Android’s Auto Hang-Up: A New Line of Defense for Bank Calls
Google is rolling out a new Android banking security feature designed to cut off scammers before they speak. When a call appears to come from your bank, Android now checks directly with the bank’s official app on your device. If the app confirms that no legitimate employee is calling, the system automatically disconnects the call, shutting down one of the most common social-engineering tricks: call spoofing. Banks can also designate specific numbers as inbound-only, so any outgoing call that falsely uses those numbers is blocked on sight. This call spoofing defense initially works with select banking apps and requires Android 11 or higher, but Google plans to expand support over time. By validating calls against trusted banking apps, Android aims to reduce the risk of users being pressured into transferring funds or disclosing sensitive credentials over the phone.
TrickMo Trojan Variant: From Banking Malware to Network Pivot
While Android strengthens call protections, mobile banking malware is becoming more sophisticated. Researchers have identified a new TrickMo trojan variant that transforms infected devices into powerful network tools rather than just traditional credential stealers. TrickMo, long known for abusing accessibility services to hijack one-time passwords and take over devices, now relies on a runtime-loaded module (dex.module) that adds advanced network capabilities. This TrickMo trojan variant can perform reconnaissance commands such as curl, dnslookup, ping, telnet, and traceroute, effectively giving attackers a remote shell from the victim’s network position. It also supports SSH tunnelling and SOCKS5 proxying, enabling compromised phones to act as programmable network pivots and traffic-exit nodes. As a result, attackers can route malicious traffic through a victim’s device, undermining IP-based fraud detection systems on banking, e-commerce, and cryptocurrency services and blurring the line between classic mobile banking malware and full-fledged network intrusion tools.
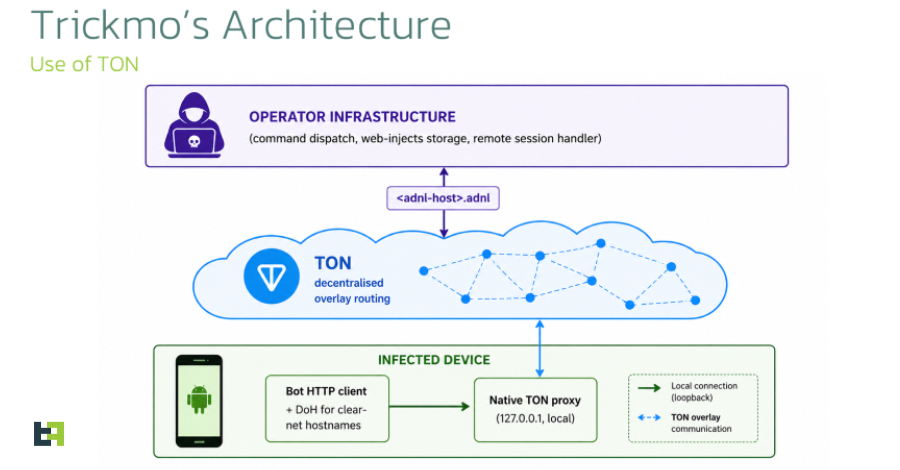
Stealth C2 with TON and Deceptive Distribution Tactics
The latest TrickMo builds stealth directly into its command-and-control (C2) channel by using The Open Network (TON) blockchain. The malware embeds a native TON proxy that runs locally on the device. All outbound C2 traffic is funneled through this proxy to .adnl hostnames resolved inside the TON overlay network. By avoiding conventional DNS and public internet infrastructure, TrickMo makes takedowns and network-based blocking significantly more difficult. Distribution tactics are equally deceptive. Threat actors deploy dropper apps that pose as adult-themed TikTok variants promoted via social platforms. Once installed, these droppers fetch and load the malicious dex.module at runtime, which then impersonates Google Play Services using innocuous-looking package names. Although the current build includes dormant components, such as Pine hooking framework references and broad NFC permissions, these are not yet active, suggesting that the developers are preparing for future expansions in functionality and stealth.
Layered Protection: OS-Level Defenses and User Vigilance
Android’s call spoofing defense is part of a broader strategy to strengthen mobile banking security at the operating system level. Alongside auto-ending spoofed bank calls, Google is enhancing one-time password protection by temporarily hiding OTPs from most apps, expanding Live Threat Detection to flag suspicious behaviors like SMS forwarding, and tightening Advanced Protection to restrict misuse of accessibility services. New controls for lost devices and fine-grained location sharing further reduce the attack surface. Yet OS safeguards alone cannot fully counter advanced threats like the new TrickMo variant, which blends social engineering, app spoofing, and stealthy C2. Users still need to install banking apps only from official stores, treat unsolicited calls and links with suspicion, and pay attention to system warnings about suspicious apps or behaviors. The most effective defense is a combined approach: platform-level protections that disrupt spoofed calls and malware behavior, reinforced by informed, cautious user habits.