Android 17’s New Privacy Defaults: Protection Without Prompts
Android 17 privacy changes reshape how apps can reach into your data, and they do it without relying on you to tweak a single setting. For apps targeting the new API level 37, three defaults now apply automatically: a system-level contacts picker, a new local network access control, and a built‑in delay on SMS one-time passwords (OTPs). Together, they clamp down on app permissions that previously granted broad, often invisible access to your address book, home network, and incoming messages. Crucially, these protections are on by default and mostly silent. You won’t see a pop‑up asking you to opt in, and many apps won’t even show new prompts if they adopt Google’s recommended pickers and APIs. Users can still grant broader permissions when a feature legitimately needs them, but the baseline now assumes your contacts, local devices, and SMS security stay locked down unless you say otherwise.
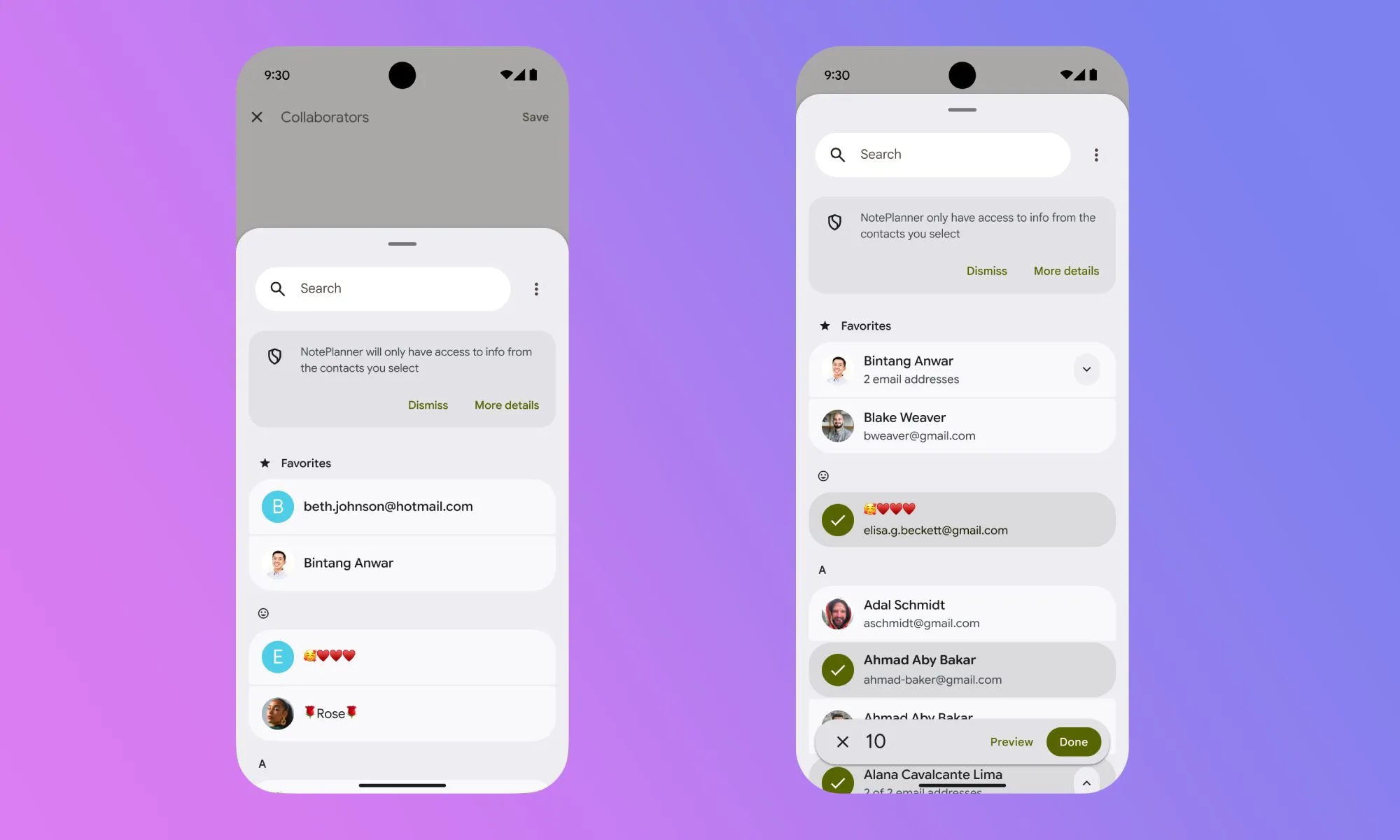
Contacts Picker: No More Handing Over Your Entire Address Book
The new contacts picker feature replaces the old all‑or‑nothing contacts permission that exposed your full address book. Previously, when an app requested contact access, saying yes meant sharing every name, number, and email in one sweep. Android 17 changes this with a system picker that works much like the existing photo picker: the app asks Android for a contact, Android shows you your list, and you choose exactly which entry or entries to share. Access is session‑based and temporary. Once you finish the task—say, inviting a friend or filling in a phone field—the app’s window into that contact closes. Apps can also request only specific data fields, such as a phone number but not an email, reducing unnecessary data exposure. This finer-grained approach to app permissions means a simple notes or to‑do app no longer needs blanket READ_CONTACTS just to pull in a single person from your list.
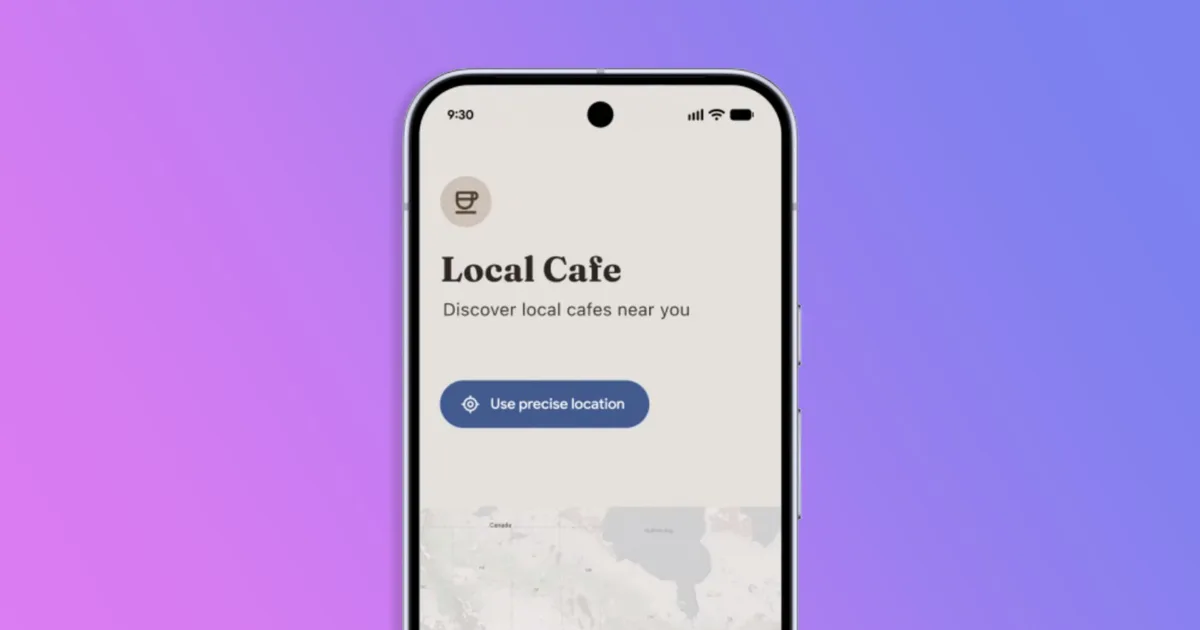
Network Access Control: Blocking Silent Scans of Your Home Network
Android 17’s new network access control tackles a quieter but serious problem: apps silently probing your local network. Historically, any app on your phone could see devices on your Wi‑Fi, sniff nearby access points, and build a unique “network fingerprint” without ever touching the internet. That fingerprint can help track you across services even when traditional tracking is blocked. To stop this, Android 17 introduces the ACCESS_LOCAL_NETWORK runtime permission. Apps targeting API level 37 must now either use a system device picker or explicitly request this permission before discovering or connecting to devices on your local area network. Everyday users may never see a prompt if their apps rely on the picker, which handles connections without exposing the whole LAN. Apps that truly need persistent communication—like smart home controllers or local media servers—can still request permission. Meanwhile, background utilities and trackers that once scanned your network by default simply lose that capability unless you consciously allow it.
SMS OTP Delay: Friction Against One‑Tap Code Theft
Android 17 also tightens SMS security by attacking a common loophole in app permissions. Many apps historically requested broad SMS read access, then quietly intercepted one‑time passwords the instant they arrived. That made two-factor authentication over SMS less secure than most users realized. Now, for apps targeting API level 37, Android 17 adds a three‑hour delay before most third‑party apps can programmatically read SMS messages that contain OTPs. Your default SMS app, assistant apps, verified companion apps, and those using official APIs like SMS Retriever or SMS User Consent are exempt, so normal SMS security flows still work as intended. The change primarily disrupts apps that were passively vacuuming up incoming codes alongside other messages. By the time the delay expires, OTPs are typically invalid, shutting down a major path for silent interception. Combined with other Android 17 privacy measures, this default-on SMS security tweak raises the baseline protection for people who still rely on texted verification codes.
How These Defaults Affect Your Daily Apps—and Your Choices
For most people, Android 17 privacy changes will feel invisible until an app’s behavior shifts. You might notice a contacts picker when sharing someone’s details, or a new prompt if a smart home app genuinely needs local network access. SMS security changes will largely stay behind the scenes unless you used apps that auto-filled codes by exploiting broad SMS permissions. Importantly, none of these features remove your ability to say yes when you truly need an app to see more. You can still grant app permissions manually in settings or accept runtime prompts for contacts, network access control, or SMS-related features. What’s different is the starting point: Android now assumes your contacts, nearby devices, and OTPs are private by default. Developers are encouraged—and in some cases required—to adopt the new pickers and APIs, aligning app behavior with stronger privacy norms while keeping critical features, like banking logins or device pairing, fully functional when you explicitly approve them.