A Purpose-Built 802.11 Cyber Range for Practical Wi-Fi Security Training
Wi-Fi remains the primary gateway into enterprise networks, yet dedicated Wi-Fi security training environments have lagged behind broader network labs. Responding to this gap, researchers from the Norwegian University of Science and Technology and the University of the Aegean have released an open-source 802.11 cyber range prototype on GitHub. Unlike generic wireless testbeds that bundle Wi-Fi alongside Bluetooth, Zigbee, and cellular, this platform focuses exclusively on Wi-Fi attack and defense scenarios. The cyber range is designed as a realistic network security lab for exploring rogue access points, deauthentication attacks, WPA handshake weaknesses, and protocol-level flaws in 802.11 frame handling. By making the prototype publicly available, the team aims to lower barriers to Wi-Fi security training for students, self-learners, and corporate teams alike, providing a reproducible environment where practitioners can safely experiment with real tools and workflows they would encounter during assessments and incident response.
How the Software-Defined Wi-Fi Lab Works
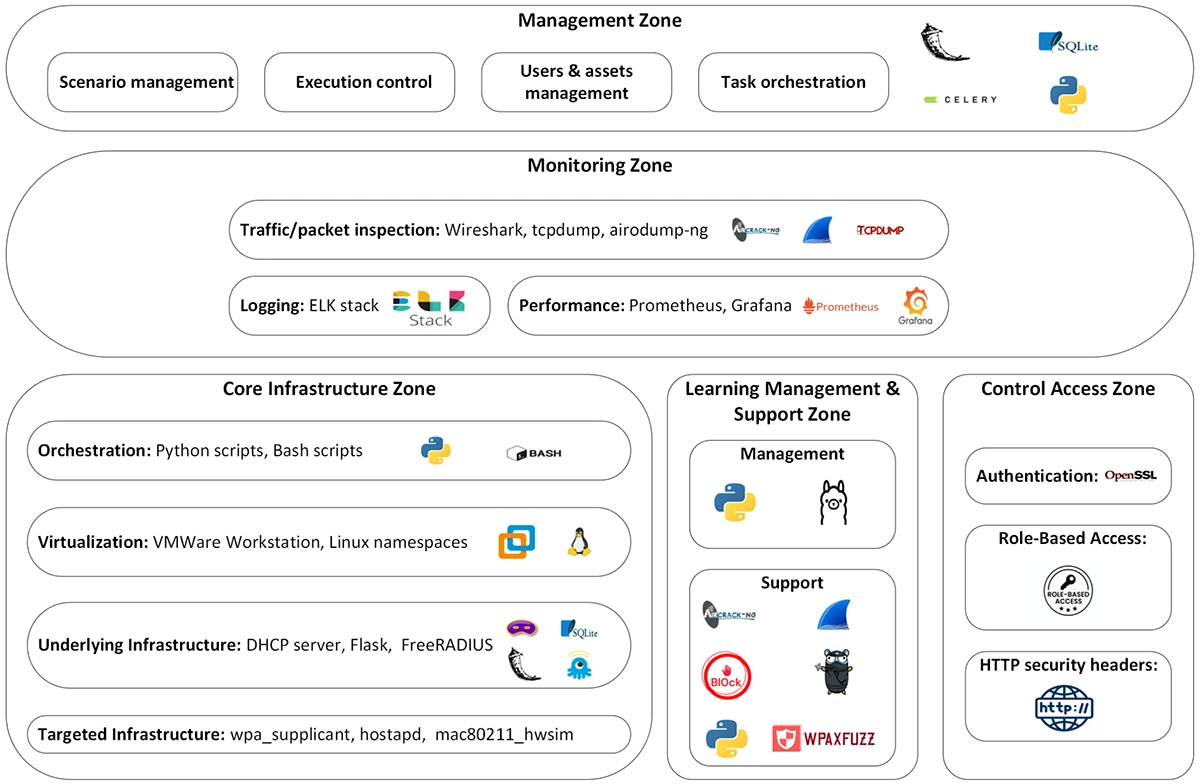
At the core of the platform is mac80211_hwsim, a Linux kernel module that emulates 802.11 radios entirely in software. Each simulated access point and client runs in its own Linux namespace, allowing many independent Wi-Fi nodes to coexist on a single host while behaving like separate physical devices. On top of this foundation, common user-space services recreate realistic network behavior: hostapd manages access points, wpa_supplicant acts as the client stack, dnsmasq delivers DHCP, and FreeRADIUS enables 802.1X/EAP for enterprise-style authentication scenarios. To support meaningful Wi-Fi security training, the range bundles open-source security tools widely used in the field. Aircrack-ng provides discovery and deauthentication capabilities, while Wireshark, tcpdump, and tshark handle packet capture and analysis. Two additional tools from the research group, WPAxFuzz and Bl0ck, extend the environment to cover WPA implementation fuzzing and block-acknowledgment-frame attacks against active 802.11 connections.
AI-Assisted Scenario Building for Instructors and Learners
Beyond the underlying network emulation, the cyber range emphasizes scenario-driven Wi-Fi security training. Instructors can create exercises through a web-based interface in two ways. They may select from predefined topology templates—covering, for example, multi-access-point networks or enterprise deployments with 802.1X—or describe the desired exercise in natural language. A locally hosted Llama model then converts that description into a structured scenario definition the platform can deploy. Each scenario is stored as a bundle of configuration files, shell scripts, and a topology manifest, making it easy to version, share, and reuse within courses or corporate training programs. This semi-automated approach reduces the friction of authoring complex Wi-Fi environments, such as multi-AP setups with authentication backends, which can be time-consuming to assemble manually. The result is a more agile network security lab where varied 802.11 cyber range exercises can be run frequently without overwhelming instructors.
Current Prototype Limits and Future Potential for Wi-Fi Security Education
The released GitHub prototype implements the core workflow for creating, storing, retrieving, and deploying Wi-Fi training scenarios, but it does not yet cover the full architecture envisioned by the researchers. Additional zones for detailed monitoring dashboards, role-based access control, and asynchronous orchestration remain outlined on paper and earmarked for future development. The authors also highlight intrinsic limitations of a software-only 802.11 cyber range: it cannot mimic radio interference, signal propagation, or hardware quirks that influence real-world Wi-Fi performance and security. Scalability is another open question, as the platform has not been evaluated with large numbers of concurrent learners, and formal learning outcomes are still to be studied. Even so, its modular design suggests a path toward integration with university courses, online learning platforms, and corporate training programs, offering a widely accessible starting point for structured, hands-on Wi-Fi security training.
Lowering the Barrier to Open-Source Wi-Fi Security Training
By centering exclusively on 802.11, the new cyber range complements existing open-source security tools and general-purpose cyber ranges, filling a longstanding gap for Wi-Fi specialists. Wireless security courses have traditionally leaned on lectures and limited lab exercises, often without realistic, repeatable environments to practice attacking and defending access points, clients, and authentication flows. This platform reframes Wi-Fi training as an iterative, experiment-driven process that can be run on commodity hardware using freely available software. For network engineers, penetration testers, and blue teams, the range provides a safe playground to rehearse Wi-Fi-centric workflows, from reconnaissance and deauthentication to packet analysis and protocol fuzzing. For educators, the ability to quickly build and redeploy tailored 802.11 scenarios promises more engaging course designs. As Wi-Fi 6 and Wi-Fi 7 deployments expand the attack surface, a dedicated, open-source 802.11 cyber range offers a timely foundation for modern Wi-Fi security training.