When Convenience Becomes an Attack Surface in Messaging Apps
Modern messaging apps compete on convenience: rich link previews, instant media playback, AI-powered cards, and seamless file sharing. But every time your chat app automatically loads a preview, opens a document, or follows a link, it quietly asks your phone’s operating system to do work on your behalf. That background activity is exactly where many messaging app security problems begin. A preview that pulls in remote content, or a file that the app mislabels, can give attackers a subtle way to influence what your device does next. This is why messaging app security is not just about encryption or passwords. It is about how safely apps handle the routine actions you barely notice—like viewing a Reel or tapping a “harmless” attachment. Understanding how these innocent features can be twisted into attack vectors is the first step to protecting your chats and your device.
WhatsApp Vulnerabilities: Reels Previews and File Spoofing Attacks
Recent WhatsApp vulnerability disclosures highlight how rich previews and file handling can undermine user trust. In one case, AI-generated rich responses for Instagram Reels did not properly verify the source URL. A crafted message could cause a device to load media from an attacker-controlled URL and potentially trigger custom URL schemes. On their own, such bugs may not be catastrophic, but they act as building blocks that other flaws in browsers, apps, or the operating system can chain into serious attacks. A second weakness in WhatsApp for Windows involved classic file spoofing attacks. By slipping hidden NUL characters into filenames, attackers could make Windows treat an attachment as a different file type than WhatsApp displayed, luring users into running something more dangerous than expected. Both issues have been patched, but they show how rich previews and attachment labels can quietly erode messaging app security.
Signal’s New Security Features for Phishing Detection
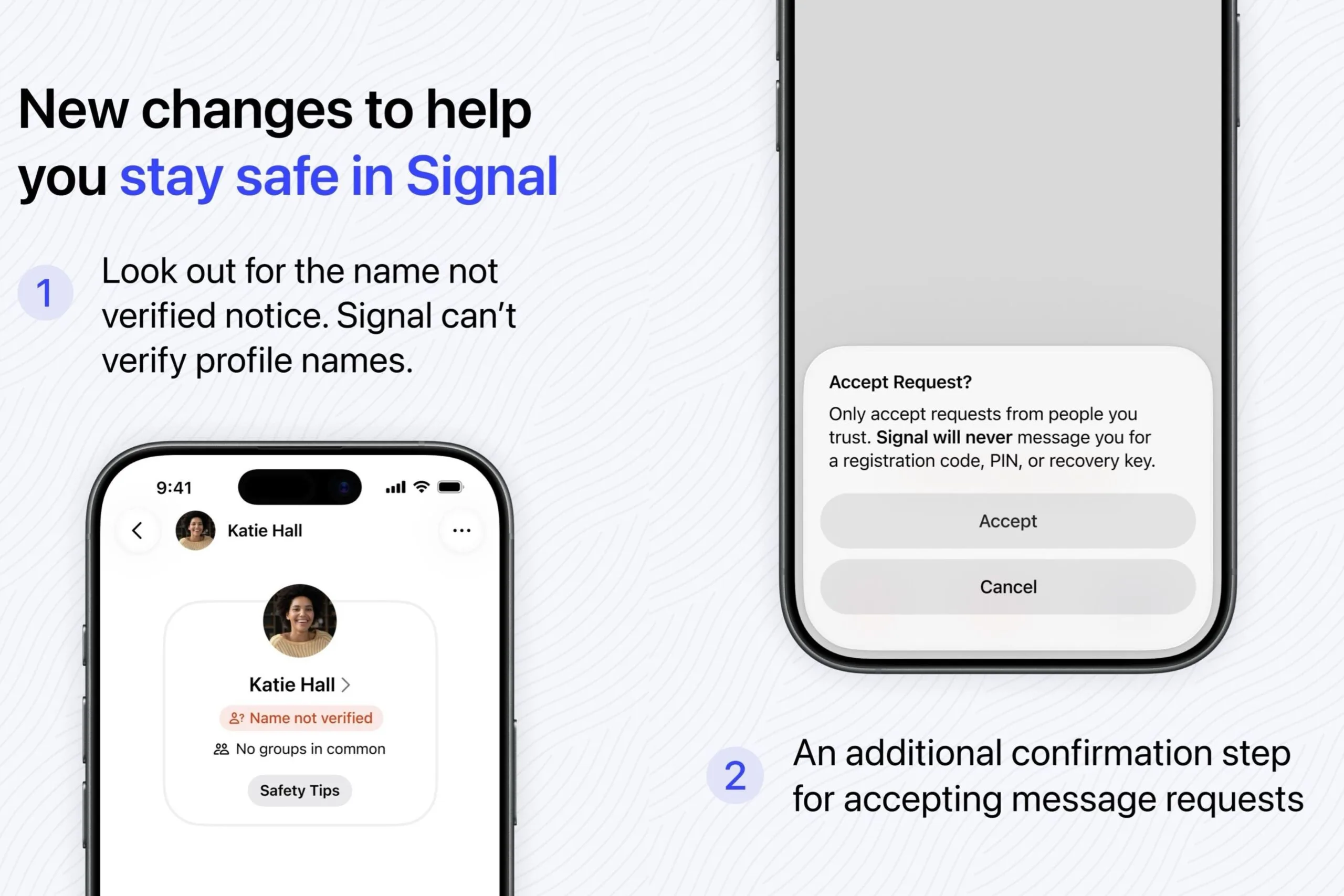
Signal is responding to escalating phishing and social engineering attempts with new in-app protections. After targeted phishing campaigns against officials and journalists, the app introduced clearer, built-in guidance to help users spot scams. A key addition is the “name not verified” notice, reminding people that Signal cannot truly verify the profile names users choose. This makes it harder for scammers impersonating trusted contacts or the app itself to seem legitimate. Signal has also added an extra confirmation step for message requests, nudging users to only accept chats from people they actually know. On top of that, the interface now highlights red flags such as vague opening messages, suspicious links, and unsolicited financial advice. Crucially, Signal reminds users that it will never ask for their PIN, registration code, or recovery key, reinforcing good habits and strengthening phishing detection right where conversations happen.
How to Protect Yourself from Hidden Threats in Everyday Chats
Even with active patching and new Signal security features, users remain the last line of defense. Start by treating messaging apps as critical software, not disposable tools: keep WhatsApp and Signal updated on every device, including desktops. Be cautious with rich previews; do not assume that a video, Reel, or link card is safe just because it appears inside a trusted app. For attachments, distrust mismatched details—if a file looks like a document but behaves like an app, close it immediately. When you receive message requests, assume unknown senders could be running social engineering plays: ignore vague introductions, pressure tactics, or any request for codes or keys. Finally, integrate messaging app security into your broader digital habits: use endpoint protection on computers, educate family or colleagues about file spoofing attacks and phishing detection, and regularly review privacy and security settings inside each app.

