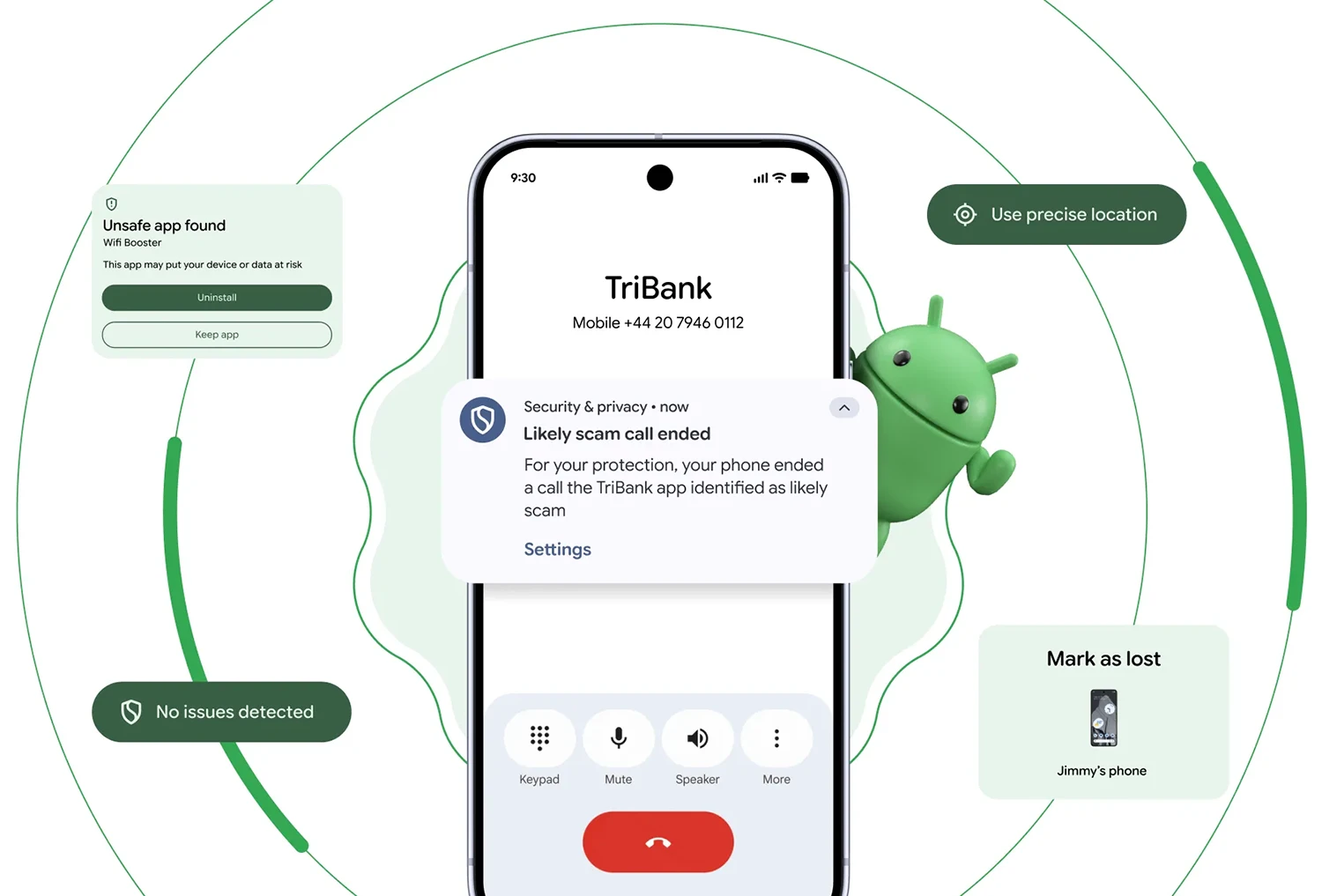
Verified Bank Calls Take Direct Aim at Phone Scam Rings
Android is building scam protection straight into the dialer with a new verified financial calls system designed to stop fraud before a conversation even starts. When a call appears to come from a bank or financial institution, Android cross‑checks it against the official banking app installed on the device. If the app confirms no call is in progress, Android automatically terminates the connection, stopping spoofed caller ID scams mid‑ring. Institutions can also mark specific numbers as inbound‑only, so any call claiming to originate from those lines is blocked on sight. This approach directly addresses losses driven by scammers who imitate bank hotlines, a pattern that authorities estimate has led to roughly USD 980 million (approx. RM4.6 billion) in annual losses worldwide. The feature is rolling out to Android 11 and newer phones in partnership with early adopters like Revolut, Itaú, and Nubank, with more banks to follow.
Beyond Find My Phone: Theft Protection Becomes Default and Biometric‑First
Android’s new phone theft prevention strategy goes far beyond simple location tracking. In Android 17, two cornerstone capabilities—Remote Lock and Theft Detection Lock—will be switched on by default after setup, reset, or upgrade, rather than relying on users to enable them manually. The updated Mark as lost feature inside Find Hub adds another critical safeguard: once a device is flagged as lost, biometric authentication is required to regain access. Even if someone has shoulder‑surfed your PIN or password, they still cannot unlock the device without your fingerprint or face. Mark as lost also hides the Quick Settings panel and blocks new Wi‑Fi or Bluetooth connections, making it significantly harder for thieves to disable connectivity, pair accessories, or tamper with system controls. Together, these layers turn a stolen Android phone into a far less valuable target—both in terms of resale and the sensitive data it contains.
AI App Monitoring Watches for Malware, SMS Forwarding, and Hidden Icons
Google is doubling down on AI app monitoring with a smarter Live Threat Detection system embedded directly into Android. This on‑device AI watches how apps behave rather than just what they claim to be. It can now flag suspicious behaviors like secretly forwarding SMS messages—a common tactic in hijacking one‑time passwords—or abusing accessibility overlays to capture inputs and screen content. A new capability called dynamic signal monitoring tracks app‑system interactions in real time, enabling Google to push updated detection rules rapidly as new malware techniques emerge. If an app hides its icon and then launches malicious background activity, Android 17’s dynamic monitoring is designed to spot and respond to that pattern. In parallel, Chrome on Android adds download‑time checks for APK files when Safe Browsing is enabled, blocking known malicious packages before they ever reach the installer, further shrinking the window for attackers.
On‑Device AI Isolation Keeps Security Protections Running When the Cloud Is Out
A key theme in Android’s new defenses is keeping critical security logic on the device itself, rather than depending on a constant cloud connection. Live Threat Detection runs locally, so AI app monitoring continues to analyze behavior even when the network is spotty or unavailable. This isolation makes Android scam protection and phone theft prevention more resilient; security decisions are not delayed by server round‑trips or outages. Advanced Protection mode further hardens the environment by blocking accessibility service access for apps that are not genuine accessibility tools, disabling device‑to‑device unlocking, and turning off Chrome WebGPU support in high‑risk scenarios. These hardening measures reduce the attack surface available to sophisticated malware. With USB protection and intrusion logging rolling out more widely, Android is evolving into a platform where core defenses are baked into the operating system and powered by on‑device intelligence, rather than bolted on as optional afterthoughts.
Why These Layers Matter as Phone Fraud and Theft Keep Rising
The combination of verified bank calls, AI app monitoring, and default‑on theft protections represents a shift from passive to active defense on mobile devices. Phone‑based fraud has grown increasingly sophisticated, with attackers blending spoofed caller IDs, malicious apps, SMS interception, and physical theft into multi‑stage schemes. Android’s response is to close gaps at each step: preventing impersonated calls from ever connecting, isolating and flagging apps that attempt to forward codes or hide themselves, and making stolen phones much harder to unlock or resell. On‑device AI isolation ensures these protections remain available even without connectivity, protecting users wherever they are. For everyday users, the impact is subtle by design—calls that never arrive, downloads that quietly fail, thieves who give up quickly—but collectively, these measures aim to reduce the success rate of scams and theft incidents that have become a global problem across mobile ecosystems.
