million customers. In this incident, the attackers accessed data including names, phone numbers and physical addresses. In a smaller number of cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were also exposed. According to the breach-tracking service Have I Been Pwned, the leaked database contains the information of around 5.5 million individuals, along with unique email addresses and partial government IDs. ShinyHunters later published an 11GB archive of the stolen data on its dark web leak site after attempts to extort ADT reportedly failed, turning this into a large-scale privacy incident.
Why a Home Security Provider’s Data Is Extra Sensitive
For any smart home security user, the ADT data breach is a stark reminder that your provider holds more than just a login ID. A security company typically stores names, mobile numbers, and full home or business addresses to dispatch support and emergency response. It may also keep device information, installation details and account metadata that reveal when and how a system is used. Even when payment data and security systems themselves are not compromised, attackers who obtain accurate addresses and contact details can craft highly convincing scams, stalk victims, or map which premises are protected. When such data is leaked at the scale of 5.5 million people, the risk is not only financial fraud but also physical safety and home security privacy. For Malaysian users installing smart CCTVs, alarm systems or video doorbells, this shows that the company behind the app can become a critical point of failure.

Cloud-Connected Smart Homes: Convenience with Hidden Cyber Risks
The ADT incident illustrates a broader issue: modern smart home security depends heavily on cloud platforms managed by vendors. Globally, smart home devices are expanding rapidly, driven by connected security systems, smart speakers and other IoT products that aim to make life safer and more convenient. This growth reflects a structural shift towards homes that rely on integrated, always-online ecosystems for monitoring and automation. However, every cloud account, remote access feature and data dashboard is also an attack surface. Users must trust that providers are securing their infrastructure, patching vulnerabilities and handling sensitive data responsibly. If a company’s internal systems are breached, as seen with ADT and the ShinyHunters leak, even well-installed hardware on your wall cannot shield your personal data. The more devices you connect, the more your privacy and safety depend on someone else’s cybersecurity standards and response processes.
Practical Steps Malaysians Can Take to Protect Smart Devices
Malaysian smart home users do not need to panic, but they should act with urgency and discipline. Start by changing passwords for your security apps and related email accounts, using unique, strong passphrases managed by a reputable password manager. Turn on two-factor authentication (2FA) wherever available so attackers need more than just a stolen password. Regularly check breach-notification services like Have I Been Pwned to see if your email or phone number appears in known leaks and update credentials immediately if it does. Be extra cautious with calls or messages claiming to be from your security provider, especially if they reference your address or system details; verify independently through official channels before sharing information. Finally, keep your router, cameras and apps updated, and disable features you do not use, to reduce the number of potential entry points into your home network and devices.

Choosing Safer Smart Security Providers in Malaysia
With Malaysia pushing digital transformation and its leaders calling for stronger national cyber resilience, local consumers must also raise their expectations of smart home vendors. When evaluating a security provider, look for clear, accessible privacy and data protection policies that explain what is collected, where it is stored and how long it is retained. Check whether communications and stored data are encrypted, and whether the company operates or uses reputable regional data centres. A good provider should describe how it detects intrusions, how quickly it will notify users of a breach and what remediation steps it offers. Prefer products that support 2FA, regular firmware updates and transparent security practices. As adoption of smart security and other connected devices accelerates, these criteria matter as much as camera resolution or price. Ultimately, your choice of vendor can either strengthen or weaken the digital front door to your home.
