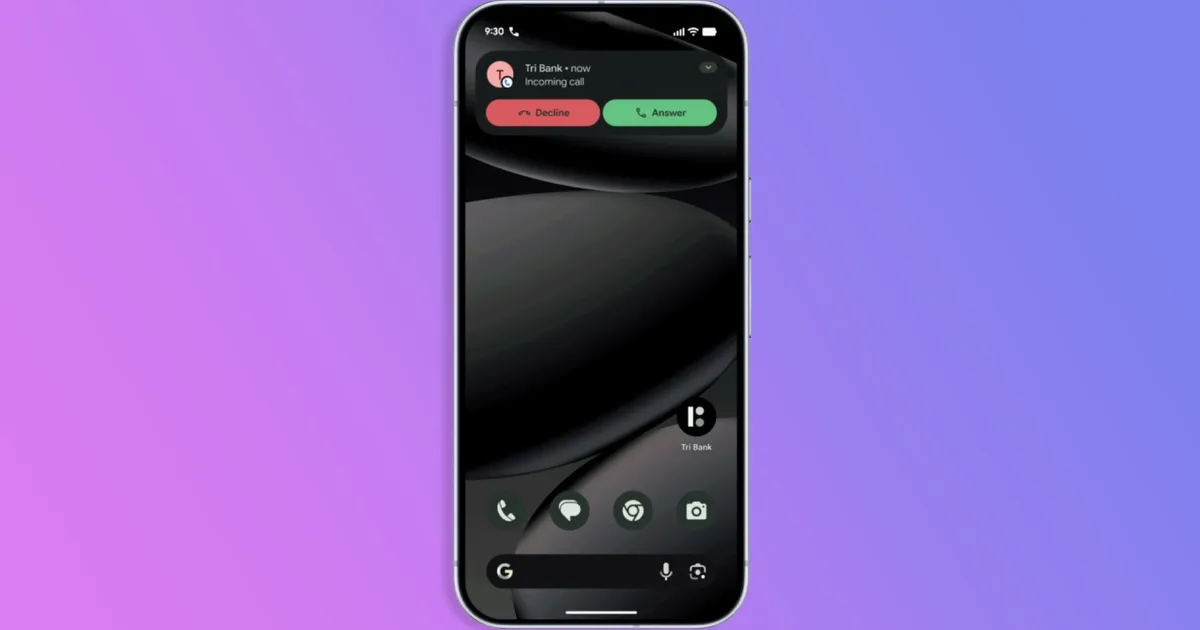
Verified Financial Calls: Android Now Hangs Up on Spoofed Scams
Google is turning the humble phone app into a frontline defense against fraud with a new verified financial calls feature. Phone spoofing, where scammers fake bank caller IDs using internet-based calling systems, is blamed for an estimated USD 950 million (approx. RM4,400,000,000) in losses every year. To counter this, Android will now check in real time with your bank’s official app whenever it claims to be calling you. If the app confirms the call, it goes through; if not, Android automatically hangs up before you even pick up. The system requires that you have a participating bank’s app installed and be signed in, and early partners include Revolut, Itaú, and Nubank, with more institutions expected to join. The rollout will reach devices running Android 11 and above in the coming weeks, making Android scam blocking far more proactive than simple spam call filters.
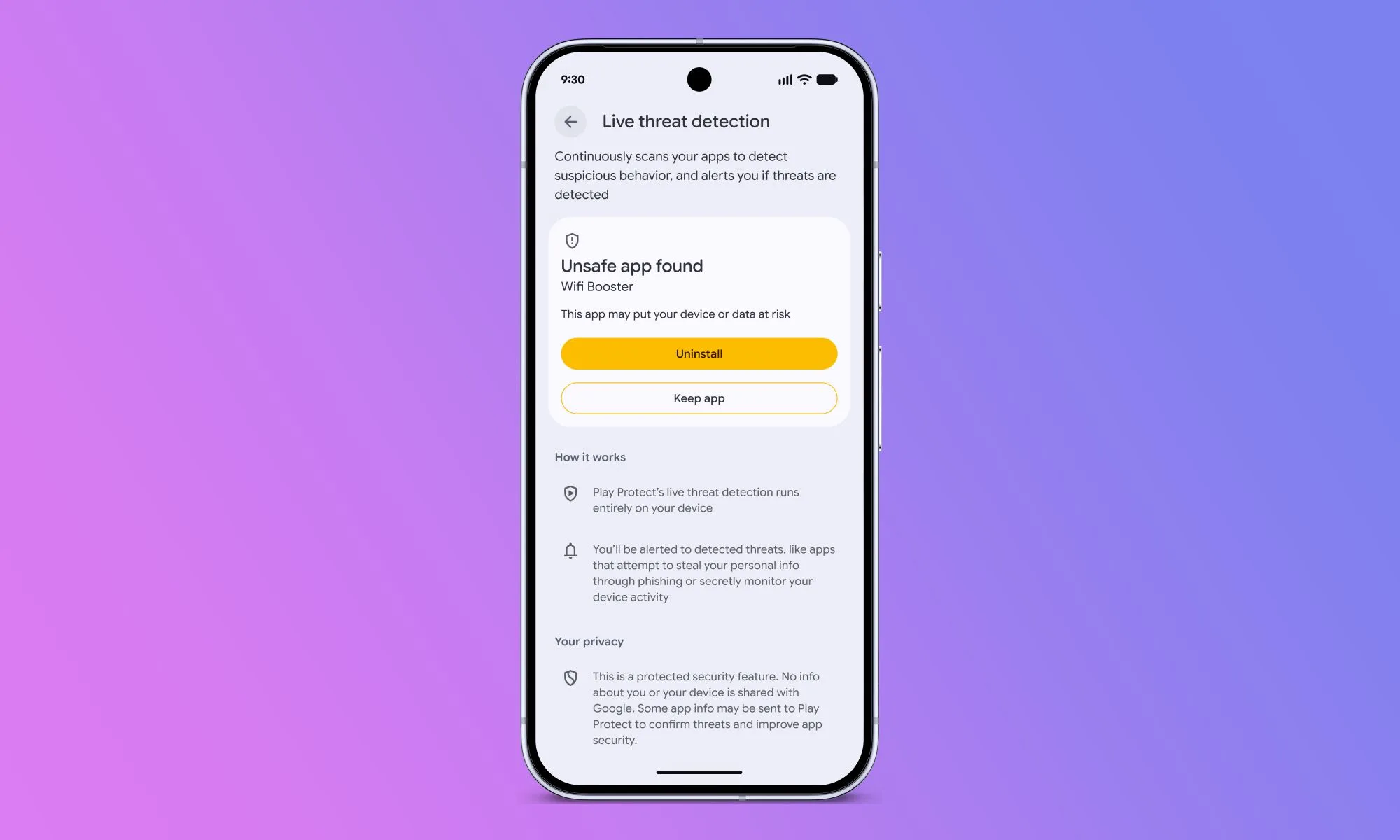
Live Threat Detection and OTP Shielding Raise the Bar on App Security
Verified calls are only one layer of Google’s new Android security features. Live Threat Detection, an on-device AI system, is being expanded to catch apps that quietly forward SMS messages or misuse accessibility permissions to overlay hidden content. A new dynamic signal monitoring capability goes further by watching for classic malware behavior, such as apps changing or hiding their icons and then launching in the background. Because threat rules can be updated as new attack patterns emerge, Android’s spoofed call detection and app defenses become more adaptive over time. To protect one-time passwords, Android will also automatically hide SMS OTPs from most apps for three hours, blocking malicious tools that try to intercept login codes. On top of that, Chrome on Android will be able to scan APK files for known malware before downloads complete, provided Safe Browsing is enabled.
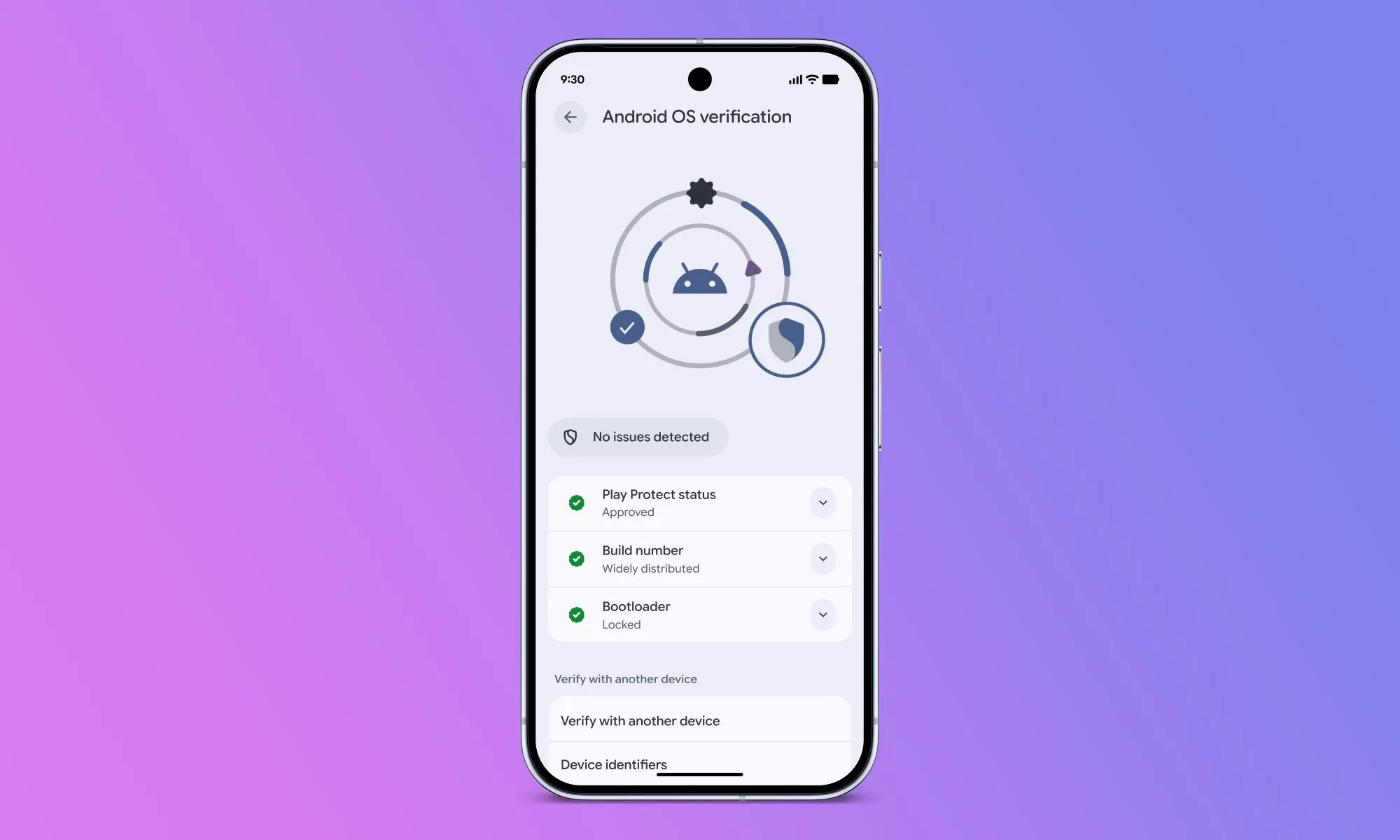
Advanced Protection, USB Defenses, and OS Verification for High-Risk Users
For people at higher risk of targeted attacks, Google is strengthening Android’s Advanced Protection mode. With Android 17, this mode will restrict accessibility service access only to apps explicitly flagged as accessibility tools, closing off a common avenue for screen-hijacking malware. It will also disable device-to-device unlocking and Chrome WebGPU support, while adding scam detection for chat notifications to flag suspicious messages in real time. Beyond that, USB protection is rolling out to devices on Android 16 and later, helping block unauthorized access over wired connections. Intrusion Logging, developed with civil society partners, is arriving on devices running the Android 16 December update and newer to provide forensic visibility into sophisticated attacks. Android 17 will additionally introduce Android OS verification so users can confirm they’re running an official build, plus a public, append-only ledger to cryptographically prove that Google’s production apps on Android are authentic.
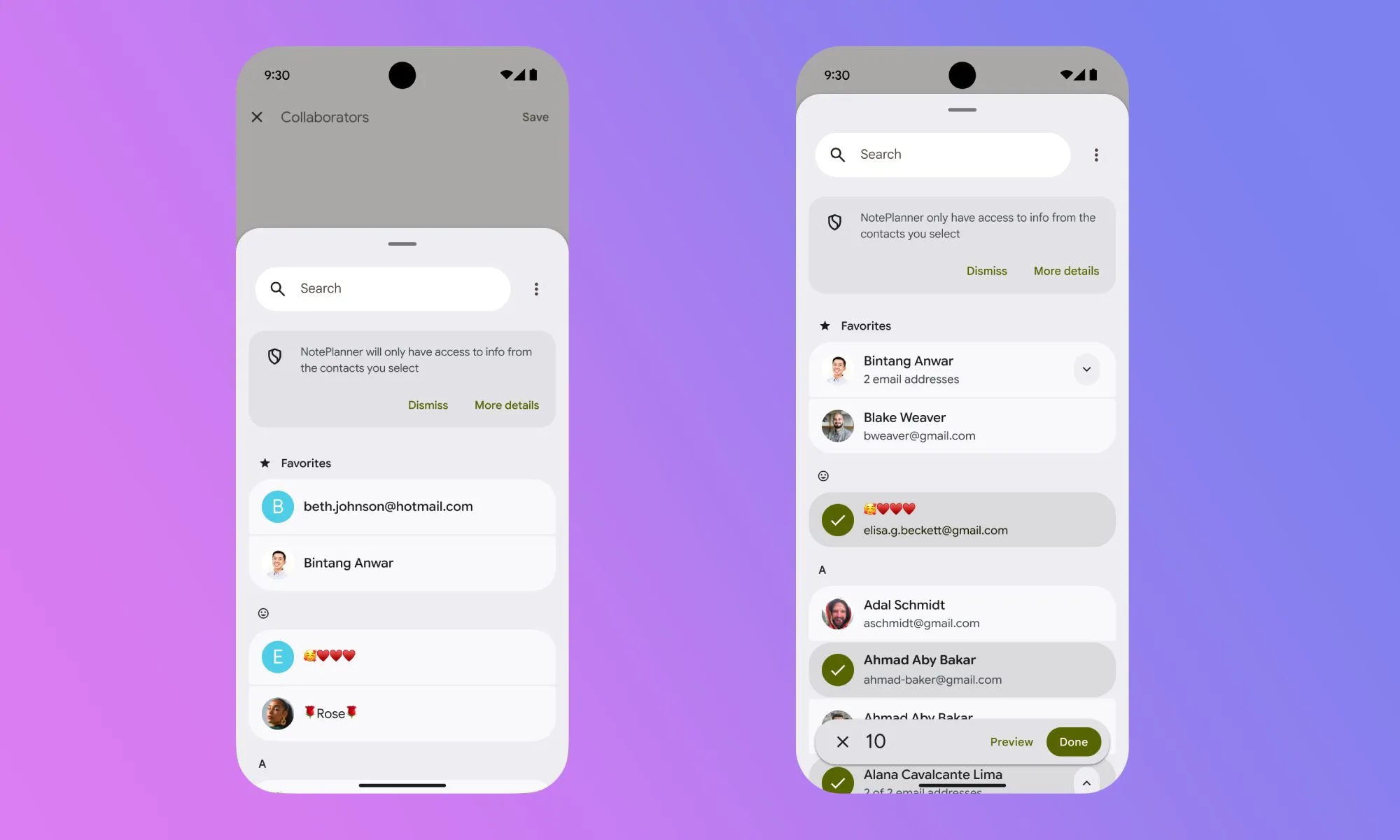
New Location and Contact Controls Put Data Sharing on a Short Leash
Android 17 is tackling location tracking privacy and data exposure with a tighter, more transparent permission model. A new location button lets you grant precise location to an app only while it’s open, automatically revoking access once you close it so there are no lingering background permissions. A persistent on-screen indicator appears whenever any app uses your location; tapping it reveals recent location access and offers a quick way to adjust permissions on the spot. A redesigned contact picker brings similar granularity to your address book: instead of handing over your entire contacts list, you can share only specific entries and limit which fields an app can see. Google says it will encourage developers to adopt both the temporary location button and the selective contact picker through Google Play policies, making app tracking prevention and fine-grained data sharing the default, not the exception.
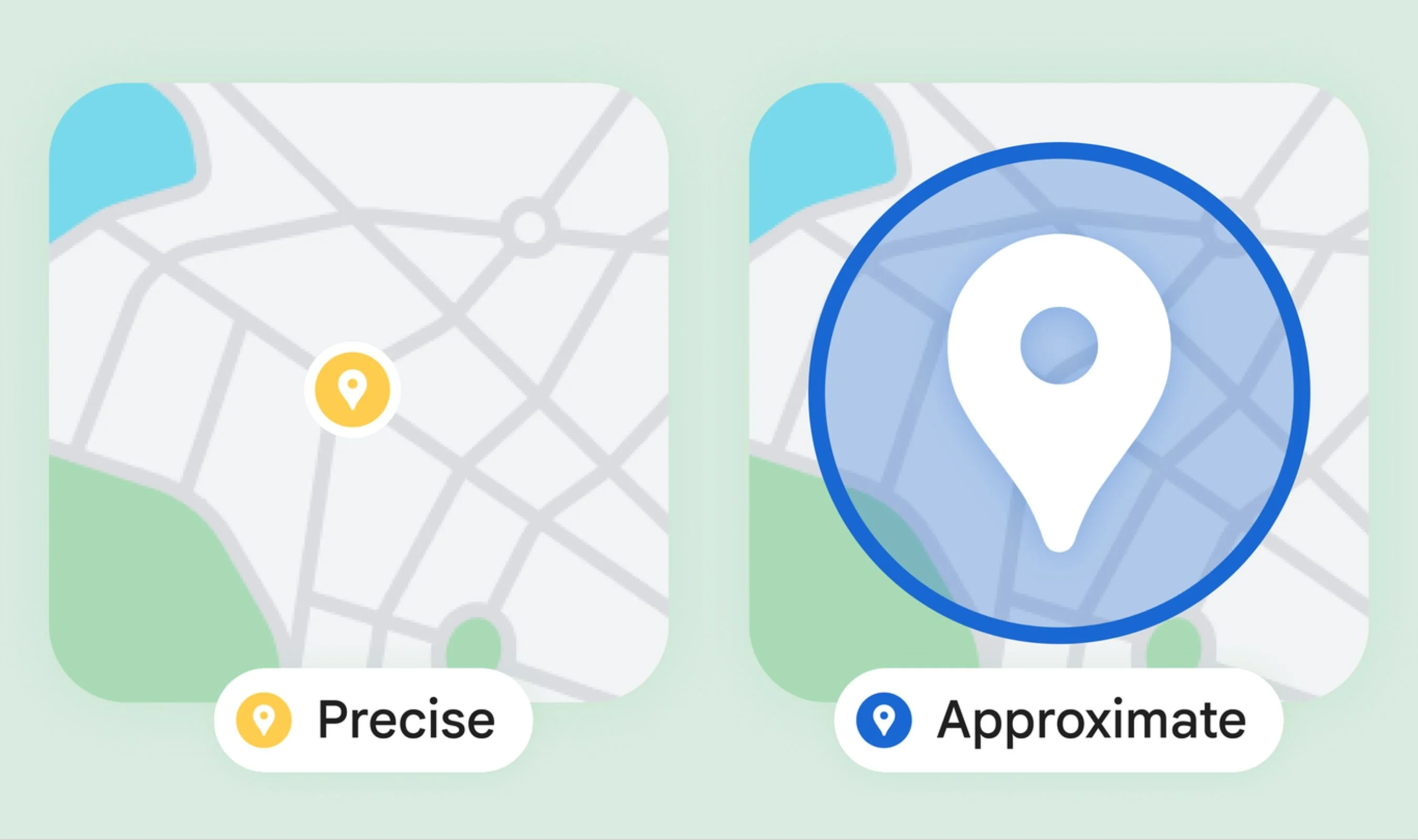
Chrome’s Approximate Location and Theft Protections Complete the Ecosystem
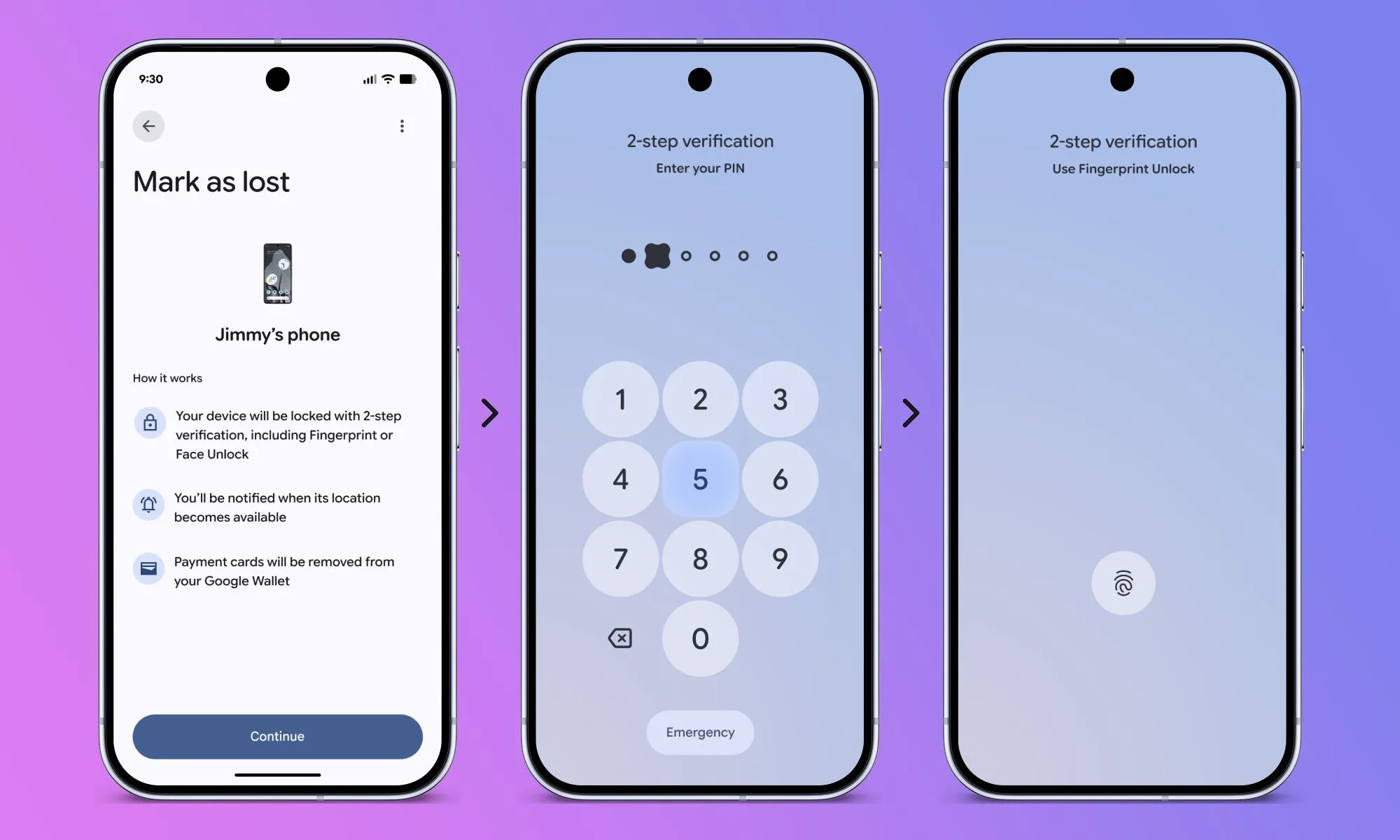
Google is extending Android’s privacy philosophy to the web and to physical device security. In Chrome on Android, websites now see a three-choice prompt when asking for location: precise, approximate, or deny. That means you can give a weather site neighborhood-level data while reserving exact GPS coordinates for services that genuinely need them, like navigation or deliveries. Google is also building new APIs so web developers can request approximate location by default and only escalate to precise when absolutely necessary. Meanwhile, Android 17’s theft protections aim to keep stolen phones locked down and recoverable. Remote Lock and Theft Detection Lock will be enabled by default on new and freshly reset devices, while the Mark as Lost tool will demand biometric authentication to unlock, hide Quick Settings, and block new Wi‑Fi and Bluetooth connections. Together, these changes link call verification, app control, and location privacy into a coherent security ecosystem.